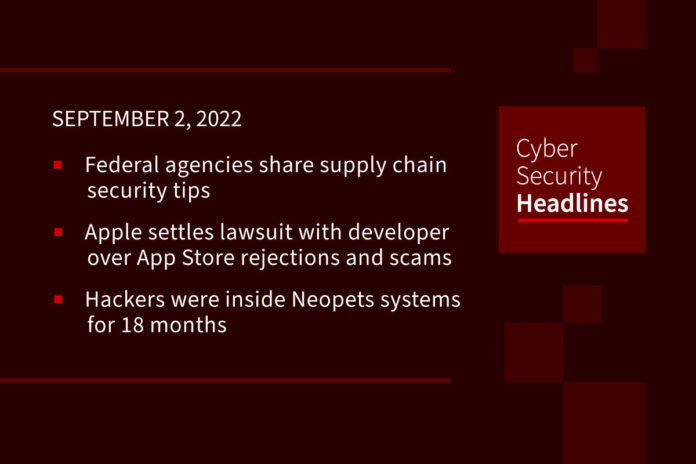
Federal agencies share supply chain security tips
On Thursday, the National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) released tips for securing software supply chains. The guidance was designed by the Enduring Security Framework (ESF), a public-private partnership that addresses threats to US critical infrastructure. The NSA said, “ Developers will find helpful guidance from NSA and partners on developing secure code, verifying third party components, hardening the build environment, and delivering the code. Until all DevOps are DevSecOps, the software development lifecycle will be at risk.” The ESF plans to release two more supply chain-focused advisories focusing on software suppliers and customers.
Apple settles lawsuit with developer over App Store rejections and scams
Apple has settled a lawsuit with its latest disgruntled app developer, and former Pinterest engineer, Kosta Eleftherioua. Eleftherioua filed the suit back in March 2021 alleging his FlickType Apple Watch keyboard app had been unfairly rejected from the App Store and then targeted by scammers. Apple rejected FlickType from the App Store because it offered a poor user experience, but then approved apps using an integrated version of FlickType. Later, Apple decided to let FlickType into the App Store, but its success made it a target for App Store scammers who launched inferior competitors boosted by fake ratings and reviews, causing FlickType’s revenue to plummet from $130,000 to just $20,000. The terms of the settlement have not been disclosed.
Hackers were inside Neopets systems for 18 months
Earlier this year, virtual pet peddler Neopets, suffered a pretty devastating data breach as we reported here on Cyber Security Headlines. This week, the company divulged new details about the incident, revealing that cybercriminals were able to linger inside its systems for about 18 months. The company issued a statement indicating that data for past and present Neopets players was affected including name, email address, username, date of birth, gender, IP address, Neopets PIN, hashed password, as well as data about a player pets. A hacker named “TarTarX,” was detected trying to sell off the data back in July. It’s unclear whether anybody ever took them up on that offer. Neopets has reset player passwords, is offering to help protect against identity theft and is in process of adding multi-factor authentication to its site.
(Gizmodo)
Microsoft will disable Exchange Online basic auth next month
Microsoft warned customers Thursday that it will finally disable basic authentication in tenants worldwide to improve Exchange Online security. The announcement follows multiple reminders and warnings the company has issued over the last three years. Beginning October 1, 2022, Microsoft will pick random tenants and disable authentication access for MAPI, RPC, Offline Address Book (OAB), Exchange Web Services (EWS), POP, IMAP, Exchange ActiveSync (EAS), and Remote PowerShell. Customers will still be able to re-enable basic auth until the end of year after which the feature will be permanently disabled.
Thanks to today’s episode sponsor, Code42

Code42 Incydr is an Insider Risk Management SaaS that provides a comprehensive understanding of your data exposure and shows which activities require security intervention. Learn more at Code42.com/showme.
Source code for 1800 Android and iOS apps serves up AWS creds
The Symantec Threat Hunter team has spotted 1859 apps across Android and iOS containing hard-coded Amazon Web Services (AWS) access tokens that permitted access to private AWS cloud services. Symantec’s advisory reads, “The AWS access tokens could be traced to a shared library, third-party software development kit (SDK), or other shared component used in developing the apps.” Symantec said some reasons for hard-coding access keys include downloading or uploading assets required by the app, accessing configuration files, and accessing cloud services. The company recommends adding security scans to the application development lifecycle and checking mobile app report cards for any outsourced applications.
Blue badges used as bait in Instagram phishing attack
A new Instagram phishing campaign has been spotted attempting to lure thousands of users with an offer to issue them a coveted blue-badge, signaling a verified account. The phishing emails direct victims to forms branded with Instagram, Facebook, WhatsApp, Messenger, and Meta logos. The forms collect name, email, phone number and ultimately account password to “verify” the account. Users should be aware that social media platforms will never contact them offering a blue badge, they can only be obtained by applying through the official platform. Further, Instagram blue badges are reserved for notable public figures, celebrities, and brands.
Parental oversight of child online activity found lacking
A new survey in the UK (conducted by Censuswide and the International Cyber Expo) found that 34% of parents are unaware of what online accounts their children are using. While roughly 20% of parents claim to know about all their children’s accounts, they admit to being unable to easily monitor online activities and who their children are interacting with. Fifteen percent of the respondents admitted allowing their children to have total online freedom. Online bullying appears to be an issue, with 14% of parents admitting their children have bullied or trolled others. Roughly the same percentage have children who experienced cyberbullying. Over half (54%) of perpetrators and 41% of bullying victims are 10 years old or younger.
TSA tests drone detection technology at LAX airport
The Transportation Security Administration (TSA) has begun testing technology designed to detect, track and identify (DTI) unmanned aircraft systems (UAS) entering restricted airspace around Los Angeles International Airport (LAX). So far this year, approximately 38 drones have been visually detected at LAX, including a drone that was reported within 700 feet of an aircraft several days before Super Bowl LVI. LAX joins Miami International Airport as one of two locations testing drone detection technology in an operational airport environment.