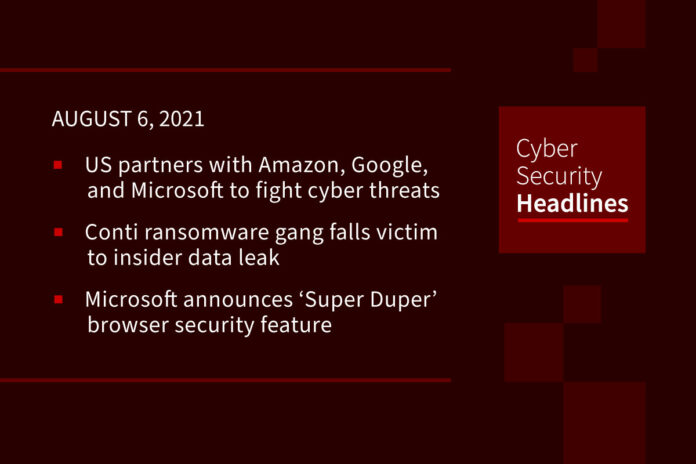
US partners with Amazon, Google, and Microsoft to help fight cyber threats
At the Black Hat cybersecurity conference on Thursday, the Department of Homeland Security’s Director of CISA, Jen Easterly, unveiled the Joint Cyber Defense Collaborative, which enlists support from tech companies, including Amazon, Microsoft and Google, to focus on combating ransomware and cyberattacks on cloud-computing providers. According Easterly, the initiative aims to improve defense planning and information sharing between government and the private sectors and added that tackling these threats “has to be a whole-of-nation effort.” Recent significant disruptions caused by cyber attacks on US infrastructure have made cybersecurity a major area of concern beyond the White House. The Senate has included additional funding for CISA in its $1 trillion infrastructure bill which is under review in the chamber this week. Other Joint Cyber Defense Collaborative participants include CrowdStrike, FireEye, Palo Alto Networks, AT&T, Verizon, and Lumen Technologies.
(WSJ)
Conti ransomware gang falls victim to insider data leak
An apparently disgruntled member of the Conti ransomware gang, which runs a ransomware-as-a-service (RaaS) operation, has leaked the gang’s inside information including IP addresses for Cobalt Strike C2 servers and a 113 MB archive containing numerous tools and training material for conducting ransomware attacks. The gang member indicated that he leaked the info because he was only paid $1,500 for his part in an attack, while the rest of the team are making millions. Advanced Intel’s Vitali Kremez, who analyzed the archive, has confirmed that the training material matches active Conti cases. Security researcher Pancak3, advised via twitter that administrators should block the published IP addresses to help prevent future attacks.
Microsoft announces new ‘Super Duper’ browser security feature
Earlier this week, Microsoft announced that it plans to introduce Super Duper Secure Mode within its Edge web browser on an experimental basis, which will feature disabling support for JIT (Just-In-Time) inside the Edge browser’s V8 JavaScript engine. JIT plays a crucial role in modern web browsers, by compiling JavaScript to machine code ahead of time, which significantly improves browser speed if the code is needed. Microsoft Edge Vulnerability Research Lead, Johnathan Norman said JIT-related security issues amounted to 45% of all V8 vulnerabilities in 2019. In place of JIT, Edge’s Super Duper Secure Mode will enable other security features such as Controlflow-Enforcement Technology (CET) and Arbitrary Code Guard (ACG). According to Norman, there are no set plans to ship the new security feature to users just yet.
Google announces delays in enforcing 2SV for Chrome extension devs
As first announced in June, Google requires all Chrome extension developers to enable 2-Step Verification (or 2SV) to publish or update their extensions as of August 2. The goal of the 2SV requirement is to prevent threat actors from hijacking developer accounts and releasing malicious extension updates. Google issued a statement on Wednesday, indicating, “It may take several weeks for the Two Step Verification requirement to be enforced across all Chrome Web Store accounts.” The 2SV requirement is part of a broader set of security requirements which include ensuring that developers don’t use deceptive installation tactics and spammy or repetitive content, which could diminish the security and overall quality of Chrome extensions.
Thanks to our episode sponsor,
PlexTrac

Apple to start scanning iPhones for banned content
Apple is about to announce a new technology for scanning individual users’ iPhones for banned content. While the new tech will be billed as a tool for detecting child abuse imagery, its potential for misuse appears to be vast. Respected cryptography professor Matthew Green stated on Thursday that the neural network-based tool will scan users’ iDevices for child sexual abuse material (CSAM) using machine learning (ML) techniques. Using ML to intrusively scan end user devices is new and may shake public confidence in Apple’s privacy-focused marketing. The new scanning tech will be first be deployed against America-based iThing users, and then gradually rolled out world-wide.
Italian energy company ERG hit by LockBit 2.0 ransomware
Recently the Italian energy company ERG, which produces wind, solar, hydroelectric and thermoelectric energy with low environmental impact, was hit by the LockBit 2.0 ransomware gang. A notice published by ERG, indicates, “ERG reports that it has experienced only a few minor disruptions to its ICT infrastructure, which are currently being overcome, also thanks to the prompt deployment of its internal cybersecurity procedures.” However, the ordeal isn’t over for ERG, as LockBit 2.0 has indicated that will begin leaking ERG’s stolen data to its site beginning at midnight on August 14, 2021.
Telegram bug lets you save self-destructing messages forever
Telegram offers an optional ‘Secret Chat’ mode that increases the privacy of chats by enabling features such as encryption and the ability to set messages to automatically self-destruct and be removed from all devices after a certain period. However, Trustwave SpiderLabs’ Lead Threat Architect, Reegun Richard Jayapaul, has discovered that self-destructing messages and attachments in Telegram for Mac were not deleted from the cache folder, therefore allowing a recipient to save it to another location on their hard drive. This bug was fixed by Telegram for macOS in version 7.7 (215786) or later after it was reported, but there’s an additional bug that allows a user to simply copy media from the cache folder before viewing it in the application. Telegram told Reegun that this second bug would not be fixed as there is no way to protect against direct access to the app’s folder.
CYBER.ORG releases first national K-12 cybersecurity learning standards
CYBER.ORG announced the release of the nation’s first voluntary K-12 cybersecurity learning standards to be used in schools and districts around the country. At a time when the United States is facing an onslaught of sophisticated cyberattacks and over 464,000 unfilled cybersecurity positions nationwide, the new standards aim to build a strong, more diverse talent pipeline to protect US national security, maintain competitiveness on the world stage, and helping address the cybersecurity workforce shortage. Director of Academic Outreach at CYBER.ORG, Kevin Nolten, stated, “For the first time, educators have a roadmap for uniformly teaching cybersecurity to students in each grade band across the country.” States now have the option to adopt the cybersecurity learning standards ahead of the 2022-2023 school year.