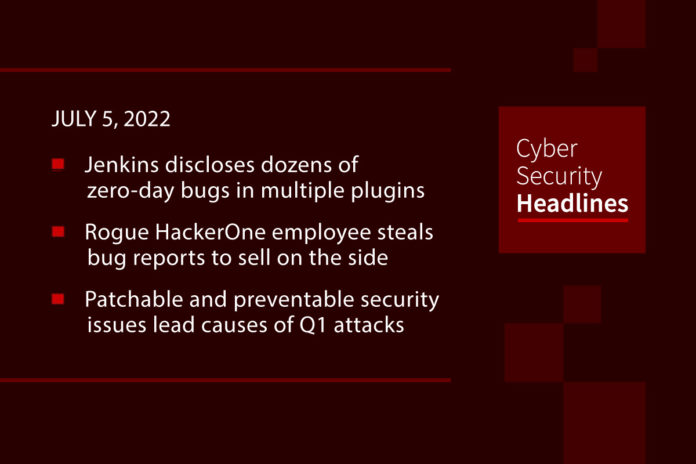
Jenkins discloses dozens of zero-day bugs in multiple plugins
On Thursday, the Jenkins security team announced 34 security vulnerabilities affecting 29 plugins for the Jenkins open source automation server, 29 of the bugs being zero-days still waiting to be patched. The zero-days’ CVSS base scores range from low to high severity, and, according to Jenkins’ stats, the impacted plugins have a total of more than 22,000 installs. The complete list of flaws yet to be patched includes XSS, Stored XSS, Cross-Site Request Forgery (CSRF) bugs, missing or incorrect permission checks, as well as passwords, secrets, API keys, and tokens stored in plain text. Based on Shodan data, there are currently more than 144,000 Internet-exposed Jenkins servers that could be targeted in attacks if running an unpatched plugin.
Rogue HackerOne employee steals bug reports to sell on the side
The rogue worker had contacted about half a dozen HackerOne customers and collected bounties “in a handful of disclosures,” the company said on Friday. On June 22, HackerOne responded to a customer request to investigate a suspicious vulnerability disclosure through an off-platform communication channel from someone using the handle “rzlr.” The customer had noticed that the same security issue had been previously submitted through HackerOne. The rogue employee received bounties for some of the reports they submitted, which allowed HackerOne to follow the money trail and identify the perpetrator as one of its workers who triaged vulnerability disclosures for “numerous customer programs.”
Patchable and preventable security issues lead causes of Q1 attacks
Eighty-two percent of attacks on organizations in Q1 2022 were caused by the external exposure of known vulnerabilities in the victim’s external-facing perimeter or attack surface. Those unpatched bugs overshadowed breach-related financial losses tied to human error, which accounted for 18 percent. The numbers come from Tetra Defense and its quarterly report that sheds light on a notable uptick in cyberattacks against United States organizations between January and March 2022. The report did not let employee security hygiene, or a lack thereof, off the hook. Tetra revealed that a lack of multi-factor authentication (MFA) mechanisms adopted by firms and compromised credential are still major factors in attacks against organizations.
Raspberry Robin Windows worm has already infected hundreds of organizations.
Discovered by cybersecurity researchers from Red Canary, Raspberry Robin is a Windows worm that propagates through removable USB devices. It uses Windows Installer to reach out to QNAP-associated domains and download a malicious DLL. The malware uses TOR exit nodes as a backup C2 infrastructure. The malware was first spotted in September 2021, with Red Canary experts observed it targeting organizations in the technology and manufacturing industries. BleepingComputer reported that Microsoft warned its customers via a private threat intelligence advisory sent to Microsoft Defender for Endpoint subscribers.
Thanks to today’s episode sponsor, Votiro

British Army social media accounts hijacked
The British army’s Twitter and YouTube accounts were compromised by a malicious third party on Sunday and used to direct visitors to cryptocurrency scams. The Ministry of Defence (MoD) press office account took to Twitter at around 7pm local time to report the incident, and four hours later an update claimed the issue had been resolved. The hackers had posted multiple promotional links to various crypto and NFT scams using live stream videos featuring celebrities like Elon Musk and Jack Dorsey, which one prominent lending institution, Santander, says is a fast growing trend in the crypto scam business.
UK signs deal to share police biometric database with US border guards
According to a member of the European Parliament’s Committee on Civil Liberties, Justice and Home Affairs (LIBE), “informally” meetings with representatives of the US Department of Homeland Security were held this week to discuss the plans. They come under the auspices of the Enhanced Border Security Partnership (EBSP), which is designed to increase the US Department Of Homeland Security’s ability to detect threats through biometric information sharing. Israel signed up to the arrangement in March. LIBE committee members said they have already discovered that the UK – and three unidentified EU member states had already signed up to reintroduce US visa requirements which grant access to police biometric databases.
Last week in ransomware
Last week’s big news was the release of LockBit 3.0, which includes a new bug bounty reward program where the threat actors pay between $1,000 to $1 million for submitted bugs and new ways of enhancing their operation. A LockBit affiliate is distributing the ransomware through fake copyright infringement emails, Word docs are used to install AstraLocker directly, and the Black Basta gang is exploiting the PrintNightmare vulnerabilities. There were attacks last week on publishing house Macmillan, Fitzgibbon Hospital in Missouri, Med. University of Innsbruck, and automotive fabric supplier TB Kawashima. Threat actors also claimed to have attacked semiconductor giant AMD, and Walmart, who says the attack never occurred.
FBI adds CryptoQueen to top ten most wanted
Ruja Ignatova, a Bulgarian woman believed to be in her 40s, is wanted for her alleged role in running a cryptocurrency Ponzi scheme known as OneCoin. Federal investigators accuse the fugitive of using the scheme to defraud victims out of more than $4bn. She has been missing since 2017 when US officials signed an arrest warrant and investigators began closing in on her. In 2014, OneCoin, a self-described cryptocurrency, began offering buyers commission if they sold the currency on to more people. But FBI agents say OneCoin was worthless and was never safeguarded by the blockchain technology used by other cryptocurrencies. For those interested in this story, the podcasting arm of the BBC has a 10-part series entitled “The Missing Cryptoqueen.”
(BBC News)