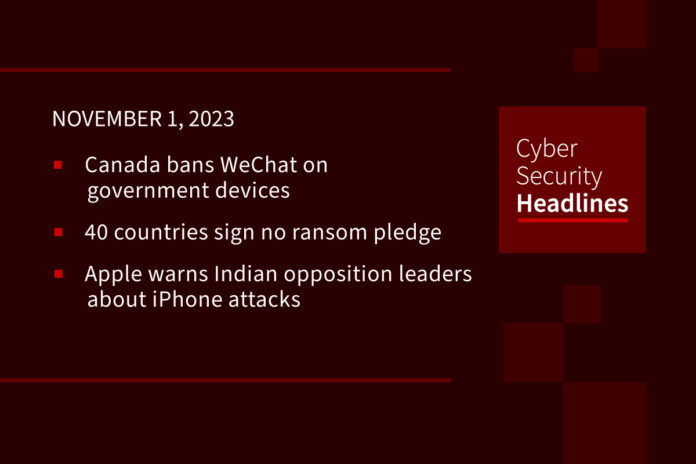
Canada bans WeChat on government devices
The Treasury Board of Canada announced the move, saying that the country’s chief information officer determined the Chinese messaging app presents “an unacceptable level of risk to privacy and security.” It also banned Kaspersky’s antivirus solutions on the same grounds. The government said neither app compromised government data, but that the access to a device’s content represented obvious risks. China’s foreign ministry said the ban lacked any real evidence and called it an abuse of national power.
(Reuters)
40 countries sign no ransom pledge
A White House official announced that forty countries signed on to a US-led International Counter Ransomware Initiative to not pay cybercrime-related ransoms. As part of the initiative, the alliance will create two information-sharing platforms about ransom payment accounts, one created by Lithuania, the other jointly run by Israel and the United Arab Emirates. The countries will also share a list of digital wallets used to process ransom payments. This alliance means the governments agree not to pay ransoms in the attacks.
(Reuters)
Apple warns Indian opposition leaders about iPhone attacks
Several Indian opposition leaders, two journalists, and the President of the Observer Research Foundation announced Apple recently contacted them about being targets of state-sponsored attacks. Apple confirmed these notifications but did not attribute attacks to any actor. India’s IT Minister Ashwini Vaishnaw said the government will investigate the notification, but said the notifications represented “estimations.” Earlier this year, researchers found NSO Group spyware on Indian opposition phones, and the Financial Times reported in March that the Indian government began looking for new spyware contracts.
Palo Alto Networks buys Dig Security
Back in September, we covered reports that Palo Alto Networks planned some major acquisitions before the end of the year. One of those shoes dropped with the security giant acquiring the Israeli firm Dig Security. No official word on the terms, but TechCrunch’s sources say it cost around $400 million. Dig provides services to understand where organizational assets reside across clouds. These assets will integrate with Palo Alto’s Prisma business. TechCrunch’s sources say the company continue to work on a deal to acquire the Israeli firm Talon, in a deal estimated worth $1 billion.
Huge thanks to our sponsor, Hunters

Citrix Bleed under exploitation
Citrix issued a patch for this vulnerability on October 10th. This impacts Citrix’s NetScaler Application Delivery Controller and NetScaler Gateway, opening to the door to disclosing information that includes session tokens that can be used to crack MFA. Security researcher Kevin Beaumont recently posted that it appears the vulnerability is “now under mass exploitation” with many organizations seeing widespread attacks. Beaumont estimates that 20,000 instances have seen session tokens stolen. The takeaway: all organizations should consider unpatched Netscaler devices compromised at this point and credentials should rotate to ensure leaked tokens no longer pose a threat.
Crypto theft tied to LastPass breach
The cryptocurrency researcher ZachXBT announced that they found evidence of $4.4 million in cryptocurrency stolen from over 25 victims directly coming from the 2022 breach of the popular password manager. This comes from actively approaching victims seen on-chain as well as victims reaching out to ZachXBT on X. It’s believed stolen password vaults of the attack are being cracked using GPU to brute force weaker passwords. It’s recommended that impacted users reset all passwords and move crypto assets to new wallets as a precaution.
MOVEit breach hits US government
According to documents received from a Freedom of Information Act request, Bloomberg reports that the MOVEit breach over the summer saw the Clop threat group access emails from the government. This saw the threat actors access emails on roughly 632,000 federal employees at the Department of Justice and Defense. The govenrment already disclosed some agencies were compromised from that breach, but this is the first indication of the scope. The breach occurred on May 28th and 29th, but compromised data was of “low sensitivity” and not classified.
Atlassian releases urgent Confluence patch
The company issued a security advisory, warning of a critical “improper authorization vulnerability in Confluence Data Center and Server” impacting on-prem versions. The company said it didn’t observe active exploitation yet, with the advisory light on any technical details for now. It recommends patching all versions now to resolve the issue. And disconnecting all Confluence instances from public internet until deploying the patches. This marks a different critical Confluence exploit from the one announced October 4th, which was under active exploitation.