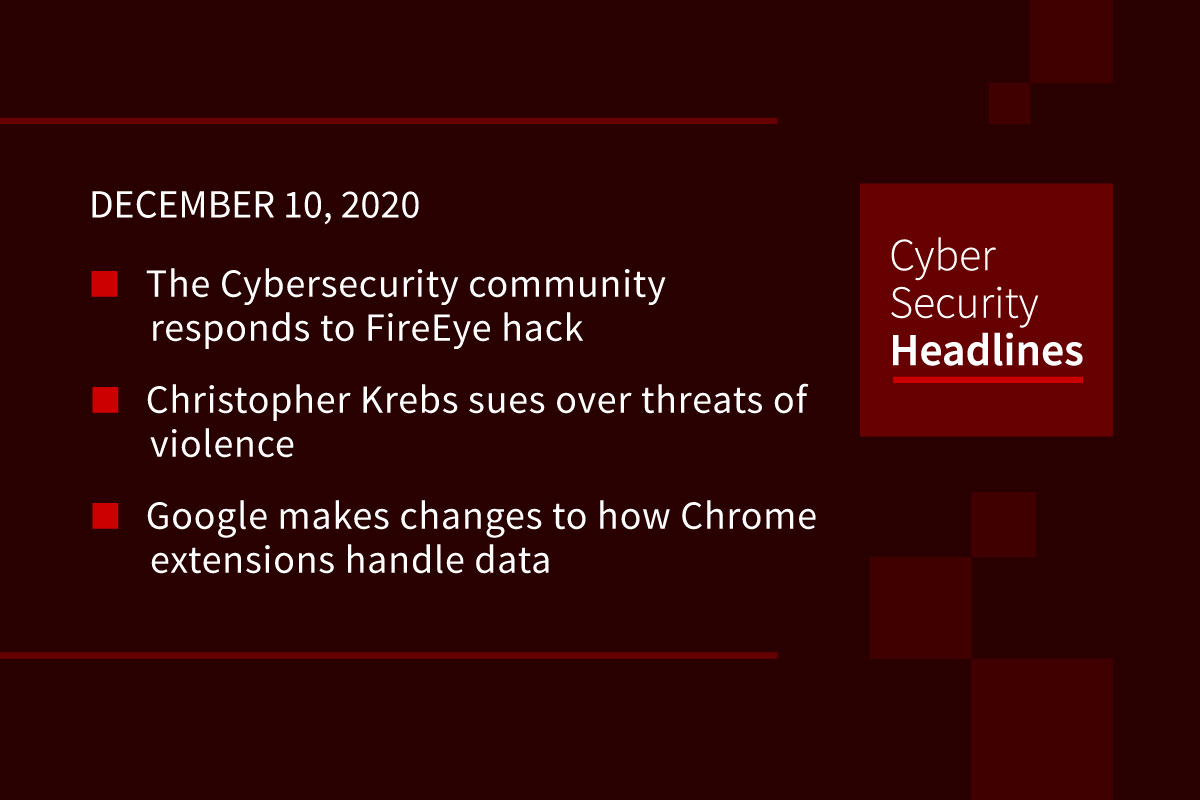
The Cybersecurity community responds to FireEye hack
On Tuesday, FireEye revealed it was hacked and its “Red Team” software it uses for penetration testing was stolen. The Washington Post reported those responsible for the breach were from a group known as APT 29 or Cozy Bear, attributed to Russia’s SVR foreign intelligence service. This appears to be a retaliatory strike and hacker critics say the tools stolen probably won’t provide any additional capability to the Russians’ extensive and impressive library of exploits. While some in the cyber community shifted to victim blaming, others posted in social media supporting FireEye’s offering of countermeasures. Most cyber professionals know that being a victim is a matter of “when”. How you handle it is what counts.
(Wired)
Christopher Krebs sues over threats of violence
The lawsuit was filed in Maryland against attorney Joseph diGenova, who called for Krebs’ death on a newscast. The lawsuit alleges that the former CISA director has been “bombarded” with similar threats since then, requiring his family to move out of their Virginia home and hire private security. Krebs is seeking financial damages from diGenova, the TV network Newsmax and the Trump campaign over “serious fear, distress, suffering, and even physical damage” caused by the comments. Krebs was fired from CISA on November 17th for maintaining that the US presidential election was fair and free from interference.
(Lancaster Online)
Google makes changes to how Chrome extensions handle data
Google announced the changes at its Chrome Dev Summit 2020. Starting on January 18, 2021, the day before the release of Chrome 88, Google will require all extensions to publicly display their privacy practices. Google will also show if a developer has certified that extensions use data primarily for the benefit of users, that they do not sell any data collected, and that data won’t be used for personalized advertising. Going forward users will also be able to specify which web page an extension can pull data from, previously extensions made this determination.
YouTube to remove content alleging widespread voter fraud
The video hosting giant said this was a continuation of its existing Community Guidelines that forbid spreading misinformation on where to vote and disputing the results of historical US Presidential elections. Given that enough states have certified election results to officially determine the President-elect, YouTube will remove content alleging voter fraud for videos going forward.
In related news, Axios’ sources say that Google informed advertising partners that it will lift its post-election political ad ban as of today.
Thanks to our episode sponsor, Code42

Credit card skimmers found hiding in CSS files
This novel approach to hiding the MageCart script was found by the security researchers at Sansec, impacting three shopping sites. Implanting the script in CSS seemingly prevented detection by automated systems, with the researchers saying it would be difficult to detect with even a manual audit. The script starts running when customers start inputting checkout information on a compromised site. When clicking the checkout button, customers are redirected to a new page that loads and parses the attackers’ malicious CSS code.
Cybercriminals spotted exploiting COVID-19 vaccine anxiety
Security researchers at KnowBe4 say they’ve seen a slew of new attacks, from phishing attacks to malware campaigns, using vaccine references for social engineering. This was also seen by researchers at Intezer, who discovered a new Zebrocy malware sample that included a slide show purportedly from a Chinese pharmaceutical company working on a vaccine to use as a spear-phishing lure. Other email-based attacks included messages encouraging recipients to fill out a form to get on a COVID-19 vaccine distribution list.
DHS and CISA urge patching OpenSSL vulnerabilities
OpenSSL recently issued fixes to two high severity Denial of Service vulnerabilities. These vulnerabilities impact how OpenSDL handles CRL Distribution Points in URLs, which could allow an attacker to create a malicious SSL certificate that would crash OpenSSL. CISA is advising admins to patch this immediately, in hopes to avoid the situation with Heartbleed in 2014, which saw rampant exploitation in the wild.
Data loss events on the rise in the UK
According to the Q2 report from the UK’s Information Commissioner’s Office, data loss events increased 79% from Q1, with 2594 reported incidents. Of these 737 were categorized as cybersecurity events, up 78% on the quarter, which were most commonly related to phishing, ransomware, and unauthorized access. Of the non-cybersecurity events, 43% of the events were the result of emailing or faxing data to the wrong recipient, and leaving paperwork in insecure locations. Some of this rise comes from the increase in remote working, with security analysts noting that employees are transmitting data more often in general, and lacking proper facilities at home to dispose of data securely.