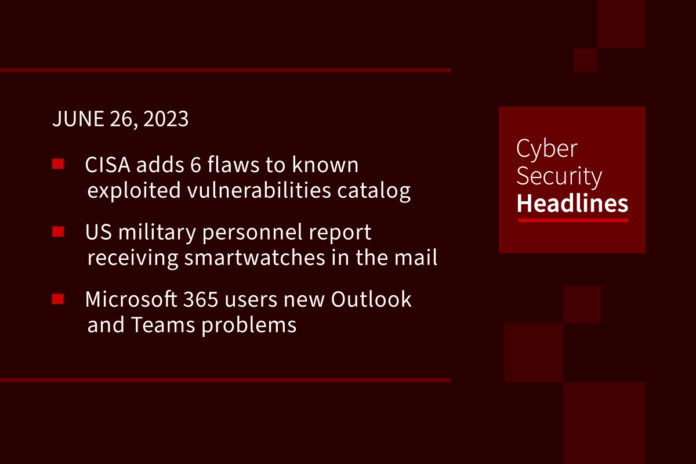
CISA adds 6 flaws to known exploited vulnerabilities catalog
The collection comprises three Apple vulnerabilities that were patched this week, two flaws in VMware, and one impacting Zyxel devices. The Apple vulnerabilities were the centerpiece of Operation Triangulation, designed to harvest a wide range of information from compromised devices, such as creating, modifying, removing, and stealing files, listing and terminating processes, gathering credentials from iCloud Keychain, and tracking a user’s location.
US military personnel report receiving smartwatches in the mail
Service members across the military who have received these unsolicited smartwatches in the mail report that upon using them, they automatically connected to Wi-Fi and to cellphones unprompted, gaining access to a huge quantity of user data. They may also contain malware that would grant the sender access to saved data that includes banking information, passwords and PII, and also may contain malware that accesses both voice and cameras. US Military personnel are advised to not turn these unsolicited watches on, and to report the receipt to their local counterintelligence, or security manager.
Microsoft 365 users new Outlook and Teams problems
There have been additional Microsoft 365 issues this week, with some users reporting that they cannot use Microsoft Outlook or other Microsoft 365 apps. This problems started last Monday, with numerous instances of Microsoft Outlook either not opening or freezing after opening. Other users complained of seeing delays in mail delivery, or errors announcing no valid license associated with the user. There are also reports that users are experiencing crashes and freezes in Word, Excel, and Teams. This appears to be a different problem than the Outlook issue that Microsoft fixed last week.
Chinese state-backed hackers accidentally infect a European hospital
The incident occurred earlier this year at an unnamed hospital that was inadvertently affected by a self-propagating malware infection introduced to its network via a USB drive. Incident responders discovered that an employee of the hospital attended a conference in Asia and conducted a presentation with another attendee. That person’s laptop was infected with WispRider — a powerful malware that can not only bypass antivirus solutions and establish backdoors into a system but also spread itself to newly connected removable drives. Check Point researchers have traced this to Camaro Dragon also known by researchers as Mustang Panda and LuminousMoth— a China-based espionage threat actor whose operations focus on Southeast Asian governments and institutions.
Thanks to this week’s episode sponsor, AppOmni
LastPass users furious after being locked out due to MFA resets
Following a requirement from LastPass for users to reset their authenticator apps following planned security upgrades on May 9, some customer have been experiencing login issues. The company stated that users might need to log back into their LastPass account and reset their multifactor authentication preference. “Since then, numerous users have been locked out of their accounts and unable to access their LastPass vault, even after successfully resetting their MFA applications.” Unfortunately, these affected customers cannot ask for assistance from LastPass support since that requires logging into their accounts, which they cannot do. LastPass says the MFA resets were announced via in-app messages for “several weeks” before the initial announcement, and additionally, advisories and instructional videos had been provided.
Capital One becomes latest bank affected by cyberattack on debt-buying giant
Capital One has come forward to say it is the most recent financial institution to have been affected by the cyberattack on NCB Management Services, a company that purchases debt. The NCB attack resulted in a initial response to former customers of Bank of America, via notification letters sent in March after discovering the February 4 attack, which confirmed that almost 500,000 people had sensitive financial information leaked. In new letters filed with regulators, Capital One has confirmed that its customers were also involved.
Lawyers who cited fake cases hallucinated by ChatGPT must pay
Following up on a story we brought you last month, the attorneys who filed court documents citing cases that had been composed by OpenAI’s ChatGPT have now been formally reprimanded by a New York judge. Judge Kevin Castel pointed out how they had “abandoned their responsibilities when they submitted non-existent judicial opinions with fake quotes and citations created by…ChatGPT, then continued to stand by the fake opinions after judicial orders called their existence into question.” In his sanctions order, Judge Castel included his concern that “a future litigant may be tempted to defy a judicial ruling by disingenuously claiming doubt about its authenticity.” Judge Castel directed the two attorneys to each pay a $5,000 fine to the court, to notify their client, and to notify each real judge falsely identified as the author of the cited fake cases.
Last week in ransomware
Last week’s focus was on the BlackCat/ALPHV ransomware gang extorting Reddit and the ongoing MOVEit Transfer data breaches. BlackCat still plans to leak 80GB of the data after they say Reddit ignored a $4.5 million ransom demand. The situation with MOVEit escalated last week with the US government issuing an up to $10 million reward for information on the Clop ransomware operation being linked to a foreign government after it was revealed they breached numerous federal agencies. As expected, this massive breach has led to a class action lawsuit against Progress Software, the developers of MOVEit Transfer.