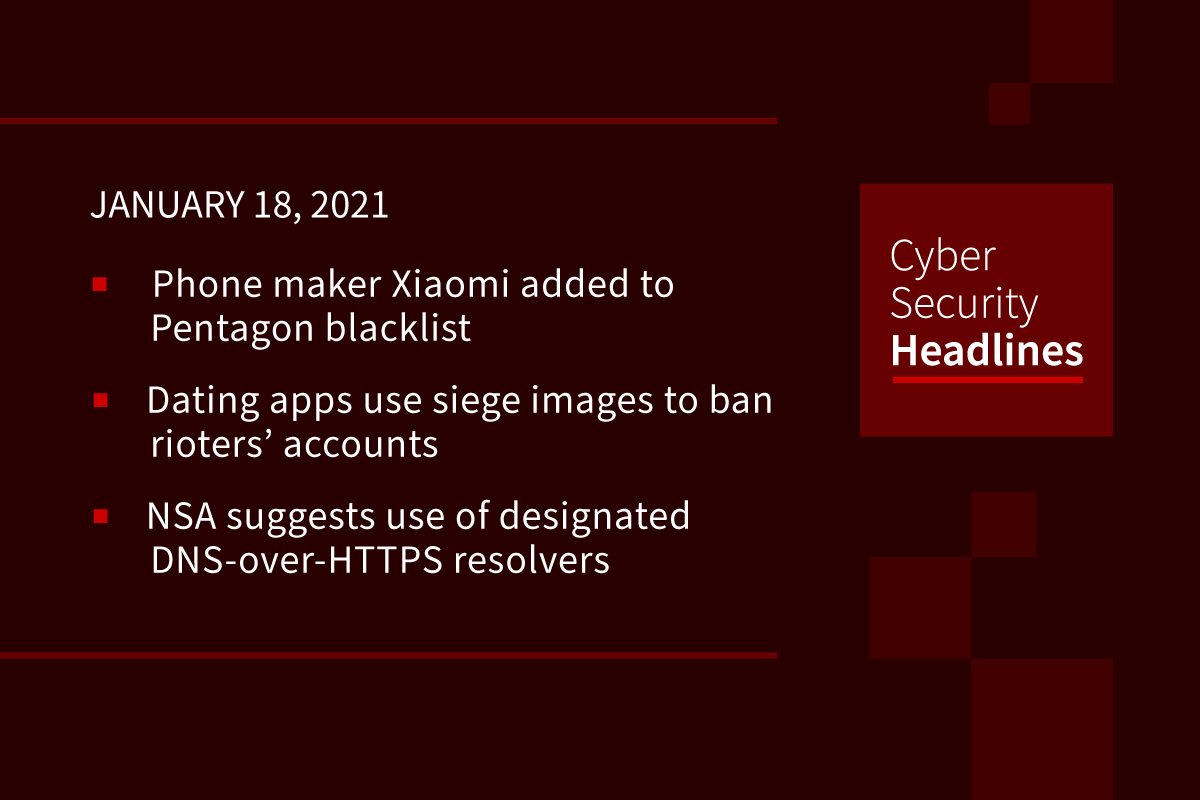
Xiaomi added to Pentagon blacklist
Nine Chinese firms have been added to the Pentagon’s blacklist of alleged ties to the Chinese military, including phone maker Xiaomi. This latest round of restrictions announced on Thursday affect, among others, China’s oil giant CNOOC and Xiaomi, which in November surpassed Apple to become the world’s third-biggest smartphone manufacturer. Being blacklisted requires a special license before these companies can receive exports of high-tech items from US suppliers. Many believe this latest action is President Trump’s final swipe at Chinese companies before President-elect Joe Biden’s inauguration on 20 January, although industry watchers suggest at least one more is to come.
(BBC News)
Dating apps are using images from the siege to ban rioters’ accounts
Tinder, Bumble and other dating apps are using images captured from inside the Capitol siege and other evidence to identify and ban rioters’ accounts. The apps have also turned into hunting grounds, with members striking up conversations with rioters, gathering potentially incriminating photos or confessions, then relaying them to the FBI. This has now become a viral pursuit, with tips shared on Twitter and some members changing their location on the dating apps to Washington, D.C., in hopes of ensnaring a potential suspect.
NSA suggests enterprises use designated DNS-over-HTTPS resolvers
If configured appropriately in enterprise environments this can help prevent numerous initial access, command-and-control, and exfiltration techniques used by threat actors, the agency said on Friday. DoH encrypts DNS requests by using HTTPS to provide privacy, integrity, and ‘last mile’ source authentication. This helps reduce threats from DNS queries being sent over an unencrypted connection, which allows for third-party eavesdropping, malware delivery and man-in-the-middle (MiTM) attacks.
Link found between data breaches and increased number of fatal heart attacks at US hospitals
A new study from Vanderbilt’s Owen Graduate School of Management and the Vanderbilt University Medical Center shows security remediation initiatives put into place after a hospital data breach, such as stronger passwords and authentication procedures leads to a rise in the time to EKG and in patient mortality rates for heart attack victims. The average increase in time to EKG was by 2.7 minutes, a significant delay considering the industry standard for time to EKG is 10 minutes. This increase was still observable years after a breach had occurred.
Thanks to our episode sponsor Armis

Search Engine DuckDuckGo grew 62% in 2020
DuckDuckGo is a search tool that compiles information through its own DuckDuckBot crawler, indexing WikiPedia, and through partners like Bing. Its search engine does not use any data from Google. It also does not track your searches to build a user profile or share any personal or identifying data with third-party companies, including ad networks. This has resonated with users who are seeking more privacy while using the Internet and reflects similar actions with recent concerns regarding data sharing between WhatsApp and Facebook.
Security researcher saves top-level domain that went forgotten
The domain, scpt-network.com, was one of two nameservers for the .cd country code top-level domain, assigned to the Democratic Republic of Congo, a domain that had the potential to redirect millions of internet users to rogue websites. Fredrik Almroth, a security researcher and co-founder of cybersecurity startup Detectify, found this critical domain name about to expire and assumed the Congolese government would pay to reclaim it. They did not. When top level domains are overtaken, regardless of country, they have the potential to expand into hacking and espionage, as evidenced by the DNSpionage campaign exposed by FireEye in 2019.
Trend Micro predicts AI will replace cybersecurity jobs and boost crime
In its 2021 predictions report, Trend Micro states that 32% of 500 IT leaders polled believe AI will replace all cybersecurity roles by 2030, and that 19% say attackers using AI will be commonplace by 2025, especially focusing on home networks as a critical launch pad to compromising corporate IT and IoT networks. 24% of the IT leaders polled also claimed that by 2030, data access will be tied to biometric or DNA data, making unauthorized access impossible. They suggested companies and IT professionals continue to evolve to keep pace.
(ZDNet)
BugTraq security mailing list shuts down after 27 years – or does it?
One of the cybersecurity industry’s first mailing lists dedicated to publicly disclosing security flaws, announced that it would be shutting down on January 31, 2021. Established in 1993, BugTraq provided the first centralized portal where security researchers could expose vulnerabilities after vendors refused to release patches. This was a time when such announcements details were often controversial, sometimes resulting in legal threats. However a post at seclists.org dated yesterday, January 17, suggests that Accenture Security has now decided to keep it running.
(ZDNet)