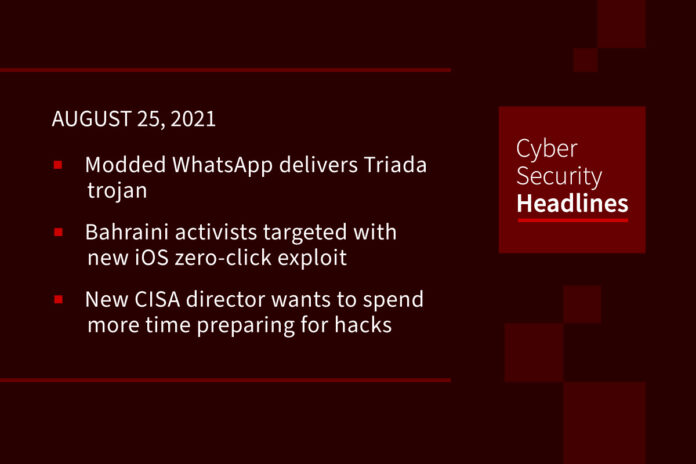
Modded WhatsApp delivers Triada trojan
A modified version of the WhatsApp messaging app for Android has been trojanized to serve malicious payloads, display full-screen ads, and sign up device owners for unwanted premium subscriptions without their knowledge. According to researchers from Kaspersky the Triada trojan sneaked its way into a modified versions of the messenger using FMWhatsApp, a feature that allows users to customize the app with different themes, personalize icons, and even deactivate video calling features. Since FMWhatsApp has access to SMS messages, it allowed the attackers to use the confirmations codes required for premium subscriptions.
Bahraini activists targeted with new iOS zero-click exploit
A new Citizen Lab investigation published yesterday has revealed the existence of a new iOS zero-click exploit that has been abused since at least February this year to hack into the iPhones of several Bahraini activists and political dissidents. Named FORCEDENTRY, the exploit was one of many offensive tools that were used to infect the devices with Pegasus, a surveillance tool developed by NSO Group. FORCEDENTRY is a zero-click exploit, meaning that just receiving an attacker’s malicious iMessage text is enough to infect a device, even without clicking a link or viewing the message and it can bypass BlastDoor, a new security feature that Apple secretly added in iOS 14 last year, which works by placing parts of the iMessages app inside a sandbox in order to isolate malicious code received via new messages. Citizen Lab researchers said they’ve seen the FORCEDENTRY exploit deployed against iOS versions 14.4 and 14.6, and the exploit is believed to work against current iOS versions as well.
New CISA director wants to spend less time cleaning up after big hacks, more time preparing for them
Jen Easterly, the new director of CISA plans to draw on her experience working on cyber operations for the military and for Morgan Stanley. The goal is to ensure that critical infrastructure firms, CISA, the FBI and other agencies are coordinated in responding to major hack like the one that hit Colonial Pipelines and which revealed a communication system in disarray. “I really want to send a signal that we are not your lumbering government bureaucracy,” she said adding “We do not normally bring together the federal government and the private sector to do left-of-boom activity.” Left of boom is a military term meaning being on the timeline before an explosion, rather than after an explosion, which is “right of boom.”
XSS vulnerability in UPS.com distributes malicious invoice
Fraudsters have been leveraging an XSS vulnerability in UPS.com to circulate fake UPS Invoice MS Word documents. Although phishing is commonplace, what makes this phishing attack stand out is that the threat actor used the XSS vulnerability in UPS.com to modify the site’s regular page to look like a legitimate download page. This vulnerability allowed the threat actor to distribute a malicious document through a remote Cloudflare worker but make it look like it was being downloaded directly from UPS.com.
(CISOMag)
Thanks to our episode sponsor, Privacy.com

Researchers warn of 4 emerging ransomware groups that can cause havoc
Researchers from Palo Alto Networks’ Unit 42 yesterday took the wraps off four up-and-coming ransomware groups that could pose a serious threat to enterprises and critical infrastructure, as the ripple effect of a recent spurt in ransomware incidents show that attackers are growing more sophisticated and more profitable in extracting payouts from victims. AvosLocker is a ransomware-as-a-service (RaaS) group that has breached organizations in the US, Europe, and the Middle East. Hive, has already hit several healthcare providers around the world, third is a Linux variant of the HelloKitty ransomware, and fourth is LockBit 2.0, who touts its “unparalleled benefits of encryption speed and self-spread function.”
Ransomware gang’s script shows exactly the files they’re after
On Monday, the MalwareHunterTeam shared a PowerShell script with BleepingComputer used by the Pysa ransomware operation to search for and exfiltrate data from a server. The script is designed to scan each drive for data folders whose names match certain strings on a device. If a folder matches the search criteria, the script will upload the folder’s files to a remote drop server under the threat actor’s control. Of particular interest are the 123 keywords that the script searches for, which give us a glimpse into what the ransomware gang considers valuable. Some are to be expected, such as audit, banking information, login credentials, tax forms, student information, social security numbers, and SEC filings. But It also looks for more intriguing keywords that could be particularly harmful to a company if leaked, such as folders containing the words ‘crime’, ‘investigation’, ‘fraud’, ‘bureau’, ‘federal’, ‘hidden’, ‘secret’, ‘illegal’, and ‘terror.’ The full list of 123 keywords targeted by the threat actors’ script is available at Bleeping Computer.
Samsung remotely bricks stolen smart TVs
Samsung is remotely bricking smart TVs it said were looted from one of its South African warehouses amid violent unrest in the nation. The Samsung televisions ship with a TV Block app, which connects to Samsung servers the minute an internet connection is available. The device reports its serial number and if it matches a list of missing hardware, all television functions are killed off remotely. Normal service can be restored if you can provide a valid proof of purchase and a TV license, Samsung’s South African operation said. The manufacturing giant stressed it is only using TV Block on the kit stolen from its warehouse.