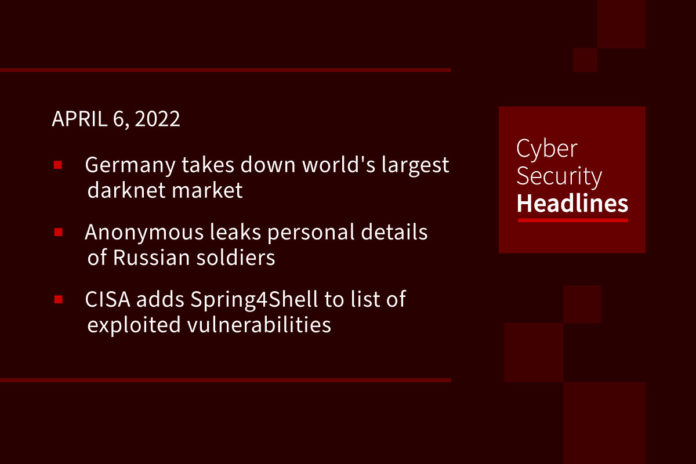
Germany takes down world’s largest darknet market
German police have seized the servers of Hydra Market, the most prominent Russian darknet platform known for laundering money and selling drugs, stolen databases, forged documents, and hacking for hire services. The police were also able to seize 543 bitcoins worth a little over $25 million. Authorities say Hydra Market had roughly 19,000 registered sellers who served at least 17 million customers with a turnover of $1.35 billion in 2020, making it the largest darknet market in the world.
Anonymous leaks personal details of Russian soldiers
Personal details of roughly 120,000 Russian soldiers were leaked by the Anonymous hacking group who blames Russia for its aggression toward Ukraine. Leaked details include names, dates of birth, home addresses, and passport numbers, all of which were tagged with the phrase, “all soldiers taking part in the Ukraine war should be subjected to a war crime tribunal.” The data release comes after Ukraine’s president Zelensky publicly condemned Russian missile strikes on Bucha which killed hundreds of innocent civilians. While some are applauding the move by Anonymous, others are criticizing the group for punishing innocent soldiers who are simply carrying out their president’s orders.
CISA adds Spring4Shell to list of exploited vulnerabilities
On Monday, the US Cybersecurity and Infrastructure Agency (CISA) added the Spring4Shell remote code execution flaw to their Known Exploited Vulnerabilities Catalog. The critical bug, which was unveiled last week, targets the Spring Framework which provides tools and utilities for Java-based applications. Spring4Shell is not expected to be as impactful as Log4Shell due to being more difficult to exploit. Nonetheless, researchers at Check Point indicate that roughly one in six organizations worldwide who are vulnerable to Spring4Shell have already been targeted by threat actors. Additionally, Microsoft confirmed that it is tracking some Spring4Shell exploit attempts across its cloud services. However, so far, there are no known successful exploitations. The vendor has addressed the issue with its release of Spring Framework versions 5.3.18 and 5.2.2, as well as Spring Boot 2.5.12.
(Help Net Security and Bleeping Computer and Bleeping Computer)
CashApp says ex-employee stole customer stock trading data
On Tuesday, stock trading platform CashApp, which is a subsidiary of Jack Dorsey’s Block (formerly Square), disclosed a breach of US brokerage account data. Allegedly, a former employee stole data including account numbers, full names, and portfolio holding info. Although it is not clear how many accounts were impacted, an SEC filing indicates the company is issuing breach warnings to roughly 8.2 million current and former customers. The company said, “While this employee had regular access to these reports as part of their past job responsibilities, in this instance these reports were accessed without permission after their employment ended.” The company indicated that they have remediated the issues and are continuing to strengthen their administrative and technical controls.
Thanks to our episode sponsor, Code42

In fact, the Code42 Annual Data Exposure Report revealed there’s a 1 in 3 chance that your company will lose IP when an employee quits. To learn more about stopping data leaks with Insider Risk Management visit Code42.com/showme.
Russian ‘war crime’ phishing campaign unsuccessful so far
On Tuesday, a top Ukrainian cybersecurity official said that phishing attempts on Ukrainian targets in late March, which contained documents appearing to contain information about Russian “war criminals,” were not successful. The files attachments were detected as malicious and forwarded to Ukraine’s Computer Emergency Response Team (CERT-UA) who attributed the campaign to a Russian hacking group dubbed “Armageddon.” CERT-UA issued a separate notice which linked attacks targeting government agencies within the European Union, at roughly the same time, to the same hacker group.
GitHub now scans for secret leaks in developer workflows
On Monday, GitHub announced that its Advanced Security suite has been upgraded with a new push protection feature which will scan for “highly identifiable patterns” of potential secret leaks. In addition, the new tool will check over 100 different token types including those issued by Alibaba Cloud, Amazon, AWS, Azure, npm, Slack, and Stripe. The new feature is an optional check for developers, and if enabled, will block a push if it detects a secret leak pattern. According to the company, there has been a low false-positive rate during testing.
(ZDNet)
Microsoft expands its bug bounty program
Microsoft has announced that, starting yesterday, Exchange, SharePoint, and Skype for Business on-premises are now part of their bug bounty program. Security researchers who find and report related vulnerabilities are eligible for awards ranging from $500 up to $26,000.The company says, “Higher awards are possible, at Microsoft’s sole discretion, based on the severity and impact of the vulnerability and the quality of the submission.”
49% of small medical practices lack a cyberattack response plan
According to a survey from Software Advice Sophisticated, cyberattacks are crippling healthcare providers by posing a threat to core functions and patient privacy. Survey findings reveal that 23% of small practices have experienced a data breach, and 46% of these breaches were caused by avoidable human error. Part of the problem could be that 42% of small practices and 25% of large practices spent no more than two hours on IT security and data privacy training in 2021. Alarmingly, 20% of small practices didn’t know if they had a formal cybersecurity response plan while 49% indicated that they definitely did not.