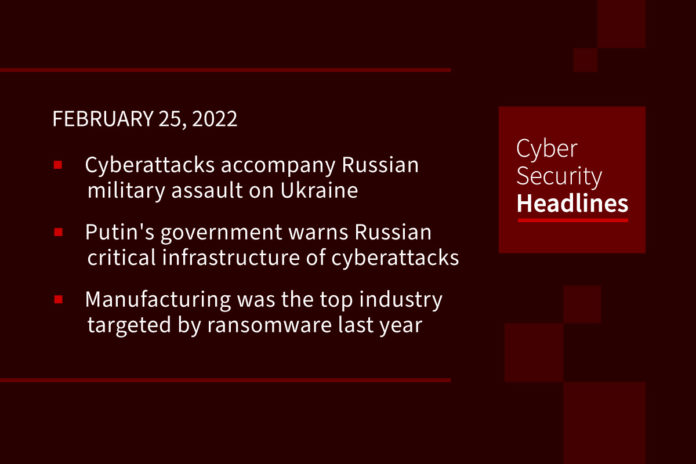
Cyberattacks accompany Russian military assault on Ukraine
The websites of Ukraine’s defense, foreign and interior ministries were unreachable or painfully slow to load Thursday morning after a punishing wave of distributed-denial-of-service attacks as Russia struck at its neighbor. In addition to DDoS attacks on Wednesday, cybersecurity researchers said unidentified attackers had infected hundreds of computers with destructive malware, some in neighboring Latvia and Lithuania. ESET Research Labs said it detected a previously unseen piece of data-wiping malware Wednesday on “hundreds of machines in the country.” It was not clear how many networks were affected.
Putin’s government warns Russian critical infrastructure of potential cyberattacks
The Russian government warned its domestic critical infrastructure operators Thursday of the “threat of an increase in the intensity of computer attacks,” and said that any failure in the operation of critical infrastructure that doesn’t have a “reliably established” cause should be considered “the result of a computer attack.” It continued, “attacks can be aimed at disrupting the functioning of information resources and services, causing reputational damage, including for political purposes, to form a negative image of the Russian Federation in the eyes of the world community.” The warning did not specify where such attacks might come from.
Manufacturing was the top industry targeted by ransomware last year
According to a new report from IBM, the X-Force Threat Intelligence Index, the manufacturing industry was the most attacked sector,accounting for 23% of reports of ransomware. The “ripple effect” of disruption caused their “downstream supply chains to pressure them into paying the ransom and ransomware actors are capitalizing on operational stressors exacerbated by the pandemic,” claimed the report. The report found that 47% of attacks on the manufacturing industry relied upon vulnerabilities that organizations had either failed to patch or could not patch, suggesting a weakness in prioritizing vulnerability management.
(Tripwire)
US and UK expose new malware used by MuddyWater hackers
New malware is being deployed by the Iranian-backed MuddyWater hacking group in attacks targeting critical infrastructure worldwide. This was revealed yesterday in a joint advisory issued by CISA, the FBI, the NSA, US Cyber Command’s Cyber National Mission Force, and the UK’s National Cyber Security Centre. MuddyWater is “targeting a range of government and private-sector organizations across sectors—including telecommunications, defense, local government, and oil and natural gas—in Asia, Africa, Europe, and North America,” the two governments said, using multiple malware strains to deploy second-stage malware on compromised systems, for backdoor access, to maintain persistence, and for data exfiltration.
Thanks to our episode sponsor, Tines
Defense contractors hit by stealthy SockDetour Windows backdoor
A new custom malware dubbed SockDetour found on systems belonging to US defense contractors has been used as a backup backdoor to maintain access to compromised networks. The malicious payload was spotted by Unit 42 security researchers, who believe that its operators kept the backdoor under the radar for a long time as it has been used in the wild since at least July 2019. SockDetour’s stealthiness can be explained by the fact that it “operates filelessly and socketlessly” on infected Windows servers by hijacking network connections, making it a lot harder to detect at the host and network levels. The connection hijacking is done using the legitimate Microsoft Detours library package used for Windows API call monitoring and instrumentation.
Cyberattackers leverage DocuSign to steal Microsoft Outlook logins
A sophisticated phishing campaign directed at a “major, publicly traded integrated payments solution company located in North America” made use of DocuSign and a compromised third party’s email domain to skate past email security measures, with the goal of stealing Microsoft login credentials, researchers at Armorblox revealed. Around 550 members of the targeted company received the same email in their inboxes, which was an email requesting signature on a revised contract. The phishing emails successfully evaded traditional email security measures in part because they came from a domain belonging to TermBrokersInsurance. The report noted that “a quick scan of the domain address would not have alerted the end user of fraudulent activity because of the domain’s validity.
US winds up national security team dedicated to Chinese espionage
The United States’ National Security Division will wind up its “China Initiative” – an effort to combat what then-attorney general Jeff Sessions described in 2018 as “systematic and calculated threats” posed by Beijing-backed economic espionage. On Wednesday assistant attorney general Matthew Olsen said it’s time for the Initiative to be wound up, because it has proven divisive and doesn’t represent the most appropriate approach to combating China.
Almost 100,000 new mobile banking Trojan strains detected in 2021
Malware developers are shifting part of their focus to the creation of mobile threats. Many of the traditional infection routes are still workable — including phishing and the download and execution of suspicious software — but cyberattackers are also known to infiltrate official app stores, including Google Play, to lure handset owners into downloading software that appears to be trustworthy. Recent examples of Trojans ending up in Google Play include Joker and Facestealer. According to new research published by Kaspersky, 97,661 new mobile banking Trojan variants were detected in 2021, alongside 17,372 new mobile ransomware Trojans and a total of 3,464,756 malicious installation packages, .APKs that can be installed on jailbroken devices or those that accept apps from unknown developers.
(ZDNet)