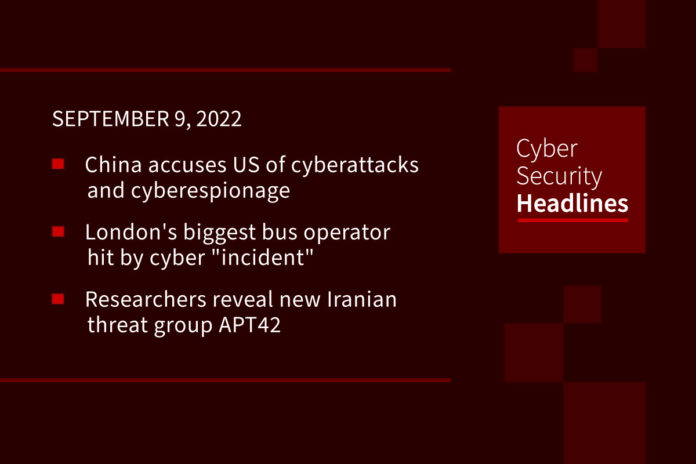
China accuses US of cyberattacks and cyberespionage
On Monday, the Chinese National Computer Virus Emergency Response Center (CVERC) published a report, co-authored by the private Chinese cybersecurity firm Qihoo 360, that accuses the US National Security Agency (NSA) of conducting “tens of thousands of malicious attacks on network targets in China in recent years” through the NSA’s Tailored Access Operations (TAO) elite hacker unit. The attacks included a university that focuses on aeronautical and space research. The foreign ministry in Beijing stated, “we ask the US to provide an explanation and urge them to immediately stop this illegal move.”
London’s biggest bus operator hit by cyber “incident”
Newcastle-based transportation group Go-Ahead this week shared a statement with the London Stock Exchange indicating “unauthorized activity” had been discovered on its network. Sky News reported that bus and driver rosters may have been impacted by the attack, which could disrupt operations. Go-Ahead operates multiple services across England and is London’s largest bus company, operating over 2400 buses in the capital and employing more than 7000 staff. The firm also operates several high-capacity railway services in the UK including Great Northern, Thameslink, Gatwick Express and Southern.
Researchers reveal new Iranian threat group APT42
Threat intelligence firm Mandiant claims to have found at least 30 victims of APT42, although it said the count is likely much higher given the group’s “high operational tempo.” Based on APT42’s targeting patterns, Mandiant assessed with “moderate confidence” that it is operating on behalf of the Islamic Revolutionary Guard Corps Intelligence Organization (IRGC-IO), and poses a threat to foreign policy officials, commentators, and journalists, particularly those in the US, the UK and Israel, working on Iran-related projects,” it said.
Over 80% of top websites leak user searches to advertisers
Security researchers at Norton Labs have found that roughly eight out of ten websites featuring a search bar will leak their visitors’ search terms to online advertisers like Google, which carries the implication of breaching the users’ privacy and leaking sensitive information to a network of third parties who then use this data to deliver targeted advertisements or track user behavior on the web. This leaves users unable to estimate their exposure or stop its dissemination. While some websites may declare this practice in their user policy, visitors typically don’t read these and assume that the information they enter on embedded search fields is isolated from big data brokers.
Thanks to today’s episode sponsor, Snyk
Code, dependencies, containers, cloud environments… all of it.
And while developers are building securely, Snyk gives security teams a bird’s eye view of all of their projects and cloud environments, so they can prioritize and focus their efforts in the right places.
Developer tested. Security approved. Start your free Snyk account at snyk.co/cybersecurity
US government recovers $30M from Axie Infinity hack
Crypto analytics firm Chainalysis announced Thursday it helped the U.S. government recover about $30 million stolen from Axie Infinity earlier this year. In a blog post, Chainalysis’ Erin Plante said law enforcement officials were able to recover the funds, which were stolen by North Korea’s Lazarus Group, a hacking entity tied to multiple crypto thefts over recent years. Plante said, “this marks the first time ever that cryptocurrency stolen by a North Korean hacking group has been seized, and we’re confident it won’t be the last.” Hackers stole over $600 million from Axie this past spring, laundering many of the proceeds through privacy mixer Tornado Cash. The U.S. Treasury Department later sanctioned Tornado Cash for facilitating money laundering.
(Coinbase)
Lazarus Group unleashes custom malware to spy on energy providers
Lazarus Group is also behind a new cyberespionage campaign whose goal is to steal data and trade secrets from energy providers across the US, Canada, and Japan, according to Cisco Talos. In research published yesterday, Talos threat researchers say they observed malicious activity attributed to Lazarus Group between February and July. All of the intrusions began by exploiting Log4j vulnerabilities in VMware Horizon, followed by the deployment one or more of three custom malware implants called VSingle, YamaBot, and MagicRAT.
Classified NATO documents stolen from Portugal, now sold on darkweb
The Armed Forces General Staff agency of Portugal (EMGFA) has suffered a cyberattack that allegedly allowed the theft of classified NATO documents, which are now sold on the dark web. The agency only realized they suffered a cyberattack after hackers posted samples of the stolen material, offering to sell the files to interested individuals. American cyber-intelligence agents noticed the sale of stolen documents and alerted the U.S. embassy in Lisbon, which in turn warned the Portuguese government about the data breach.
Emergency text averted possible California power cuts
The message asked residents to limit energy use for three hours to cut the risk of power cuts being implemented. The California Independent System Operator (Cal-ISO), said it “saw an immediate and significant drop” in the use of power after the text was sent. The alert was issued after record temperatures put pressure on the state’s electrical grid. The message, called a flex alert, was created by Cal-ISO to encourage users to conserve electricity when energy supply is at capacity. The alert targeted 24 counties, which included Los Angeles and the Bay Area, because of high population and high air conditioning use.
(BBC News)