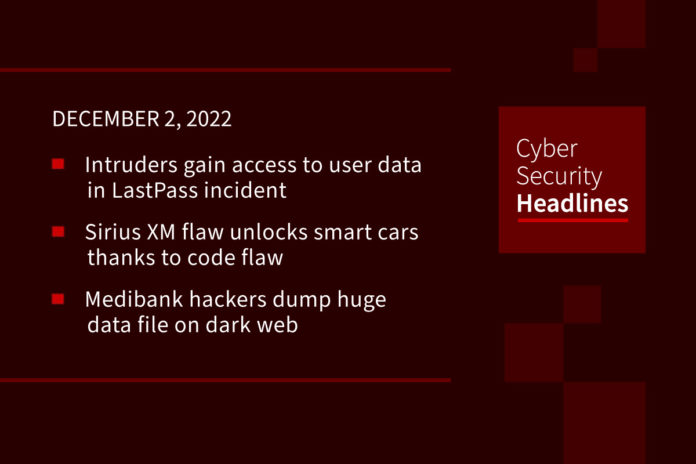
Intruders gain access to user data in LastPass incident
Following up on a story we brought you in August, intruders broke into a third-party cloud storage service that LastPass shares with affiliate company GoTo and gained access to “certain elements” of customers’ information, the companies have confirmed. LastPass did not define what it meant by “certain elements,” saying it was unsure what data was looked at. The statement confirmed that the attackers obtained the information to carry out the current intrusion using information stolen in an August attack. It did maintain, however, that services were unaffected and that customers’ passwords remained “safely encrypted” – without ruling out that some of the data was stolen.
Sirius XM unlocks smart cars thanks to code flaw
Sirius XM’s Connected Vehicle Services has fixed an authorization flaw that would have allowed an attacker to remotely unlock doors and start engines on connected cars knowing only the vehicle identification number (VIN). Yuga Labs’ Sam Curry detailed the exploit in a series of tweets and confirmed that the patch issued by SiriusXM has since fixed the security issue. Security researchers at Yuga Labs found the issues and explored attack surfaces in the SiriusXM “smart vehicle” platform used in models made by Hyundai, Toyota, Honda, Fiat Chrysler, Nissan, Acura, and Infinity that allowed them to “remotely unlock, start, locate, flash, and honk” them.
(The Register and Bleeping Computer)
Medibank hackers announce ‘case closed’ and dump huge data file on dark web
Following up on the ongoing story of the Medibank breach in Australia, the group behind the cyber-attack has posted on the dark web what appears to be the remainder of the customer data they took from the health insurer, stating it is “case closed” for the hack. On Thursday morning, the blog – which returned online after several days of being offline, posted “Happy Cyber Security Day!!! Added folder full. Case closed,” and included a file that has several compressed files amounting to over 5GB. Medibank said it is in the process of analyzing the data but it “appears to be the data we believed the criminals stole.”
Data reveals California as the most security conscious state
Internet privacy and digital security company TechShielder has revealed the most security-conscious states in the US by comparing the number of Google searches in each state for the following eight terms: VPN, Private Browsing, Incognito Mode, Delete Cookies, Change Password, Private Search, Erase History, and Clear Cache. Factoring in the differences in populations between states, the report ranked them in terms of searches per 100 thousand people. California ranked highest with 301 searches per 100,000, followed by Nevada, Oregon, New Jersey, New York and Texas with rankings between 291 and 278 per 100,000.
Thanks to this week’s episode sponsor, Automox

LinkedIn rolls out focused inbox and messaging tools to deal with spam and scams
The business network platform is currently experiencing a year-over-year growth rate of 34% and claims to now have 875 million members. Yesterday it announced changes to its direct messaging service that speak to the issue of spam and scams. It states it is now rolling out a “focused” option for incoming messages with others relegated to an “other” box; and it’s turning on new automatic spam and harassment detection tools, and a new feature to report unwanted messaging. The system will use AI to learn and refine its processes for identifying and eliminating unwanted messages.
Ransomware group may have stolen customer bank details from British water company
In yet another follow-up story, South Staffordshire Water, which supplies water for more than 1.7 million people in England, has said that an attempted ransomware attack in August may have enabled cybercriminals to steal customer bank details. At the time of the incident the company stressed that the water supply was not affected, although its corporate network was experiencing disruptions. The company said in an update on Wednesday that customers who paid by direct debit may have had their bank details stolen. Water suppliers are required to report cybersecurity incidents to The Water Services Regulation Authority (Ofwat) under the U.K.’s Network and Information Systems (NIS) Regulations. However, the reporting obligation only applies to incidents which ultimately impact water supply, which the ransomware attack did not. The government announced yesterday it would update the legislation so that service providers would need to notify regulators “of a wider range of incidents.”
UK introducing mandatory cyber incident reporting for managed service providers
The British government is introducing a new mandatory reporting obligation on managed service providers (MSPs) to disclose cyber incidents, alongside minimum security requirements which could see MSPs fined up to £17 million ($20 million) for non-compliance. The government said on Wednesday that MSPs “play a central role in supporting the UK economy” and warned they are “an attractive and high value target for malicious threat actors, and can be used as staging points through which threat actors can compromise the clients of those managed services.” Financially-motivated ransomware attacks have impacted MSPs such as Kaseya in the United States and the NHS supplier Advanced in Britain, with the latter severely impacting patient care according to BBC News.
San Francisco to allow police ‘killer robots’
San Francisco’s ruling Board of Supervisors has voted to let the city’s police use robots that can kill. The measure permits police to deploy robots equipped with explosives in extreme circumstances. The San Francisco police force have told the BBC they do not currently operate any robots equipped with lethal force, although they say there may be future scenarios in which lethal force could be used, such as using explosive charges to breach fortified structures containing violent, armed, or dangerous subjects.” It should be noted that this type of lethal robot is already in use in other parts of the United States. In 2016, police in Dallas, used a robot armed with C-4 explosive to kill a sniper who had killed two officers and injured several more.
(BBC News)