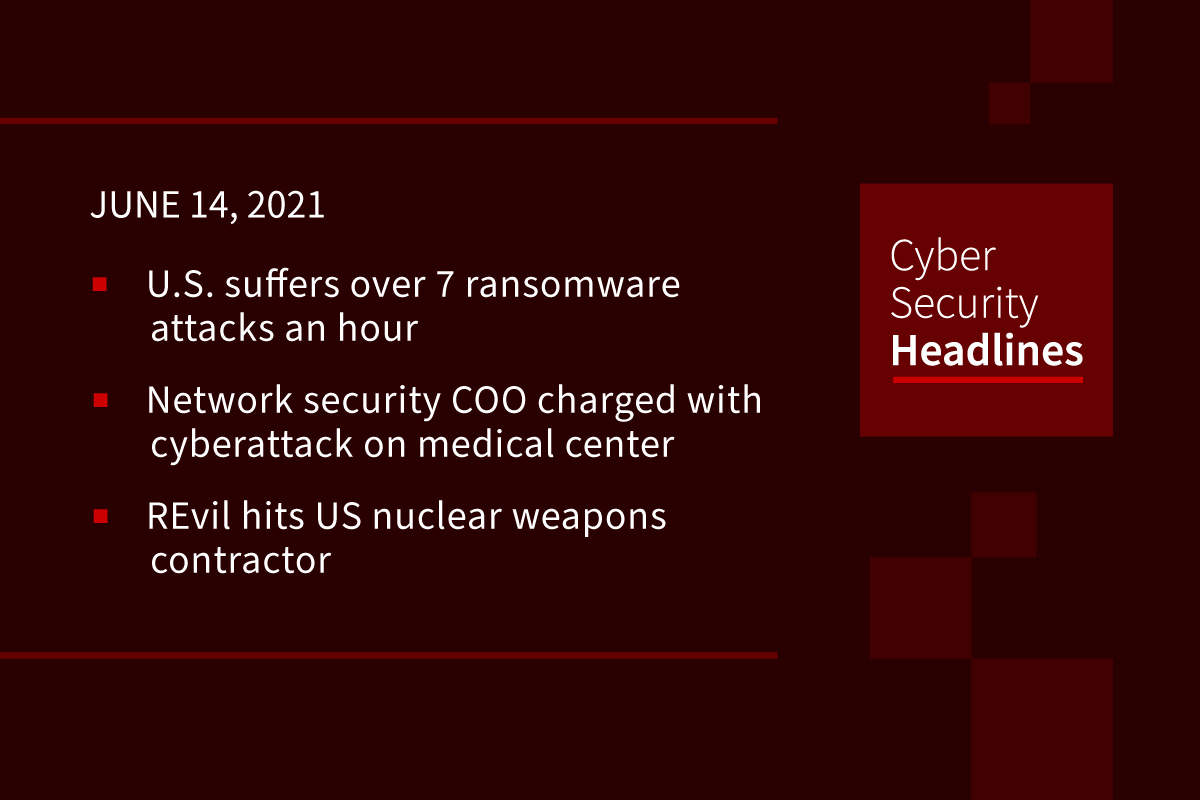
U.S. suffers over 7 ransomware attacks an hour
According to Recorded Future, the US suffered 65,000 ransomware attacks last year, with cybercriminals especially targeting key parts of the country’s infrastructure. Reasons for the increase include companies’ overall neglect of their IT systems, pandemic-related security issues like work from home, the growing popularity and anonymity of cryptocurrencies, and companies’ general willingness to pay out of fear of interruption of their business.
(NPR)
Chief Operating Officer of network security company charged with cyberattack on medical center
Vikas Singla, 45, of Marietta, Georgia, COO of a metro-Atlanta network security company allegedly conducted a cyberattack on Gwinnett Medical Center, allegedly for financial gain. Singla was indicted by a federal grand jury on Tuesday. He is charged with 17 counts of intentional damage to a protected computer, each of which carries a maximum penalty of 10 years’ imprisonment, and one count of obtaining information by computer from a protected computer, which carries a maximum penalty of five years’ imprisonment. The FBI is investigating this case.
REvil hits US nuclear weapons contractor
Sol Oriens, a subcontractor for the U.S. Department of Energy (DOE) that works on nuclear weapons with the National Nuclear Security Administration (NNSA), last month was hit by a cyberattack that experts say came from the relentless REvil gang. For now, the data seems benign, consisting of a company payroll form from September 2020, a company contracts ledger, and a portion of a memo outlining worker training plans. The question remains whether the gang got its hands on more sensitive secret information.
UK government admits ministers can use self-deleting messages
Ministers and civil servants in the UK are allowed to set messages to delete instantly, amplifying concerns about its transparency and accountability. The confirmation comes as concerns grow that self-destructing messages are being used to avoid scrutiny of decision-making processes, including on key issues such as the government’s coronavirus response. Transparency campaigners have expressed alarm at a culture of what they call “government by WhatsApp,” the government’s summary is, “Instant messaging may be used in preference to email for routine communications where there is no need to retain a record of the communication.”
Thanks to our episode sponsor, Keyavi

DoS vulnerabilities in message brokers could leave users locked out of their homes
Synopsys Cybersecurity Research Centre (CyRC) has warned of easily triggered denial-of-service (DoS) vulnerabilities in three popular open-source Internet of Things message brokers: RabbitMQ, EMQ X, and VerneMQ. The message brokers, responsible for handling data sent to or from IoT devices like smart home hubs and door locks, all share a common protocol: Message Queuing Telemetry Transport (MQTT). All three can be fooled into bloating their memory usage until they are terminated by the host operating system by sending them a specially crafted MQTT message. Once terminated, any IoT device on the network which relies on the MQTT message broker will be rendered inoperable.
RockYou2021 means 8.4 billion passwords leaked online
In what seems to be the largest password collection of all time, a hacker forum user posted a massive 100GB TXT file that contains 8.4 billion entries of passwords. Threat actors can use the RockYou2021 collection to mount password dictionary and password spraying attacks against untold numbers of online accounts. Since most people reuse their passwords across multiple apps and websites, the number of accounts affected by credential stuffing and password spraying attacks in the wake of this leak can potentially reach millions, if not billions.
Lax security around URL shortener exposed PII of retailer Carter’s customer base
The US retailer of children’s’ clothing accidentally exposed the personally identifiable information (PII) of potentially hundreds of thousands of customers through a “simple oversight” in the firm’s online order tracking infrastructure caused by a failure to implement authentication protocols for a popular URL shortener tool used on the retailer’s US e-commerce domain used to access a purchase confirmation page. A lack of security around the URLs themselves, together with no authentication to verify the customer led to the potential exposure of over 400,000 customer records.
(ZDNet)
Google won’t kill the URL after all
Since 2018, Google has been on a quest to phase out the URL in the Chrome browser, for security reasons relating to the fact that criminals can easily craft URLs that impersonate legitimate sites. In 2019, the Chrome team detailed ways it wanted to automatically flag sketchy URLs. And in June of last year, the browser took the significant user-facing step of hiding parts of a URL in the address bar. A year later, the company has decided to move on. Chrome security engineer Emily Stark wrote on Monday, “this experiment didn’t move relevant security metrics, so we’re not going to launch it.”
(Wired)