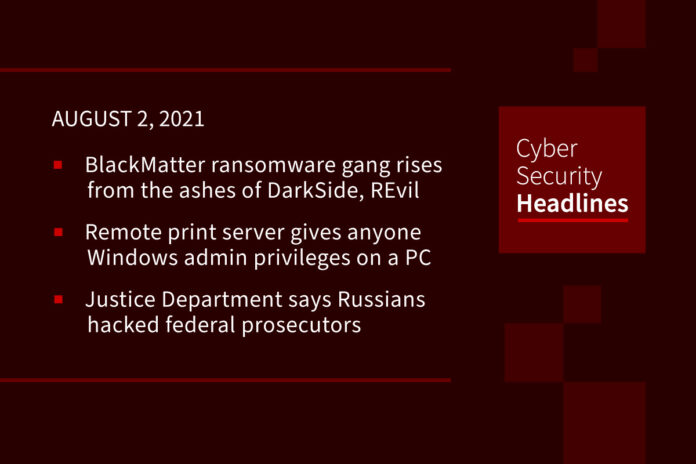
BlackMatter ransomware gang rises from the ashes of DarkSide, REvil
Adding to a story we brought you on Friday, a new ransomware gang named BlackMatter is purchasing access to corporate networks while claiming to include the best features from the notorious and now-defunct REvil and DarkSide operations. They stated they are willing to spend between $3,000 and $100,000 per network that had revenue of $100 million or more, with between 500-15,000 devices, and untargeted by other threat actors. They also state they will not target hospitals, critical infrastructure facilities, oil and gas, defense, non-profit companies or government sectors. Similarities in web sites and other discovered information indicate that BlackMatter has recruited or was created by threat actors that were previously with the DarkSide and the REvil ransomware operations.
Remote print server gives anyone Windows admin privileges on a PC
A researcher has created a remote print server that allows any Windows user with limited privileges to gain complete control over a device simply by installing a print driver. This follows on the heels of the zero-day Windows print spooler vulnerability known as PrintNightmare. Microsoft released a security update for this but researchers figured out ways to bypass the patch. This new method effectively allows anyone, including threat actors, to get administrative privileges simply by installing the remote print driver. Once they gain administrative rights on the machine, they can run any command, add users, or install any software, effectively giving them complete control over the system.
Justice Department says Russians hacked federal prosecutors
The Russian hackers behind SolarWinds broke into the email accounts of some of the most prominent federal prosecutors’ offices around the country last year, the Justice Department said. 80% of Microsoft email accounts used by employees in the four U.S. attorney offices in New York were breached between May 7 and Dec. 27, 2020. Jennifer Rodgers, a lecturer at Columbia Law School, said office emails frequently contained all sorts of sensitive information, including case strategy discussions and names of confidential informants, when she was a federal prosecutor in New York.
Iran leak hints at second tier targets as next terror gateway
Following up on a story we brought you in May, a recent report by Sky News exposed a trove of documents appearing to be from a branch of the Islamic Revolutionary Guard Corps (IRGC), Intelligence Group 13. They show a coordinated attempt to collect information on the vulnerabilities of second-tier targets, including those that can capsize merchant vessels, remotely control electrical controllers in building management systems, and tamper with fuel pumps triggering spills or explosions. Michael Langer, a cyberwarfare expert and CPO of Radiflow, says, “Iran is looking to expand the outreach and objects of their cyber-attacks. The mapping of Building Management Systems vulnerabilities may indicate a shift to target more easily exploitable sites.”
(CISOMag)
Thanks to our episode sponsor,
PlexTrac

UK home car charger owners urged to install updates
Security researchers have discovered failings in two home electric car chargers. Wallbox and Project EV – both approved for sale in the UK by the Department for Transport – were found to be lacking adequate security when used with an accompanying app for smartphones. Researchers were able to make the chargers switch on or off, remove the owner’s access, and show how a hacker could get into a user’s home network. Most of the faults have now been fixed but owners are being told to update their apps and chargers, to be safe.
(BBC News)
Euro watchdog will try to extract $900m from Amazon for breaking data privacy laws
On July 16, 2021, the Luxembourg National Commission for Data Protection (CNPD) issued a decision against Amazon Europe claiming that its processing of personal data did not comply with the EU GDPR. The €746m fine is the largest penalty under the 2018 GDPR to date, surpassing the previous top penalty of €50m assessed against Google in 2019 by a factor of 15. The complaint that spurred the ruling contends that Amazon subjects website visitors to behaviorally targeted ads but fails to disclose this practice and obtain consent. Amazon said in reply that the CNPD decision has no merit and that it plans to challenge it.
Zoom reaches $85 mln settlement of lawsuit over user privacy, ‘Zoombombing’
The lawsuit claimed Zoom had violated users’ privacy rights by sharing personal data with Facebook, Google and LinkedIn, and letting hackers disrupt Zoom meetings in a practice called Zoombombing. The San Jose-based company denied wrongdoing in agreeing to settle, but has agreed to incorporate improved security measures. Subscribers in the proposed class action would be eligible for 15% refunds on their core subscriptions or $25, whichever is larger.
(Reuters)
Experts uncover several C&C servers linked to WellMess malware
Cybersecurity researchers on Friday unmasked new command-and-control (C2) infrastructure belonging to the Russian threat actor APT29, aka Cozy Bear, that has been spotted actively serving WellMess malware. First identified by Japan’s JPCERT/CC in 2018, WellMess (aka WellMail) had been previously deployed to plunder intellectual property from organizations involved in COVID-19 research and vaccine development in the U.K., U.S., and Canada. “The group predominantly targets governmental, diplomatic, think-tank, healthcare and energy targets for intelligence gain,” said the U.K.’s National Cyber Security Centre in an advisory published in July 2020. The new WellMess C2 server was discovered on June 11 of this year.