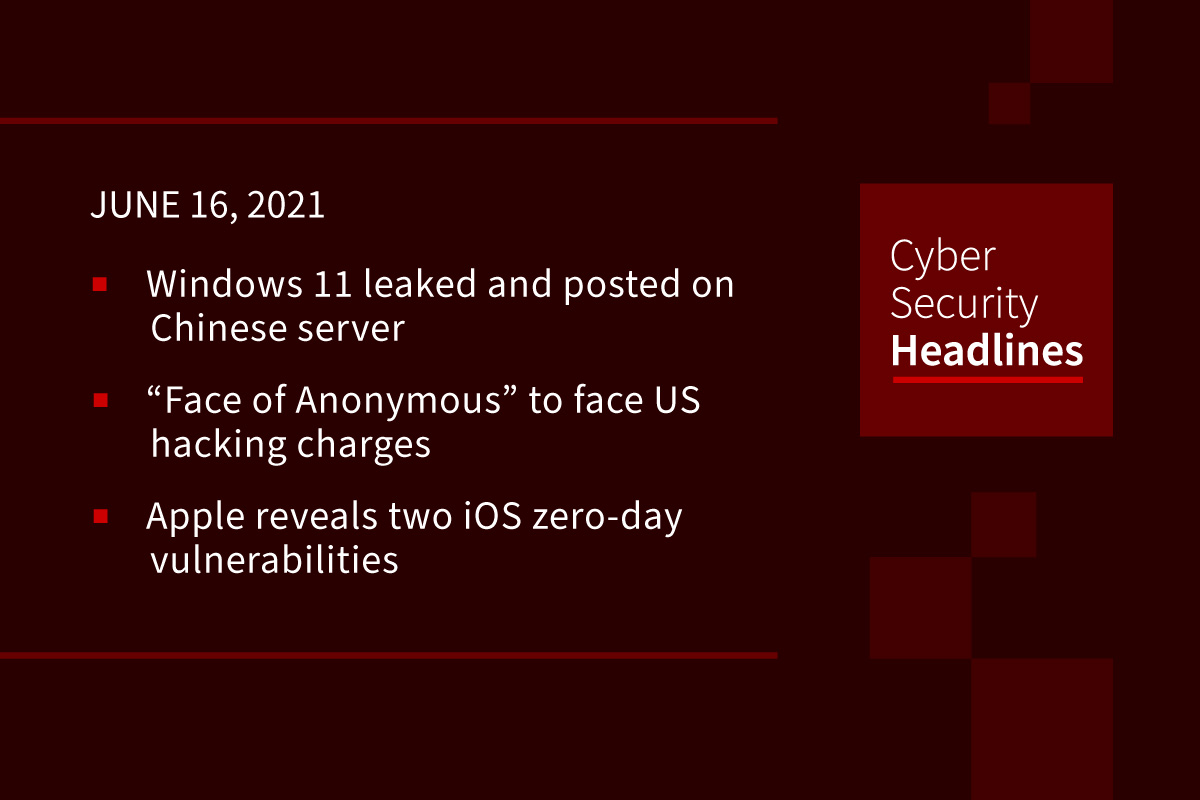
Windows 11 leaked
Windows 11 ISO image was leaked yesterday on a Chinese-speaking forum and has quickly spread throughout the Internet as users rush to install the new leaked operating system. Links for the Windows 11 ISO are now emerging on various file sharing sites, making it difficult to contain the leak. If the leaked material is legitimate, first reviews mention more rounded corners and a Start menu that hovers in the middle of the desktop. Bleeping Computer points out that the leaked build may have been tampered with to include malicious programs or viruses and that care should be taken to install and play with it on a virtual machine or other secured device.
“Face of Anonymous” suspect deported from Mexico to face US hacking charges
Media in the San Francisco area are reporting the arrest of Christopher Doyon, 56, who allegedly skipped bail on hacking charges almost a decade ago and was known in the media on TV and through his own book, as the face of the hacking group Anonymous. After living in Toronto for some years, Doyon apparently moved to Mexico. Anonymous is known for high-profile hacks such as the takedown of PayPal in 2010 after it suspended donations to Julian Assange and Wikileaks; government website takedowns during the so-called “Arab Spring” of 2011, and much more.
Apple reveals two iOS zero-day vulnerabilities that allow attackers to access fully patched devices
Apple has released a new patch for vulnerabilities that are located in the browser engine Webkit, which provides web content for App Store, Mail and Safari as well as other various apps running on iOS, Linux and macOS. Apple described this attack as the processing of maliciously crafted web content resulting in arbitrary code execution. The patch, iOS 12.5.4, is available for download.
Instagram bug allowed anyone to view private accounts without following them
Instagram has now patched the bug, which was discovered by security researcher Mayur Fartade and reported to Instagram owner FaceBook on April 16. The bug allowed non followers to see details of private and archived posts, stories, reels, and IGTV without following the user, but by using Media ID, with some brute forcing involved . He was also awarded $30,000 as part of the company’s bug bounty program.
Thanks to our episode sponsor, Keyavi
Paradise ransomware source code released on hacking forum
Released on the hacking forum XSS, the code allows any would-be cybercriminal to develop their own customized ransomware operation to include a custom command and control server, encrypted file extension, and contact email address. Sprinkled throughout the source code are Russian comments, that purportedly demonstrate the native language of the developer. Once the customized ransomware is created, affiliates can distribute the malware in their campaigns to target victims.
Critical remote code execution flaw in thousands of VMware vCenter servers remains unpatched
Researchers have warned that thousands of internet-facing VMware vCenter servers still harbor critical vulnerabilities weeks after patches were released. The vulnerabilities impact VMware vCenter Server, a centralized management utility. As we reported last week, VMware issued patches for two critical bugs, CVE-2021-21985 and CVE-2021-21986, on May 25. VMware said in a security advisory that this severe bug can be exploited so threat actors can access “the underlying operating system that hosts vCenter Server” with “unrestricted privileges.” It appears that thousands of internet-facing servers are still exposed and vulnerable to both of the vulnerabilities.
(ZDNet)
Mystery malware steals 26 million passwords and much more from Windows PCs
Researchers have discovered yet another massive trove of sensitive data, a 1.2 TB database containing login credentials, browser cookies, autofill data, and payment information extracted by malware that has yet to be identified. Researchers from NordLocker said on Wednesday, the database contained 26 million login credentials, 1.1 million unique email addresses, more than 2 billion browser cookies, and 6.6 million files. In some cases, victims stored passwords in text files created with the Notepad application. The stash also included over 1 million images and more than 650,000 Word and PDF files. Additionally, the malware made a screenshot after it infected the computer and took a picture using the device’s webcam. The data was extracted between 2018 and 2020 from more than 3 million PCs. NordLocker hasn’t been able to identify the malware used in this case.
(Wired)
Texas Attorney General charged in 32-bit eco-friendly server scam
The US Securities and Exchange Commission (SEC) has charged the CEO of Texas server manufacturer Servergy, one of its board members, and the state’s Attorney General with fraud over claims of revolutionary low-powered computer hardware. The SEC alleges that between 2009 and 2013 Servergy’s then-CEO William Mapp misled investors about the capabilities of the firm’s Cleantech CTS-1000, saying it could deliver 80 per cent power savings against servers from IBM, HP and others, which allegedly came from improper comparisons. Mapp is also accused of misrepresenting sales, having millions of dollars worth of orders from a variety of companies, including Amazon.