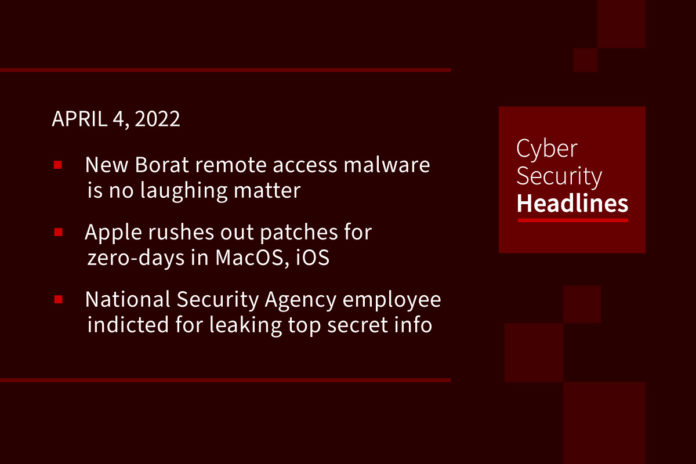
New Borat remote access malware is no laughing matter
A new remote access trojan named Borat has appeared on darknet markets, offering easy-to-use features to conduct DDoS attacks, UAC bypass, and ransomware deployment. As a RAT, Borat enables remote threat actors to take complete control of their victim’s mouse and keyboard, access files, network points, and hide any signs of their presence. The malware lets its operators choose their compilation options to create small payloads that feature precisely what they need for highly tailored attacks. Borat was analyzed by researchers at Cyble, who spotted it in the wild and sampled the malware for a technical study that revealed its functionality. It is unclear if the Borat RAT is sold or freely shared among cybercriminals, but Cycle says it comes in the form of a package that includes a builder, the malware’s modules, and a server certificate.
Apple rushes out patches for zero-days in MacOS, iOS
Apple rushed out patches for two zero-days affecting macOS and iOS Thursday, both of which are likely under active exploitation and could allow a threat actor to disrupt or access kernel activity. Apple released separate security updates for the bugs – a vulnerability affecting both macOS and iOS tracked as CVE-2022-22675 and a macOS flaw tracked as CVE-2022-22674. Their discovery was attributed to an anonymous researcher. CVE-2022-22675 – found in the AppleAVD component present in both macOS and iOS – could allow an application to execute arbitrary code with kernel privileges, according to the advisory.
National Security Agency employee indicted for ‘leaking top secret info’
The United States Department of Justice (DoJ) has accused an NSA employee of sharing top-secret national security information with an unnamed person who worked in the private sector. According to a DoJ announcement and the indictment, an NSA staffer named Mark Unkenholz “held a TOP SECRET/Sensitive Compartmented Information (SCI) clearance and had lawful access to classified information relating to the national defense.” The indictment alleges that on 13 occasions between 2018 and 2020, Unkenholz shared some of that information with a woman identified only as “RF” who was not entitled to see it. The indictment and announcement allege Unkenholz used his personal email address to send material to RF.
Trezor wallets hacked? Don’t be duped by phishing attack email
Owners of hardware Trezor cryptocurrency wallets should be on their guard after an email was sent out by thieves attempting to dupe them into downloading new software to their devices. The emails claim that Trezor, which has been making physical USB-connected devices to protect the cryptocurrency and tokens of users since 2014, “experienced a security incident” yesterday that breached the data of 106.856 of its customers.
Thanks to our episode sponsor, Code42

Code42 Incydr is an Insider Risk Management SaaS that provides a comprehensive understanding of your data exposure and shows which activities require security intervention. Learn more at Code42.com/showme.
China-linked APT Deep Panda employs new Fire Chili Windows rootkit against VMware servers
Researchers from Fortinet have observed the Chinese APT group Deep Panda exploiting a Log4Shell exploit to compromise VMware Horizon servers and deploy previously undetected Fire Chili rootkit. The experts observed opportunistic attacks against organizations in several countries and various sectors. The targeted organizations operate in the financial, academic, cosmetics, and travel industries. The kernel rootkit employed by the threat actors is signed with a stolen digital certificate, which is the same certificate used by the Winnti cyberespionage group. The group “Deep Panda” is a well-known APT that during the past years has targeted defense, financial and other industries in the US. The group employed many zero-day exploits to spread different malware, including the popular Poison Ivy.
Upstart crime site woos Raid Forums orphans
A new crime site for hackers is positioning itself as an alternative to Raid Forums, a popular watering hole for threat actors before it was mysteriously taken down in February. The new site, Breach Forums, was launched by an old Raid Forum character, “pompompurin,” according to a blog post this week by Flashpoint, a threat intelligence company. In the welcoming thread to the forum, pompompurin stated that the new hacker community was being created as an alternative to Raid Forums. The forum was one of the most popular illicit online forums on the public internet and was notorious for its high-profile database leaks and offerings. As a side note, the name pompompurin pops up regularly, including a recent hack of the FBI email system and the Robinhood breach last November.
(CSOOnline and PrivacyAffairs)
Companies going to greater lengths to hire cybersecurity staff
According to an article in Dark Reading, employers are desperately seeking to fill cybersecurity positions. The number of available cybersecurity jobs coupled with accelerated attrition due to the Great Resignation has led to companies offering ridiculously high salaries, a bevy of benefits, and free training and certifications to woo candidates. Even so, the candidate pool is limited. Employers are exploring ways to help applicants fill in the gaps in their experience so that they can be hired. “The No. 1 thing anyone interested in cybersecurity careers should do is apply,” says Justine Fox, principal product manager, technical, at NuData Security, a Mastercard company. “There is no faster way to learn the role’s required skills than in the role. Whether you are self-taught or formally educated, I encourage folks to apply.” Mitch Ashley, principal at Techstrong Research, suggests cyber leaders must “widen the net” to bring in “talents beyond only traditional cybersecurity domains,” he adds, and managers “must think more like software leaders and less like network engineers.”
Cyberattackers target UPS backup power devices in mission-critical environments
The uninterruptible power supply (UPS) provides battery backup power during power surges and outages and are often found in mission-critical environments, safeguarding critical infrastructure installations and important computer systems and IT equipment. CISA and the Department of Energy, warned that threat actors are going after internet-connected versions of UPS via default usernames and passwords, as well as vulnerabilities like the TLStorm bugs disclosed earlier this month.