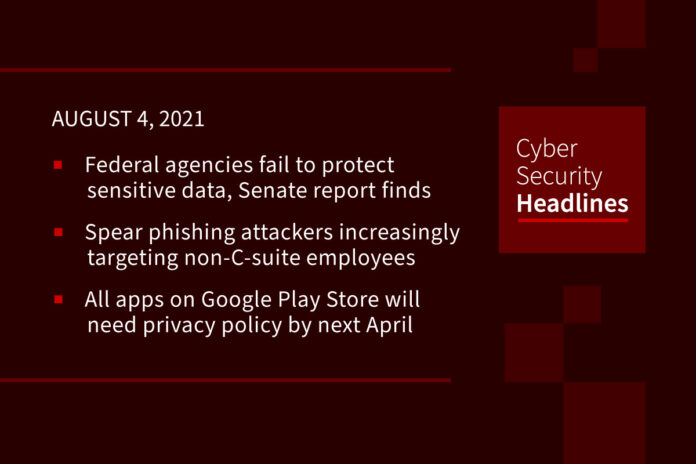
Federal agencies are failing to protect sensitive data, Senate report finds
Of eight federal agencies audited for their cybersecurity programs, only the Department of Homeland Security showed improvements in 2020, according to a report from the Senate Homeland Security and Governmental Affairs Committee. Released by the panel yesterday, the report underscores the increased scrutiny of federal cybersecurity by lawmakers in the aftermath of the SolarWinds supply chain attack. It found that seven of the eight agencies reviewed still use legacy systems that no longer have security updates supported by their vendor, which can leave agencies vulnerable to foreign hacking, the report notes.
Spear phishing attackers increasingly targeting non-C-suite employees
According to a report from Barracuda, an average organization is targeted by over 700 social engineering attacks each year, and 77% of BEC attacks target employees outside of financial and executive roles, including personnel working in sales, project management, human resources, and administration. Different from regular spam, these non c-suite spearphishing attacks show that middle and lower levels of an organization are now becoming easier targets. Findings in the report, entitled, Spear Phishing: Top Threats and Trends Vol.6, include that 43% of phishing attacks impersonate Microsoft brands, and that 1 on 5 BEC attacks are aimed at the sales team.
(CISOMag)
All apps on Google Play Store will need privacy policy by next April
As part of ongoing changes to help increase safety, security, and transparency for apps on the Play Store, Google hopes that by announcing the guidelines now, app developers will have time to respond. While Google is still figuring out the final design of the safety section, it has provided early some early mock-ups. For developers that aren’t able to provide an approved security section in time, Google says new apps or app updates from that developer may get rejected, with the safety section for non-compliant apps set to display a line saying “No information available.”
(Gizmodo)
DeadRinger targeted exchange servers long before discovery
Researchers have discovered that threat actors linked to China exploited the Microsoft Exchange ProxyLogon vulnerabilities long before they were publicly disclosed, waging attacks against telecommunications companies, to steal customer data and maintain network persistence. Researchers from Cybereason have been tracking multiple cyberespionage campaigns collectively dubbed “DeadRinger” since 2017, reporting initially on findings that a Chinese threat group named SoftCell was targeting billing servers to steal call records from telecoms in Africa, the Middle East, Europe and Asia. A report released yesterday builds upon this research, identifying two new threat groups – Naikon APT and Group-3390 – that also appear to be working for China’s regime.
Thanks to our episode sponsor,
PlexTrac

Raccoon stealer-as-a-service will now try to grab your cryptocurrency
A new campaign, tracked by Sophos, shows that the malware is being spread not through spam emails this time, but through droppers disguised as installers for cracked and pirated software. Samples obtained by Sophos revealed that the stealer is being bundled with malware including malicious browser extensions, cryptocurrency miners, and click-fraud bots targeting YouTube sessions. Raccoon Stealer is able to monitor for and collect account credentials, cookies, website “autofill” text, and financial information that may be stored on an infected machine. However, the upgraded stealer also has a “clipper” for cryptocurrency-based theft.
(ZDNet)
Google Chrome to no longer show secure website indicators
Further to its push for universal use of https over http, upcoming releases of the Google Chrome browser will no longer display the closed padlock icon, signifying a page has been encrypted with the more secure https protocol. This new feature, slated for Chrome 94 will only display security indicators when a site is not secure, replacing the padlock with the words, “not secure.” For businesses that wish to continue with the padlock indicator, Google has added an enterprise policy for Chrome 93 named ‘LockIconInAddressBarEnabled’.
Microsoft unveils proof of vaccination requirements for entering a Microsoft building in the US
Proof of vaccination is required for all employees, vendors, and any guests, although employees with a medical condition or a protected reason, such as religion, that prevents them from getting a vaccine can get a special accommodation. The company has also pushed its full office reopening date from September to “no earlier than October 4th, 2021. Microsoft’s announcements follow the recent surge in COVID-19 cases around the country and aligns with policies put in place by Facebook, and Google who will also require employees to be vaccinated before they can return to the office who have delayed their opening to October.
Hackers leak full EA data after failed extortion attempt
The hackers who breached Electronic Arts last month have released the entire cache of stolen data after failing to extort the company and later sell the stolen files to a third-party buyer. The data, dumped on an underground cybercrime forum on Monday, July 26, is now being widely distributed on torrent sites. According to a copy of the dump obtained by The Record, the leaked files contain the source code of the FIFA 21 soccer game, including tools to support the company’s server-side services. The hackers originally gained access to the data after buying authentication cookies for an EA internal Slack channel from a dark web marketplace called Genesis. They used the authentication cookies to mimick an already-logged-in EA employee’s account and access EA’s Slack channel and then trick an IT support staffer into granting them access to the company’s internal network.