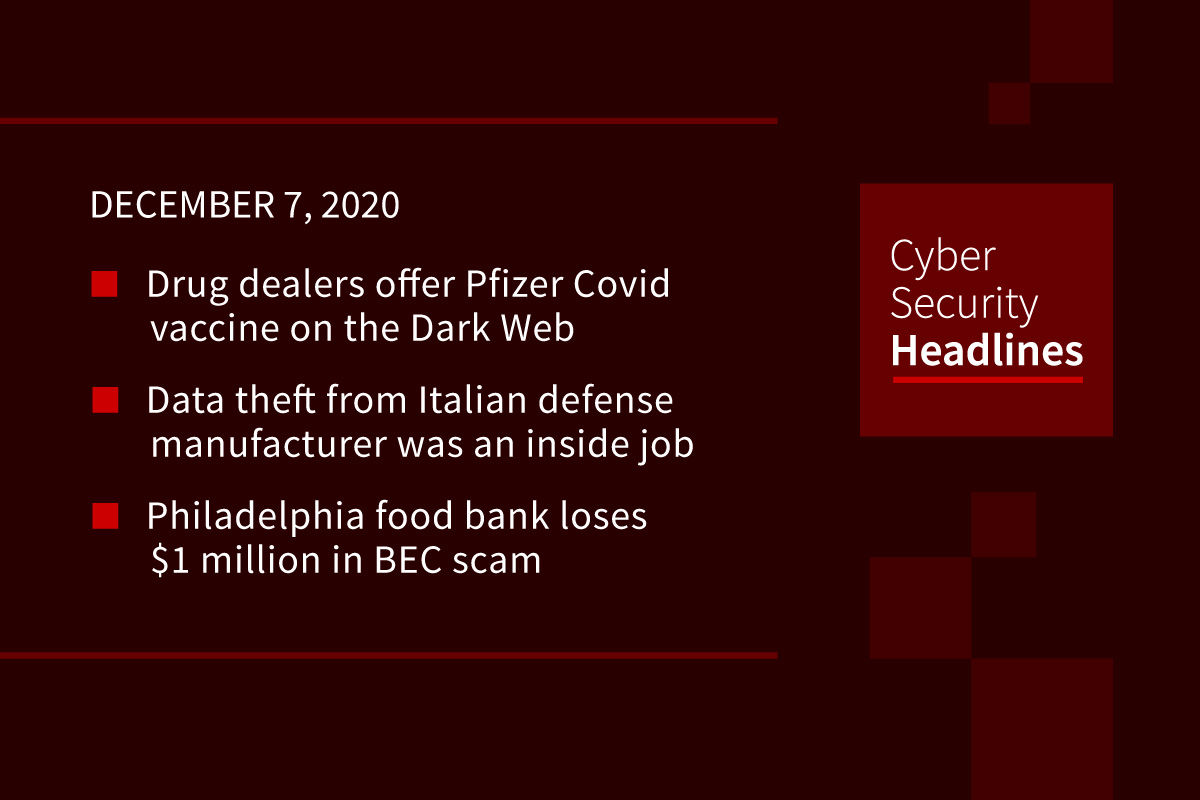
Drug dealers offer Pfizer vaccine on the Dark Web
With the United Kingdom becoming the first Western country to authorize a Covid-19 vaccine and announce distribution plans and the first doses expected to be rolled out next week, numerous darknet vendors are already offering doses of the Pfizer/BioNTech vaccine for sale for up to $1300 each. It is unknown whether these doses are real, or simply a typical scam accompanied by realistic imagery, but the vendors claim to have obtained the doses through government suppliers. The Pfizer vaccine must be kept at minus-70 degrees Celsius, meaning it cannot be shipped by mail or courier, which makes it unclear how the sellers are managing and shipping the doses.
Data theft from Italian defense manufacturer was an inside job
Italian police have arrested two people in relation to the theft of 10 gigabytes of confidential data including military designs from the Leonardo corporation, one of the world’s largest defense contractors. One of the suspects was an employee of Leonardo’s IT security management department and the other was head of its Cyber Emergency Readiness Team. The two used USB keys to infect 94 workstations with an undetectable trojan disguised as a Windows executable, that then exfiltrated data to an external server.
Philadelphia food bank loses $1 million in BEC scam
The hunger relief group Philabundance fell victim to a Business Email Compromise scam when they paid a bogus invoice for over $923,000 for construction of a community kitchen. The error was only realized 18 days later, when the genuine construction company asked for payment. Earlier this year, the FBI said BEC scams had defrauded companies of some $1.7 billion during 2019.
Kazakhstan government intercepts HTTPS traffic in its capital
For the third time since 2015 the Kazakhstan government is installing a root certificate on its citizens’ devices. Described as a cybersecurity exercise, the move forces citizens in its capital of Nur-Sultan (formerly Astana) to install a digital certificate on their devices if they want to access foreign internet services, allowing it to intercept all HTTPS traffic made from users’ devices. Representatives for major browser makers, who succeeded in blocking the government’s previous blocking attempts have not commented, but are expected to block this certificate as well.(ZDNet)
Thanks to our episode sponsor, Code42

TikTok emerges as dubious source of financial learning for Gen-Z
Videos showing questionable financial management techniques have become a hot commodity for the TikTok audience base, which HootSuite estimates to be mostly aged 13 to 24 years. Videos by admittedly unqualified experts are experiencing millions of downloads as TikTok emerges as a preeminent source of knowledge packaged in short, easy to digest video formats. Industry watchers state that TikTok’s proprietary algorithm for selecting videos, along with its meteoric rise during pandemic lockdown make it something to be taken seriously as a medium with considerable influence.
Payment card skimmer scripts hidden inside social media sharing icons
Newly discovered malware that injects payment card skimmer scripts into compromised online stores is being hidden inside social media buttons that mimic those found on Facebook, Twitter, and Instagram. The JavaScript-based scripts are injected by Magecart cybercrime groups in the checkout pages of compromised e-commerce sites, which then automatically harvest payment and personal information submitted by customers. Cybersecurity experts call this an example of steganography – the practice of concealing a message within another file. Its use of valid images makes the code extremely difficult to detect.
Egregor ransomware strikes K-Mart and Vancouver transit
K-Mart’s new owners, Transformco, received an unwanted year-end surprise last week at the hands of the prolific Egregor gang, which encrypted devices and servers connected to the company’s networks, knocking out back-end services, and delivering a ransom note that claims to have compromised Kmart’s Windows domain. At the same time, the City of Vancouver’s public transportation network, Translink, was also hit by Egregor, leaving users unable to use their metro cards or buy tickets at kiosks.
(Threatpost + Threatpost)
Ransomware extortion escalates to cold calling companies who restore backed up data
In an attempt to increase pressure, ransomware gangs are turning to call centers to phone their victims who they suspect might try to restore seized data from backups rather than pay the ransom. Conti, Ryuk, and the now defunct Sekhmet and Maze have been known to make these calls, and experts note that the script used by the callers is similar among them, all suggesting a pooled use of call centers resources. Experts warn that such calls might be mistaken for legitimate IT support calls among unprepared employees.
(ZDNet)