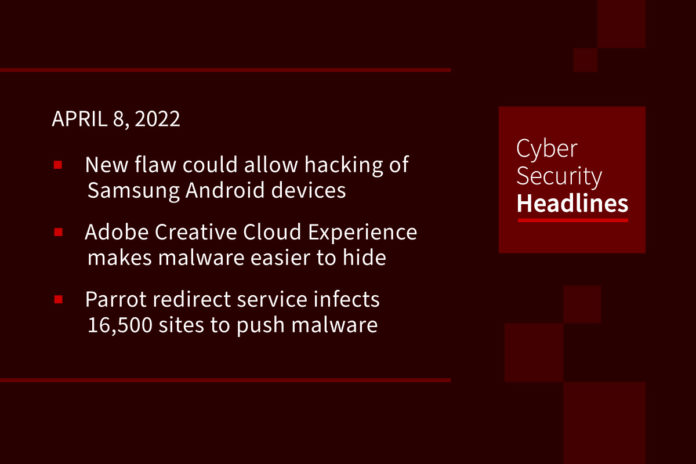
Newly discovered flaw could allow hacking of Samsung Android devices
Researchers from mobile cybersecurity firm Kryptowire have discovered a vulnerability that resides in a pre-installed Phone app that executes with system privileges on Samsung devices. Tracked as CVE-2022-22292, in Android 9, 10, 11, and 12 devices, the vulnerability could give attackers the ability to initiate a factory reset (i.e., deleting all user data), make phone calls (including to emergency numbers such as 911), install/uninstall apps, weaken HTTPS security by installing arbitrary root certificates, all from untrusted apps running in the background and without end-user approval.”
Adobe Creative Cloud Experience makes malware easier to hide
Experience is a service installed via the Creative Cloud installer for Windows that includes a Node.js executable that’s useable as part of an attack chain. Security researcher Michael Taggart recently demonstrated that the node.exe instance accompanying Adobe’s service could be abused by writing a simple proof-of-concept JavaScript file that spawns the Windows Calculator app, and that can “run any JavaScript you point it to.” Security researchers commenting on Taggart’s finding said they’d been under the impression the bundled Node runtime would only execute files signed by Adobe, but evidently that’s not the case.
Parrot redirect service infects 16,500 sites to push malware
A new traffic direction system (TDS) called Parrot is relying on servers that host 16,500 websites of universities, local governments, adult content platforms, and personal blogs, in order to redirect potential victims matching a specific profile (location, language, operating system, browser) to online resources such as phishing and malware-dropping sites. Parrot TDS was discovered by threat analysts at Avast, who report that it’s currently used for a campaign called FakeUpdate, which delivers remote access trojans (RATs) via fake browser update notices. As Avast details in the report, the particular campaign’s user profile and filtering are so fine-tuned that the malicious actors can target a specific person from thousands of redirected users. Most of the users targeted by these malicious redirections were in Brazil, India, the United States, Singapore, and Indonesia.
New FFDroider malware steals Facebook, Instagram, Twitter accounts
This new information stealer steals credentials and cookies stored in browsers to hijack victims’ social media accounts. Researchers at Zscaler have been tracking its spread and published a detailed technical analysis yesterday based on recent samples. FFDroider is spread through software cracks, free software, games, and other files downloaded from torrent sites. When installing these downloads, FFDroider will also be installed, but disguised as the Telegram desktop app to evade detection. Once launched, the malware will create a Windows registry key named “FFDroider,” which led to the naming of this new malware.
Thanks to our episode sponsor, Code42

Code42 Incydr is an Insider Risk Management SaaS that provides a comprehensive understanding of your data exposure and shows which activities require security intervention. Learn more at Code42.com/showme.
Israeli officials catfished by Bearded Barbie
AridViper, also known as APT-C-23, is a politically-driven APT group active in the Middle East. In the past, it has conducted spear-phishing attacks against Palestinian law enforcement, military, and educational establishments, as well as the Israel Security Agency (ISA). In February, Cisco Talos researchers uncovered AridViper attacks against activists associated with the Israel-Palestine conflict. On Thursday, Cybereason’s Nocturnus Research Team published new findings on the APT’s latest activities. Dubbed “Operation Bearded Barbie,” the latest campaign targets “carefully chosen” Israeli individuals to compromise their PCs and mobile devices, spy on their activities, and steal sensitive data. The researchers say the APT-C-23 group, alongside MoleRATs, are subset APTs of the Hamas cyberwarfare division and are working to benefit the Palestinian political group.
(ZDNet)
Zoom awards $1.8 million in bug bounty rewards over 2021
Zoom has awarded $1.8 million to researchers who submitted bug bounty reports over 2021. Recent updates to the program include extending the bug bounty reward range on offer, with up to $50,000 per report for the most severe vulnerabilities and $250 for low-hanging fruit. The company also launched a public Vulnerability Disclosure Program (VDP) and a VIP bug bounty program for licensed software. They attribute the increase in payments to the explosion of usage of Zoom by work-from-home employees paired with a shortage of available talent to hire.
(ZDNet)
Suspected Chinese hackers are targeting India’s power grid
According to a report by Recorded Future, researchers have observed “likely” network intrusions of at least seven state centers that carry out real-time grid control and electricity dispatcht. They state this was the work of hackers “likely affiliated with the Chinese government.” Although Researchers weren’t able to pinpoint the initial vector for how the malware got into the networks they believe Hackers likely gained access to the dispatch centers by compromising internet-facing camera devices, and using them as a command & control center.
Amazon secures rockets for broadband project
Over the next five years, three new heavy-lift rockets will put thousands of satellites into low earth orbit as part of Amazon’s Project Kuiper. The project aims to provide broadband connections using a constellation of 3,236 satellites. Rival Starlink is said to have more than 2,300 satellites in orbit already. The rockets will be made by Arianespace, Blue Origin – which was founded by Amazon owner Jeff Bezos – and United Launch Alliance. Amazon says Project Kuiper aims to provide high-speed, low-latency broadband to customers including households, businesses, government agencies, disaster relief operations, mobile operators, and other organizations “working in places without reliable internet connectivity”. Like Elon Musk’s Starlink, users will connect to the internet via a terminal that communicates with the satellites. Amazon says its experience in shipping and making products like Echo and Kindle will be useful in producing and distributing these.
(BBC News)