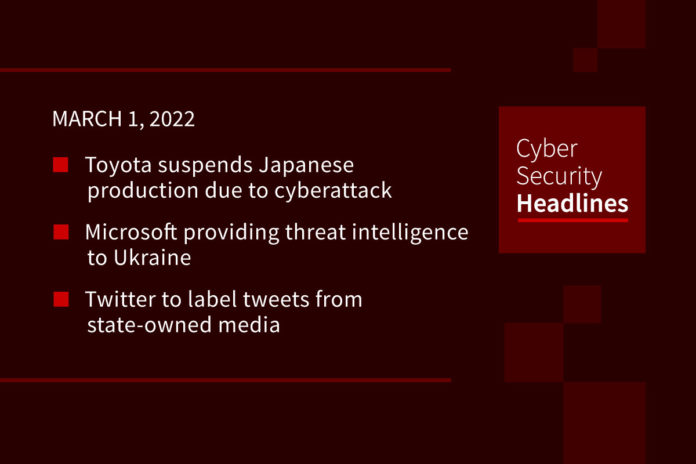
Toyota suspends Japanese production due to cyberattack
Toyota suspended all of its 14 factories in Japan due to what a spokesperson called a “supplier system failure” with Kojima Industries. Kojima said it appeared to be the victim of a cyberattack. This will result in the company losing about 13,000 cars of output per day, about a third of its global production. It’s unclear if the shutdown will last more than a day, Toyota only said it would shut down production for March 1st. No word on who was behind the attack. Japanese Prime Minister Fumio Kishida said the government is investigating the attack, saying “It is difficult to say whether this has anything to do with Russia before making thorough checks.”
(Reuters)
Microsoft providing threat intelligence to Ukraine
In a blog post, Microsoft President Brad Smith said the company has provided direct “threat intelligence and defensive suggestions” to Ukrainian government agencies. Smith did not attribute attacks to specific actors, saying this action was part of Microsoft’s primary responsibility to “help defend governments and countries from cyberattacks.” As part of this information exchange, Microsoft informed the Ukrainian government of a new malware hitting the country on February 24th, ahead of initial Russia missile strikes. Smith further noted recent cyberattacks against the country are narrowly targeted, in contrast to the broad NotPetya ransomware attack in 2017.
(CNBC)
Twitter to label tweets from state-owned media
Twitter will add new labels to tweets with links from Russian state-linked media outlets, stating their affiliation and adding an orange exclamation point. The reach of these posts will also be algorithmically limited. Twitter began labeling state-controlled account profiles in 2020, but not individual tweets. The platform will add similar labels to other “state-affiliated media accounts” over the next few weeks. Twitter Head of Site Integrity Yoel Roth said these labels are meant to “add helpful context” to conversations on the platform.
Conti ransomware gang member breaks rank over Ukraine
The operators of the Conti ransomware recently published a pro-Russian message on its official site, following the Russian invasion of Ukraine. However one Conti member, believed to be of Ukrainian origin, hacked into the group’s Jabber/XMPP server and leaked internal logs to journalists and security researchers. This includes conversations for the group from January 29, 2021 through February 27th 2022. The chats show Conti’s relationships with TrickBot and Emotet gangs, ransom negotiation and payment details, and Bitcoin addresses where the group received payments.
There are many misconceptions about security automation, so Torq is debunking a security automation myth each day this week.

Wrong. While scanning and testing may be one example of a security automation use case, it’s hardly the only one. Automation can be used to do things like help manage complex security workflows and optimize collaboration between different stakeholders. These are tasks that were not traditionally automated. To learn more about the realities of automation, head to torq.io.
Facebook and Twitter removed covert influence operations
The two social networks removed two anti-Ukranian influence operations over the weekend. One campaign showed ties to Russia, run as a propaganda campaign linking to an anti-Ukraine website, seemingly an offshoot of an existing disinformation campaign. This used AI generated faces to create fake “correspondants ” to add credibility to their content. The other campaign showed ties to Belarus. According to Meta’s head of security policy Nathaniel Gleicher, these tactics largely mirror Russian disinformation operations used around the 2016 election, but noted that neither seemed to be particularly effective.
(NBC News)
Nvidia hacks the hackers
Yesterday we covered a cyberattack against Nvidia by the group LAPSU$ that allegedly obtained over 1TB of data from the GPU giant. At the time, Nvidia said it was investigating the incident… and by investigating the incident, they meant turning the tables of the attackers. According to a several sources, Nvidia performed a “hack back,” taking over and ransoming the groups machines, at least encrypting their hard drives. The groups claims they were able to generate backups contained the breached Nvidia data. This apparently was possible because the attackers had to enroll in Nvidia’s MDM to access its VPN, providing a connection to let Nvidia access a virtual machine used by LAPSU$.
CISA warns of WhisperGate
The Cybersecurity and Infrastructure Security Agency and FBI released a new joint advisory with guidance on WhisperGate and HermeticWiper for US organizations. These have both been seen used against organizations in Ukraine, although the advisory said there are no known specific threats using it against the US. CISA Director Jen Easterly said CISA has been working with partners to identify new malware used in the conflict that could threaten critical infrastructure in the US.
(ZDNet)
Windows reset leaves user data on PCs
Microsoft disclosed a bug in the latest versions of Windows 10 and 11 that results in all users data not being wiped when performing a system reset. This impacts a portion of locally stored OneDrive data, which is left unencrypted even if using disk encryption prior to the reset. Microsoft said this particularly impacts “”apps which have folders with reparse data” synced locally. Microsoft suggests signing out of OneDrive or deleting the Windows old folder before resetting a PC.