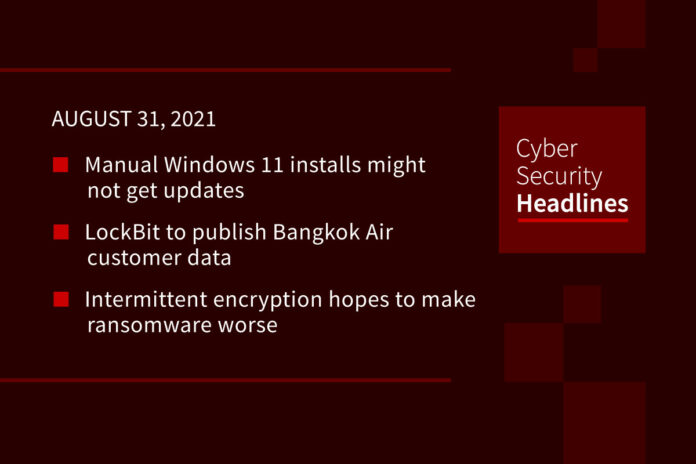
Manual Windows 11 installs might not get updates
Microsoft confirmed it won’t block users installing Windows 11 on older PCs manually using ISO files. The requirements to get the OS to run using a manual install are pretty straightforward, a 64-bit 1GHz processor with two or more cores, 4GB of RAM, and 64GB of storage. However, the company said manual installs of the OS may not be entitled to Windows Updates, even security ones, and is mainly meant to be used by businesses evaluating the OS.
Microsoft also announced system’s with Intel’s Core X-series, Xeon W-series, and the Core 7820HQ found in the Surface Studio 2 are supported in Windows 11, but said there would be no support for AMD Zen 1-based CPUs. The company plans to update its PC Health Check app to include the updated CPU support information and provide clarity why your system might not be able to upgrade.
LockBit to publish Bangkok Air customer data
Bangkok Air confirmed it suffered a ransomware attack last week. Now the LockBit ransomware gang claims to have obtained 103GB worth of customer data, pledging to release it on August 31st if a ransom isn’t paid. Data exfiltrated includes names, emails, phone numbers, passport information, and partial credit card info, the kind of stuff social engineering and phishing attacks are made from. It doesn’t appear the attacks had access to Bangkok Air’s operational or aeronautical security systems.
Intermittent encryption hopes to make ransomware worse
Security researchers with Sophos identified a new ransomware called LockFile, which employs a novel intermittent encryption technique. LockFile encrypts every 16 bytes of a file, which helps the ransomware to evade security detections, using memory-mapped input/output to encrypt a file that allows the attackers to target cached documents in the compromised system’s memory. LockFile also leaves no ransomware binary for analysis and clean up. The LockFile operators have been using recently disclosed ProxyShell and PetitPotam vulnerabilities to compromise Microsoft Exchange servers.
(CISO Mag)
It’s the end of days for Ragnarok ransomware
The operators of Ragnarok ransomware gang closed shop and released its universal decryption key. Ragnarok had been active since 2019, using the Ragnar Locker ransomware to target IT networks, collecting over $4.5 million in documented ransom payments. The operators did not announce why it was shutting down. Several high profile ransomware gangs have closed shop in recent years due to stepped up investigations by law enforcement. Others, like the DoppelPayment ransomware, have simply gone dormant before rebranding.
Thanks to our episode sponsor, Semperis
Bumble stumbles, reveals user locations
One of the features of the popular dating app Bumble is showing a prospective date;s distance from you while you’re browsing the app. However, using a fake account security researcher Robert Heaton was able to determine a user’s precise location using a ‘trilateration’ attack. Heaton notified Bumble who quickly patched the vulnerability, as well as adding controls to prevent matching with or viewing users outside of a user’s match queue. This appears to be a client-side fix to the problem, so users will have to install the patched version of the app for it to be effective.
BazaLoader makes DMCA takedown notices even worse
Digital Millennium Copyright Act notices are the bane of many a content creator. These notifications often require a response in order for content to not be taken down, and the guilty-until-innocent nature made them the perfect target to get click through for the BazaLoader malware. These emails appear to reference allegedly stolen images, with a Firebase URLs that will download the BazaLoader. This will be the first stage before loading Cobalt Strike. A similar tactic will also send an email alleging a site is engaged in a distributed denial-of-service, with a legal threat included to spur action.
Deepfakes-as-a-Service (Dfaas)
MIT Technology Review profiled Hour One, a startup that licenses a model’s likeness to use in AI-generated videos. This is done by recording 4k footage of the model moving and speaking in front of a green screen. The company has about 100 AI-generated “characters” that can be used for videos, with over 40 clients. Models receive a micropayment every time a client licenses a video with their likeness. Models do not have a say in how their likeness will be used, but Hour One’s ethics policy says it won’t work with certain industries, including gambling, sex, and politics.
Cyber Fellowship program to train attorneys on cyber threats
The US Department of Justice announced the new program, which is being run through the Criminal Division’s Computer Crime and Intellectual Property Section. This will train federal employees across departments which are focused on cyber defense, going into detail about cybersecurity-related cases such as operations of state-sponsored threat actors and cybercrime organizations. The goal is to create a “new generation of prosecutors and attorneys equipped to handle emerging national security threats.” Candidates will need to obtain a Top Secret security clearance and commit to the three-year program.