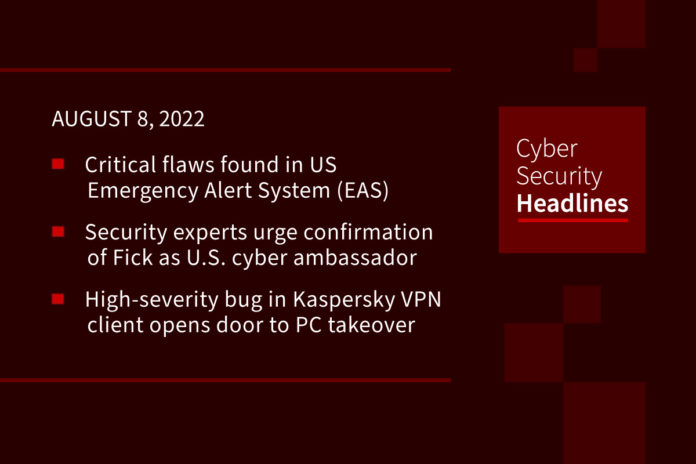
Critical flaws found in US Emergency Alert System
The US government is warning of critical vulnerabilities in its Emergency Alert System (EAS) that, if exploited, could enable intruders to send fake alerts out over television, radio, and cable networks. The Department of Homeland Security (DHS) said in an advisory it was recently informed about the flaws in EAS encoder and decoder devices, adding that they were successfully exploited by Ken Pyle, a security researcher at cybersecurity firm CYBIR. There is a sense of urgency to the advisory because the exploit “may” be presented, with proof of concept code, at the DEF CON conference in Las Vegas next week. The DHS is urging organizations that operate the EAS to ensure that their devices and supporting systems are updated with the most recent software versions and security patches, are protected by a firewall, and are monitored, with audit logs being regularly reviewed to ensure there is no unauthorized access.
Security experts urge Fick’s speedy confirmation as first U.S. cyber ambassador
A bipartisan group of 106 national security experts, former government officials and industry leaders sent the Senate Foreign Relations Committee a letter Tuesday endorsing Nate Fick to serve as the State Department’s first ambassador at large for cyberspace and digital policy, according to a copy of the letter obtained by CyberScoop. The letter emphasized the cyberthreats the U.S. faces and highlights Fick’s unique resume. If confirmed, Fick will step into a role overseeing three policy channels dedicated to cyberspace security, communications and information and digital freedom. The Bureau of Cyberspace and Digital Policy that Fick would take over is an expanded effort that builds on what had been a smaller and more diffuse cybersecurity portfolio at the State Department.
High-severity bug in Kaspersky VPN client opens door to PC takeover
Tracked as CVE-2022-27535 this bug is a local privilege-escalation security vulnerability in the security software that threatens remote and work-from-home users. It exists in the Support Tools part of the application, and would allow an authenticated attacker to trigger arbitrary file deletion in the system, along with privilege escalation to SYSTEM. “It could lead to device malfunction or the removal of important system files required for correct system operation,” according to a Kaspersky spokesperson. Kaspersky has fixed the issue, and users should update to version 21.6 or later to patch their systems.
Thanks to today’s episode sponsor, Edgescan

Massive cyberattack hits German Chambers of Industry and Commerce
The email and website of the German Chambers of Industry and Commerce (DIHK) – an organization representing millions of businesses – are still down as it tries to recover from a cyberattack that began on Thursday. The organization did not respond to requests for comment but said on Twitter that only its phone system is still working. The DIHK helps companies with legal issues, provides general support, and promotes German businesses internationally. The attack, which carried the hallmarks of a ransomware incident, was having downstream effects on the 79 local arms of the organization, including offices in Frankfurt, Cologne, Berlin.
Iran-linked Lyceum Group adds a new weapon to its arsenal
The Lyceum group, which has been active since 2017 and is a state-sponsored Iranian APT group, generally targets Middle Eastern organizations most notably in the energy and telecommunication sectors, and they rely heavily on .NET based malwares. Researchers from Zscaler have stated that they recently observed a new campaign where the Lyceum Group was utilizing a newly developed and customized .NET based malware targeting the Middle East by copying the underlying code from an open source tool and using a .NET based DNS backdoor.
Apple tells suppliers to use “Taiwan, China” or “Chinese Taipei” to appease Beijing
This rule, which applies to its suppliers in Taiwan means that all components manufactured there must be label in such a way as to describe Taiwan as a province of the People’s Republic of China (PRC). According to Japanese financial publication Nikkei, this is due to China has ramping up enforcement of a long-standing import rule. While China and the US have allowed the status of Taiwan to remain ambiguous over the years, observers at The Register suggest this may be a repercussion from last week’s visit ot Taiwan by Nancy Pelosi, an action that did not sit well with the Chinese government.
Last week in ransomware
According to Bleeping Computer, last week was a relatively quiet one on the ransomware front. Mandiant revealed that an Iranian threat actor is behind ransomware attacks on the Albanian government. Microsoft announced this week that new Windows 11 builds in the Beta Channel had improved Microsoft Defender for Endpoint ransomware attack blocking capabilities. Ransomware attacks of interest included ones on the Spanish National Research Council (CSIC), Semikron getting hit by LV ransomware, the German Chambers of Industry and Commerce as we just reported on, and Creos Luxembourg. The Hive group attacked two private schools in England, basing their ransom demands on their research into the school’s ransomware insurance policy.