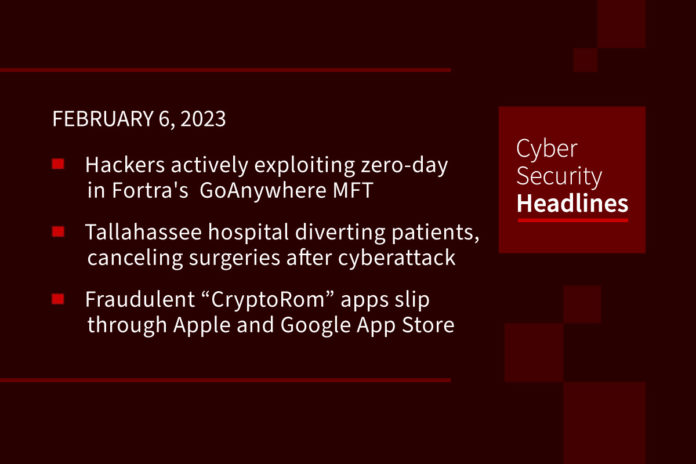
Hackers actively exploiting zero-day in Fortra’s GoAnywhere MFT
Fortra’s GoAnywhere managed file transfer application is being actively exploited in the wild by zero-day vulnerability. The vulnerability involves remote code injection “that requires access to the administrative console of the application, making it imperative that the systems are not exposed to the public internet.” Security researcher Kevin Beaumont states “there are over 1,000 on-premise instances that are publicly accessible over the internet, a majority of which are located in the U.S.”
Tallahassee hospital diverting patients, canceling non-emergency surgeries after cyberattack
Tallahassee Memorial HealthCare, which serves a 21-county region in north Florida and south Georgia have taken their IT systems offline due to a security issue that began on Thursday night and is suspected to be ransomware. They are diverting EMS patients and are only accepting Level 1 traumas from our immediate service area. All non-emergency surgical and outpatient procedures have been canceled and rescheduled, the hospital said in a statement on Friday.
Fraudulent “CryptoRom” apps slip through Apple and Google App Store review process
CryptoRom is used to coordinate romance scams with the aim of stealing cryptocurrency from victims. While this is nothing new in itself, it appears that apps perpetrating the scam can be downloaded from the official Apple and Android app stores – giving them greater apparent validity. In two separate examples that bypassed Apple’s App Store review, a legitimate-looking app initially communicates with a benign back end, where nothing malicious can be seen. Only after the app is accepted, downloaded, and launched does the developer switch domains from the benign back end to a malicious server that delivers the malicious content.
Musk says Twitter will provide a free write-only API to bots providing ‘good’ content
In an apparent contradiction to last week’s announcement that it would be shutting down free access to its APIs starting February 9, Twitter chief Elon Musk has now stated that after receiving feedback from developers, Twitter will provide a write-only API for “bots providing good content that is free.” There is no information on what constitutes “good content” and who will decide that. This follows last week’s shuttering of API access to third-party clients saying they broke a “long-standing rule” without any specification.
Thanks to this week’s episode sponsor, CISO Series

Massive ESXiArgs ransomware attack targets VMware ESXi servers worldwide
According to Bleeping computer, “admins, hosting providers, and the French Computer Emergency Response Team (CERT-FR) warn that attackers are actively targeting VMware ESXi servers unpatched against a two-year-old remote code execution vulnerability to deploy a new ESXiArgs ransomware.” CERT-FR said, “these attack campaigns appear to be exploiting the vulnerability CVE-2021-21974, for which a patch has been available since 23 February 2021. The systems currently targeted would be ESXi hypervisors in version 6.x and prior to 6.7.”
NY attorney general forces spyware vendor to alert victims
The AG’s office has also announced a $410,000 fine for a stalkerware developer who used 16 companies to promote surveillance tools illegally. “Patrick Hinchy, the spyware vendor, also agreed to alert his customers’ victims that their phones are being secretly monitored using one of his multiple apps, including Auto Forward, Easy Spy, DDI Utilities, Highster Mobile, PhoneSpector, Surepoint, or TurboSpy.” The apps enabled Hinchy’s customers to secretly monitor what other individuals were doing on their mobile devices, including location, browsing history, call logs, text messages, photos and videos, email activity, WhatsApp and Skype chats, and social media activity.
Vulnerabilities could let hackers remotely shut down EV chargers, steal electricity
According to a report from cybersecurity firm Saiflow, “two vulnerabilities in a commonly used networking protocol for electric vehicle chargers could allow hackers to remotely shut down charging stations or manipulate docking stations to recharge for free.” Ron Tiberg-Shachar, CEO of Saiflow, which sells cybersecurity services to the EV charger market, says, “if a hacker exploits these two vulnerabilities, he can create a denial of service which would mean disrupting or disconnecting a single charger or at scale they can execute distributed denial of service which would mean taking down and disconnecting all chargers connected to that network, imitating and hijacking a connection between the charger and the management platform.
Last week in ransomware
In addition to the VMware ESXi server attack covered earlier in this podcast,we saw new research released last week, with Microsoft warning that over a 100 ransomware gangs and over 50 unique ransomware families are currently active in the ransomware field. Also, LockBit has decided to create a new decryptor based on Conti. REsecurity released a report on the new Nevada ransomware-as-a-service recruiting and gearing up for future attacks. APT groups are using ransomware TTPs as cover for intelligence gathering and sabotage. Schools in Tucson, Arizona, and Nantucket, Massachusetts suffered cyberattacks, with one confirmed to be a Royal ransomware attack. Arnold Clark confirmed data was stolen in a December ransomware attack, and a ransomware attack on the ION Group disrupted the derivatives trading market in London England.