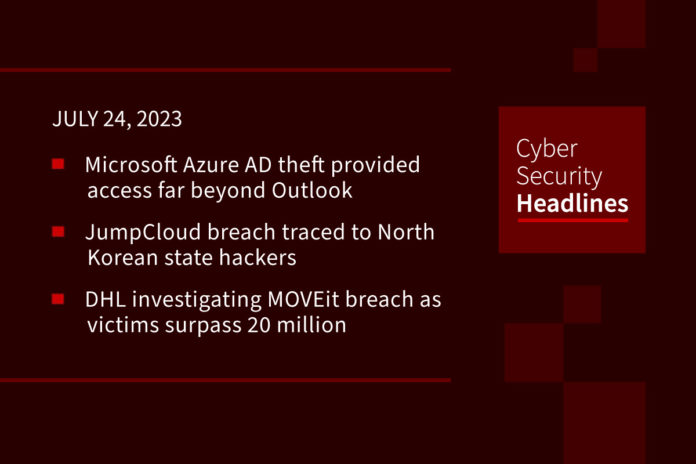
Microsoft key stolen by Chinese hackers provided access far beyond Outlook
In a blog post published Friday, Shir Tamari, head of research at Wiz, stated that the key, allegedly stolen by Chinese hackers, would have given the group, which Microsoft calls Storm-0558, access well beyond Outlook, and into many other Microsoft services that use the same authentication process. Tamari suggests that this would include “every application that supports personal account authentication, such as SharePoint, Teams, OneDrive, customers’ applications that support the login with Microsoft functionality, and multi-tenant applications in certain conditions.” Although Microsoft revoked the affected key, Wiz warns that the APT “could have used the access and time to build in backdoors or other forms of persistence into victim systems and accounts.”
(SCMagazine and Wiz)
JumpCloud breach traced back to North Korean state hackers
Security researchers at SentinelOne, CrowdStrike, and Mandiant are unanimous in suggesting that U.S. software company JumpCloud was breached by hackers affiliated with the North Korean Lazarus Group. SentinelOne senior threat researcher Tom Hegel bases this link on “multiple indicators of compromise shared” by the company in a recent incident report. CrowdStrike vice president for intelligence Adam Meyers told Reuters, the attack was intended for revenue generation.
DHL investigating MOVEit breach as number of victims surpasses 20 million
Shipping company DHL said its UK division is investigating a data breach that appears to be connected to its use of the MOVEit software. In a statement to Recorded Future News, DHL confirmed that one of its software providers was impacted by the vulnerability affecting MOVEit. Researchers from Emsisoft suggest that at least 383 organizations have been affected, with information belonging to more than 20 million people being leaked.
Elon Musk says Twitter to change logo, no more birds
Elon Musk said on Sunday he was looking to change Twitter’s logo, tweeting: “And soon we shall bid adieu to the Twitter brand and, gradually, all the birds.” A message from Musk tweeted at 12:06 a.m. ET Sunday morning, he stated, “If a good enough X logo is posted tonight, we’ll make (it) go live worldwide tomorrow.”
(Reuters)
Thanks to this week’s episode sponsor, AppOmni

Sophisticated BundleBot malware disguised as Google AI chatbot and utilities
Malware known as BundleBot has been taking advantage of .NET single-file deployment techniques, “enabling threat actors to capture sensitive information from compromised hosts.” According to a report from CheckPoint, it is “commonly distributed via Facebook Ads and compromised accounts leading to websites masquerading as regular program utilities, AI tools, and games.” Some of these websites seek to impersonate Google Bard, conning victims into downloading a bogus RAR archive (“Google_AI.rar”) hosted on cloud storage services such as Dropbox.
DDoS hits OnlyFans
Anonymous Sudan, a seemingly pro-Russian hacktivist group affiliated with KillNet, delivered a one-hour DDoS attack on OnlyFans Wednesday. This is the latest activity aimed at American and European targets. Mandiant stated that while it “cannot confirm collaboration or cooperation with Russian security services, KillNet’s targeting of victims consistently reflects the interests of the Russian state.” Swedish cybersecurity firm Truesec adds, “It’s not clear who is behind Anonymous Sudan, but it almost certainly is not part of the larger Anonymous collective and likely has nothing to do with the original Anonymous Sudan.”
Researchers warn of several DDoS botnets exploiting Zyxel devices
Part of an ongoing story, Fortinet FortiGuard Labs researchers have identified DDoS botnets exploiting a vulnerability impacting Zyxel firewalls. The flaw, tracked as CVE-2023-28771 (CVSS score: 9.8), is a command injection issue that could potentially allow an unauthorized attacker to execute arbitrary code on vulnerable devices. Zyxel addressed the issue in April and advised customers to install the patches provided. As of May 19, there were at least 42,000 instances of Zyxel devices on the public internet. Researchers from Rapid7 added, “Since the vulnerability is in the VPN service, which is enabled by default on the WAN, we expect the actual number of exposed and vulnerable devices to be much higher.”
Last week in ransomware
Last month saw the release of new ransomware named NoEscape (or No_Escape), which, according to ransomware expert Michael Gillespie, is a rebrand of Avaddon, who shut down in June 2020 after being pursued by law enforcement. Other ransomware news includes a new SophosEncrypt ransomware that impersonates Sophos; FIN8 threat actors seen deploying the ALPHV ransomware using Sardonic malware; and Big Head ransomware displaying fake Windows update alerts. Clop’s data theft attacks using the MOVEit Transfer zero-day continues to claim additional victims. According to a new Coveware report released last week, the MOVEit attacks are expected to earn the gang $75-100 million in extortion payments.