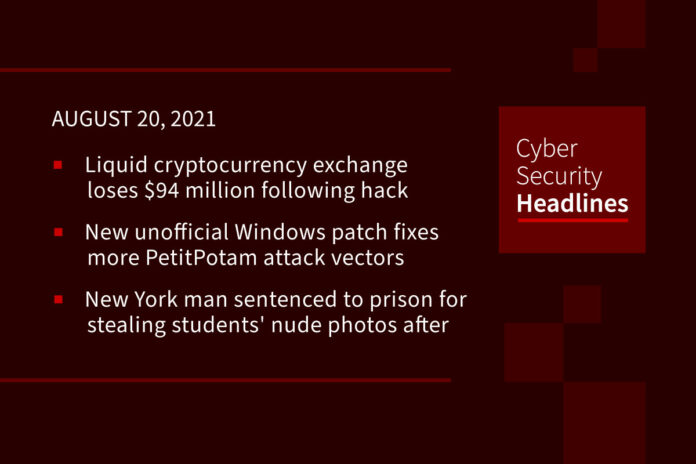
Liquid cryptocurrency exchange loses $94 million following hack
Japan-based cryptocurrency exchange Liquid has suspended deposits and withdrawals after attackers compromised its warm wallets. Liquid is one of the largest cryptocurrency-fiat exchange platforms worldwide with more than 800,000 customers from over 100 countries and says that it reached a $1.1B+ daily trade volume this year. After discovering that its warm wallets were hacked, the crypto exchange moved its assets into a cold wallet and suspended all deposits and withdrawals. According to blockchain analytics firm Elliptic, who is helping Liquid trace the stolen funds, the hackers stole roughly $94 million worth of cryptocurrency assets including $45 million in Ethereum tokens.
New unofficial Windows patch fixes more PetitPotam attack vectors
A second unofficial patch for the PetitPotam vulnerability, which allows a threat actor to force a Windows server or domain controller to authenticate against an NTLM relay server, has been released to fix issues not addressed by Microsoft’s official security update. The PetitPotam bug, tracked as CVE-2021-36942, was partially fixed by Microsoft’s August 2021 Patch Tuesday update but unfortunately, it is still possible to abuse PetitPotam using EFSRPC functions that were not addressed. 0patch micropatching service has released an unofficial patch that can be used to block all known PetitPotam NTLM relay attacks on Windows Server 2019, Windows Server 2016, and Windows Server 2012 and Windows Server 2008 R2. For those who wish to wait an official patch from Microsoft, PetitPotam attacks can be defended against using NETSH RPC filters that block remote access to the EFSRPC service.
New York man sentenced to prison for stealing students’ nude photos after hacking their accounts
The Justice Department announced on Thursday that Nicholas Farber, of Rochester, New York has been sentenced to three years in federal prison for hacking the accounts of dozens of female SUNY Plattsburgh students to access private nude photos. Farber, who is a SUNY Plattsburgh graduate, worked with a co-conspirator, Michael Fish, to access the students’ school email accounts between 2017 and 2019. Fish gained access to at least one account by guessing the answers to a victim’s security questions. Farber then used the credentials to access Facebook, Snapchat and cloud accounts from which he stole private nude photographs and movies, which he then traded with others online. Farber was charged with computer fraud and aggravated identity theft and has been ordered to pay just over $35,000 in restitution to the school. Fish also pled guilty to several related charges and his sentencing is set for November 3. The school implemented multi-factor authentication on all email accounts after the incident.
Cisco security devices are vulnerable to SNIcat data exfiltration technique
On Thursday, Cisco indicated that its firewalls running FTD (Firepower Threat Defense) software, devices running WSA (Web Security Appliance) modules, and all ISA3000 (Industrial Security Appliance) firewalls fail to detect and stop traffic to malicious servers using a technique called SNIcat, which is a data exfiltration technique that covertly s data from inside corporate networks. Researchers at mnemonic discovered the issue by hiding a proof-of-concept Python script inside the TLS Client Hello packet, exchanged at the beginning of the TLS handshake, which occurs prior to being checked for possible suspicious traffic. Cisco became the fourth major network security vendor, joining F5 Networks, Fortinet, and Palo Alto Networks, to disclose that its devices can be bypassed using the SNIcat technique. Cisco is expected to release patches in the near future.
Thanks to our episode sponsor, Copado

To get a free demo, visit Copado.com.
Report reveals growing security concerns in APAC businesses
EY’s 2021 Global Information Security Survey, which polled more than 1,000 organizations worldwide, has revealed 56% of Asia-Pacific businesses admit to circumventing digital processes to accommodate remote or flexible work arrangements, despite 48% also expressing increased concern about their company’s ability to manage security threats. 73% cited an increase of disruptive attacks such as ransomware over the past year, up 26% from the 2020 report. Just 20% of Asia-Pacific respondents said their cybersecurity teams were part of the planning stage of any digital transformation initiative and business managers indicated that they did not always regard their cybersecurity teams as a strategic partner. 41% of APAC respondents anticipate a major breach that they might be able to avoid if they had better investment in cybersecurity, compared to 29% in the Americas.
(ZDNet)
Cisco won’t fix zero-day RCE vulnerability in end-of-life VPN routers
In a security advisory published on Wednesday, Cisco said that a critical Universal Plug-and-Play (UPnP) vulnerability, tracked as CVE-2021-34730 with a 9.8/10 severity score, in multiple small business VPN routers will not be patched because the devices have reached end-of-life. Unauthenticated attackers can exploit the bug to restart vulnerable devices or execute arbitrary code remotely as the root user on the underlying operating system. Cisco noted the vulnerable router models are RV110W, RV130, RV130W, and RV215W and urges customers to migrate to newer routers for which the company continues to provide security updates.
Researchers identify wannabe ransomware scammer soliciting insiders
Cyber firm Abnormal Security said on Thursday that it has identified emails to its customers attempting to persuade recipients to infect their employer networks with ransomware, and then share a cut of the proceeds. Researchers set up a fake identity to communicate with the individual behind the scheme who used the screen name “Pablo.” Through conversations with Pablo, researchers were able to determine that the associated ransomware was DemonWare, which is freely available on GitHub, and that Pablo is stationed in Nigeria and resorted to the insider option after failed phishing email attempts. Pablo wavered on expected ransom and accomplice payout amounts numerous times throughout the conversation. Abnormal Security’s director of threat intelligence, Crane Hassold, indicated, “This is the first time we’ve seen a threat actor attempting to socially engineer an insider employee to deploy ransomware on their behalf against the company they work for.”
Widespread device adoption and complexity increase security risks in schools
Research from Absolute Software reveals that K-12 education IT teams face significant management and security challenges with the adoption of digital devices and remote learning increasing 74 percent from 2019 to 2020. According to the FBI, schools are now the top target for ransomware attackers, with 57 percent of all reported ransomware attacks in August and September 2020 targeting K-12 institutions. The report also revealed that devices issued are traveling further with 47% registering more than 25 miles from their district in spring 2021, up from 27 percent in spring 2020. Data also showed 21 percent of online activity occurring outside established and approved education sites. The report added that device maintenance and complexity is another challenge with Absolute finding that only 53 percent of anti-virus applications on these devices were working effectively.