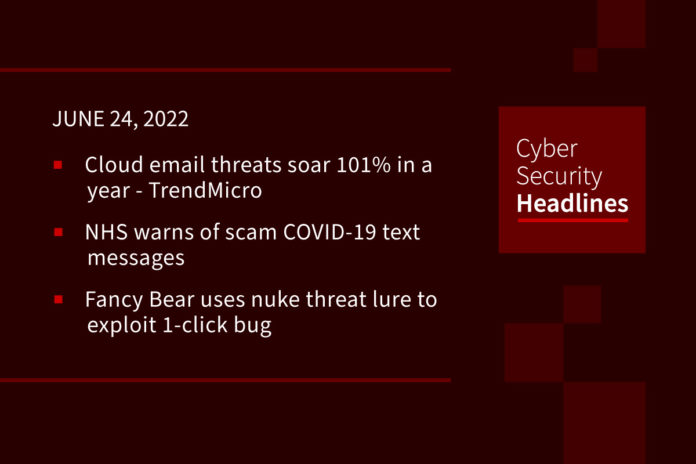
Cloud email threats soar 101% in a year
Trend Micro announced this number as their observation of growth in email-borne cyber-threats that they blocked last year. They also note a 138% year-on-year increase in phishing emails, of which 40% were credential phishing attempts. They also blocked 3.3 million malicious files in cloud-based emails, including a 134% increase in known threats and a 221% increase in unknown malware. Another security company, Proofpoint warned in a new report of the continued dangers posed by social engineering, highlighting how many users don’t realize that threat actors may spend considerable time and effort building a rapport over email with their victims, especially if they’re trying to conduct a business email compromise (BEC) attack, it said.
NHS warns of scam COVID-19 text messages
The UK’s National Health Service (NHS) is warning the public about a spate of fake messages, sent out as SMS text messages, fraudulently telling recipients of their exposure to the Omicron variant of COVID-19. The link leads to a lookalike website that pretends to belong to the NHS. The bogus website confirms that the test is free, but asks for 99 pence to cover postage. Its true mission, though, is to collect personal information including name and address. The fact that this is being reported in mid-June 2022 shows that Covid-related scams are still successful.
Fancy Bear uses nuke threat lure to exploit 1-click bug
APT group Fancy Bear is behind a phishing campaign that uses the specter of nuclear war to exploit a known one-click Microsoft flaw. The goal is to deliver malware that can steal credentials from the Chrome, Firefox, and Edge browsers. Researchers at Malwarebytes state that the group is pushing malicious documents weaponized with the exploit for Follina. Their campaign targets users with emails carrying a malicious RTF file called “Nuclear Terrorism A Very Real Threat” in an attempt to prey on victims’ fears that the invasion of Ukraine will escalate into a nuclear conflict, researchers said.
Chinese hackers distributing SMS bomber tool with malware hidden inside
Israeli cybersecurity company Check point said in a report that they had found a threat cluster, tied to the hacking group Tropic Trooper, uses a previously undocumented malware coded in Nim language. The novel malware, dubbed Nimbda, is “bundled with a Chinese language greyware ‘SMS Bomber’ tool that is most likely illegally distributed in the Chinese-speaking web,” used to strike targets as part of a newly discovered campaign. An SMS Bomber is a technique which, as the name mentions, renders a phone number unusable via a barrage of denial-of-service (DDoS).
Thanks to today’s episode sponsor, Optiv

• Increasing security
• Decreasing risk
• Lowering cost
Learn more at www.optiv.com/IAM-Microsoft.
New MetaMask phishing campaign uses KYC lures to steal passphrases
A new phishing campaign targets users on Microsoft 365 by spoofing the popular MetaMask cryptocurrency wallet provider and attempting to steal recovery phrases. According to email security firm Armorblox the new campaign distributes messages that resemble legitimate identity verification requests. They appear to be sent from MetaMask support and are spoofs of a Know Your Customer (KYC) verification request and features convincing branding and no typos or other obvious scam giveaways. KYC requests are part of standard anti-money laundering legal obligations financial companies must abide by, so receiving a request would not necessarily be unusual.
Critical PHP vulnerability exposes QNAP NAS devices to remote attacks
QNAP, the Taiwanese maker of network-attached storage devices, said on Wednesday it’s in the process of fixing a critical three-year-old PHP vulnerability that could be abused to achieve remote code execution. A vulnerability affects PHP versions in the 7.1. and 7.2 range. It is tracked as CVE-2019-11043, is rated 9.8 out of 10 on the CVSS scale. The alert comes a week after QNAP revealed that it’s “thoroughly investigating” yet another wave of DeadBolt ransomware attacks targeting QNAP NAS devices running outdated versions of QTS 4.x.
Microsoft’s AI spots ransomware attacks before they get started
Microsoft is focusing on disrupting the earliest stages of a ransomware attack with AI enhancements for Microsoft Defender for Endpoint. In what the company calls “early incrimination,” they are developing machine learning (ML) algorithms to determine “malicious intent” in files, processes, user accounts, and devices. Microsoft engineers have developed three sets of AI-generated inputs that independently generate a risk score determining whether an entity is likely involved in an active ransomware attack:
• Time-based and statistical analysis of security alerts at the organizational level
• Graph-based aggregation of suspicious events across devices
• Device-based monitoring to flag suspicious activities
By correlating these datasets, Defender can detect patterns and connections that might have been missed otherwise. If a high enough confidence level is reached, it automatically blocks the files and entities involved in the ransomware.
(ZDNet)
Amazon’s Alexa could turn dead loved ones’ voices into digital assistant
Claiming it will allow people to “make the memories last”, the company is developing technology that will allow its Alexa digital assistant to mimic the voice of anyone it hears from less than a minute of provided audio, Rohit Prasad, its senior vice-president and head scientist, said on Wednesday. He added that during the coronavirus pandemic “so many of us have lost someone we love”. They announced the existence of this technology from beyond the grave at the company’s re:Mars conference, focusing on its “ambient computing” achievements in the realms of machine learning, automation, robots, and space.