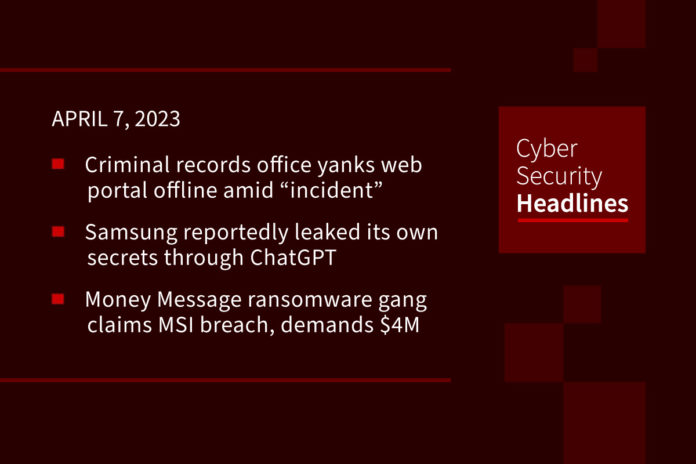
Criminal records office pulls web portal due to ‘cyber security incident’
ACRO is the UK’s criminal records office responsible that manages criminal record information and the exchange of records with other countries. It is now reviewing a “cyber security incident” that forced it to take pull its customer portal offline. In addition to managing people’s criminal record information, this government agency assists employers who are vetting potential hires, as well as embassies processing visa applications. The criminal record data data is drawn from UK’s Police National Computer via an information sharing agreement. The office confirmed by email that it has “recently been made aware of a cyber security incident affecting the website between 17th January 2023 and 21 March 2023,” adding “we have no conclusive evidence that personal data has been affected by the cyber security incident.”
Samsung reportedly leaked its own secrets via ChatGPT
According to The Register, “less than three weeks after Samsung lifted a ban on employees using ChatGPT, the company has reportedly leaked its own secrets at least three times.” The ban had been put in place to protect company data but was lifted to “enhance productivity and keep staff engaged with the world’s latest tech tools.” According to a Korean local media report, those now-leaked secrets include equipment measurement and yield data from the conglomerate’s device solution and semiconductor business unit. One employee told the local outlet they copied some problematic source code of a semiconductor database download program, entered it into ChatGPT, and inquired about a solution.
Money Message ransomware gang announces MSI breach
A new ransomware gang known as Money Message has listed Taiwanese PC parts maker MSI (Micro-Star International) on its extortion portal, having claimed to have stolen source code from the company’s network. MSI manufactures “motherboards, graphics cards, desktops, laptops, servers, industrial systems, PC peripherals, and infotainment products.” The group has posted “screenshots of what they claim to be the hardware vendor’s CTMS and ERP databases and files containing software source code, private keys, and BIOS firmware.” They have threatened to publish all these allegedly stolen documents in about five days.
Many workers willing to take a pay cut to work remotely, survey finds
A recent survey by recruiting firm Robert Half reveals that Americans have “grown so fond of working from home that many are willing to sacrifice pay on average up to 18% for the privilege of skipping the office.” Of more than 2,500 U.S. workers and 2,100 hiring managers polled, three-quarters of workers said they are “happier and more productive when they’re working from home despite sometimes having to work longer hours.” Such preferences are finding pushback from employers to get people back in the office. A recent Resume Builder survey found that nine out of 10 companies will require employees back to the office in 2023.
(CBS News)
Thanks to this week’s episode sponsor,

OCR Labs exposed, jeopardizing major banking clients
London-based OCR Labs, a provider of digital ID verification tools with clients that include BMW, Vodafone, the Australian government, HSBC, and Virgin Money, has stated that a misconfiguration of the company’s systems exposed sensitive credentials to the public. Although the issue has now been fixed, the data could be used by threat actors to breach a banks’ backend infrastructure and consequently the infrastructure of their clients. The discovered data leak specifically impacted financial institutions in Australia and the UK.
Google and Amazon find it difficult to lay off workers in Europe
US big tech companies are now learning how difficult it is to reduce headcount in Europe. As opposed to the US, where companies can announce widespread job cuts and let go of hundreds if not thousands of workers within months, in Europe, mass layoffs among tech companies have stalled because of labor protections that make it virtually impossible to dismiss people in some countries without prior consultations with employee interest groups. By law, companies are required to bargain with labor law councils before implementing layoffs — a sometimes lengthy process that includes information gathering, negotiations and the possibility of recourse. Because of these requirements, Google branches in Germany and France will be some of the last locations to be affected by the cuts, if even at all.
Law firm for Uber loses drivers’ data to hackers again
In this, the third data breach in six months for Uber, its law firm, Newark, NJ-based Genova Burns LLC, observed “suspicious activity at the end of January, and — after an investigation by outside specialists — discovered that its systems had been compromised and PII on an undisclosed number of Uber drivers had been stolen.”
Hackers launch a DDoS attack against CheckPoint
Hacker group Anonymous Sudan has launched a DDoS attack on Israel-based cybersecurity company Check Point. The attackers promise to launch a stronger version of a similar attack today, April 7th with the intent of taking down the website. As of this recording, the CheckPoint website has been restored. At the same time Anonymous Sudan allegedly attacked several websites belonging to Israeli universities including Tel Aviv University, The Hebrew University of Jerusalem, Ben-Gurion University of Negev, Haifa University, Weizmann Institute of Science, Open University of Israel, and Reichman University.