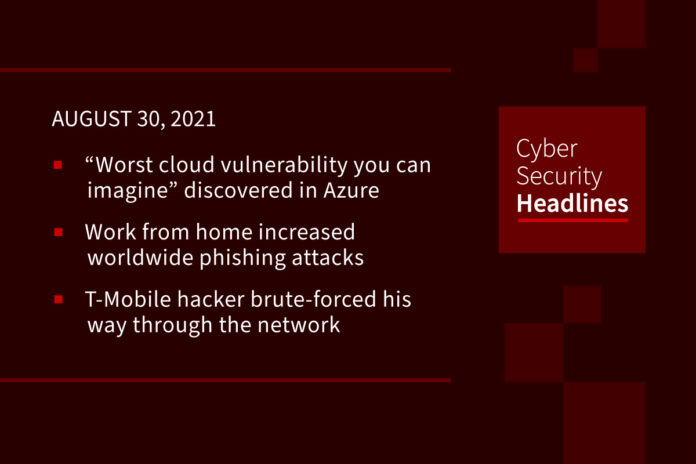
“Worst cloud vulnerability you can imagine” discovered in Microsoft Azure
[Extended story] Cloud security vendor Wiz announced that it had found a vulnerability in Microsoft Azure’s managed database service, Cosmos DB, which granted read/write access for every database on the service to any attacker who found and exploited the bug. Although Wiz only found the vulnerability—which it named “Chaos DB”—two weeks ago, the company says that the vulnerability has been lurking in the system for “at least several months, possibly years.” Although all the details have not been released, it appears to involve a misconfiguration in Microsoft’s open-source Jupyter Notebook which was intended for machine learning algorithms stored in Cosmos DB.
Microsoft rapidly fixed the configuration mistake that would have made it easy for any Cosmos user to get into other customers’ databases, then notified some users Thursday to change their keys. However the Wiz researchers are now urging all users to change their digital access keys, not just the 3,300 notified last week. The U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency used stronger language in a bulletin Friday, making clear it was speaking not just to those notified. “CISA strongly encourages Azure Cosmos DB customers to roll and regenerate their certificate key,” the agency said. Experts at Wiz, founded by four veterans of Azure’s in-house security team, agreed. One of the founders went on record as describing the bug discovery as “terrifying.”
(Ars Technica and Reuters)
Work from home increased worldwide phishing attacks
From September 2019 to April 2021, Palo Alto Network’s Unit 42 monitored firewall traffic and phishing sites detected by URL filters. As individuals began working from home, the number of new phishing pages per week increased significantly. They also noticed a sudden and significant drop in firewall traffic between March and April 2020 when companies were forced to switch to remote work. At this point, threat actors improved and intensified their phishing attacks by exploiting remote work environments where employees were not protected by corporate firewalls and had limited knowledge of cybersecurity best practices.
T-Mobile hacker brute-forced his way through the network
T-Mobile’s CEO Mike Sievert has said that the hacker behind the carrier’s latest massive data breach brute forced his way through T-Mobile’s network after gaining access to testing environments. While stealing personal information on 54.6 million current, former, or potential customers, the attacker could not exfiltrate customer financial information, credit card information, other payment information. Sievert added that the individual “leveraged knowledge of technical systems, along with specialized tools and capabilities to gain access to our testing environments and then used brute force attacks and other methods to make their way into other IT servers that included customer data.”
Thanks to our episode sponsor, Semperis
Windows 11 to only support one Intel 7th gen CPU, no AMD Zen 1 CPUs
Microsoft made the announcement Friday. When Microsoft first announced Windows 11, many users were upset, if not angry, about the new and stricter system requirements for the new operating system. This means that many people are finding that their devices with Intel 7th generation and first generation AMD Zen CPUs, which run Windows 10, cannot upgrade to Windows 11. Microsoft has released a new tool called PC Health Check that checks if a computer’s hardware is compatible with Windows 11, but gives little information as to why a device may not be compatible.
Hive ransomware hackers call victims by phone
The Hive ransomware group is hiring call centers to make phone calls to victims in order to extort their data hostage fee. As we mentioned last week, Hive is one of the four up-and-coming cybercrime groups to watch and they appear to be leveraging an affiliate business model which involves hackers renting access to a malware tool, working with other specialists and then splitting the profits. Call centers, either for so-called customer support or payment harassment, often function as part of that scheme, with a single call center operating on behalf of multiple gangs.
Data poisoning: the next big threat
Data poisoning against security software that uses artificial intelligence (AI) and machine learning (ML) is likely the next big cybersecurity risk. According to the RSA 2021 keynote presentation by Johannes Ullrich, dean of research of SANS Technology Institute in Bethesda Maryland, it’s a threat we should all keep an eye on. Data poisoning occurs when attackers tamper with data used to train AI models. Because AI relies on that data to learn how to make accurate predictions, the predictions generated by the algorithm will be incorrect. For example, threat actors can change data for a recommendation engine which will help get someone to download a malware app or click on an infected link. Ullrich said the solution starts with having thorough knowledge of the models used by AI cybersecurity tools.
Man robbed of 16 Bitcoin sues parents of young thieves
A man who had approximately $1 million worth of bitcoin stolen back in 2018 has filed a civil lawsuit in Colorado against the parents of the people he believes were responsible, both of whom are currently studying computer science at U.K. universities, and were minors at the time of the theft. A forensic investigation of the victim’s computer found he’d inadvertently downloaded malicious software after clicking a link posted on reddit for a purported cryptocurrency wallet application called “Electrum Atom.” The malware swapped out his bitcoin address. The victim had hoped that the parents of the teens would listen and return the money, and he filed the suit after their continued silence.