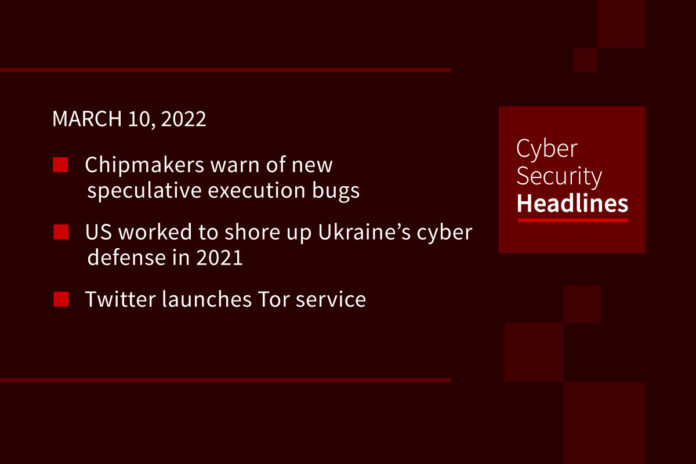
Chipmakers warn of new speculative execution bugs
AMD, Arm, and Intel each published advisories about newly discovered ways to bypass hardware-based protections for speculative execution in modern CPUs. Back in 2018, Meltdown and Sepctre vulnerabilities led to a rash of security concerns around speculative execution, resulting in software-based partial mitigations and hardware changes on CPUs. Researchers at VUSec published a report detailing all existing hardware and software mitigations around speculative execution using what they refer to as Branch History Injection. This allows low privilege users to poison the global history used as a hardware mitigation for speculative execution attack to mispredict targets and subsequently leak data, The researchers demonstrated how this could be used to obtain a root hash password in a proof of concept attack. All three chip makers released mitigation recommendations with their security advisories.
US worked to shore up Ukraine’s cyber defense in 2021
Ars Technica shares a report that US personnel, including soldiers with the US Army’s Cyber Command, began focusing on shoring up Ukraine’s cyber defenses in preparation for war with Russia in October and November. While the US has been helping Ukraine with cyber defenses since the 2015 attack on its power grid, but these two months were targeted specifically to prepare for the conflict. This includes removing malware found in Ukranian Railways. These teams also laid the groundwork with private companies to help alleviate attacks, including Fortinet which helped counter DDoS attack, and Microsoft.
Twitter Tor service launches
Twitter has been tough to access in Russia, with the government blocking access earlier this month and most VPNs compelled to also block the site. In response, security researcher Alec Muffett announced a new Tor Project onion service for Twitter. This will allow users in Russia to access the service through the Tor browser even when blocked by their ISP. ISPs can still block access to the overall Tor network, although users can often connect through use of a Tor bridge relay. Facebook, which is also blocked in Russia, launched its own Tor version back in 2014.
(Vice)
More internet stalwarts pull out of Russia
We previously covered that the internet backbone company Cogent Communications pulled out of Russia. Now another backbone provider, Lumen is joining them, leaving the remaining international data options for Russia only from Western companies based in Sweden, Italy and the United Kingdom. In addition Amazon Web Services implemented a policy change over the weekend, preventing customers in Russia and Belarus from signing up for new accounts. AWS does not operate any data centers in Russia, and says most of its existing customers in the country are multinationals with local development teams.
There are many misconceptions about security automation, so Torq is debunking a security automation myth each day this week.

Not true. Any business that attempts to automate security will quickly find that most high-stakes security issues are far too complex to be detected and remediated by automation tools alone. Human security professionals need to take the lead delivering nuanced insight about the business impact of a large-scale breach. To learn more about the realities of automation, head to torq.io.
Anonymous strikes Russia
The group Anonymous and several other hacker collectives targeted Russia IP cameras, publishing over 400 feeds to the website behindenemylines.live. This organizes the feeds into various categories and locations, including Business, Outdoor, Restaurants, and Schools. These feeds are overlaid with messages criticizing Russia’s invasion of Ukraine. The group also resented hacking into a TV channel streaming service in Russia to broadcast war footage, and continues to targets websites in Belarus. An Anonymous affiliate group also claimed to have obtained source code from the security firm Kaspersky, although as of this recording no code has been leaked.
The EU goes after Russian crypto
The European Union clarified its previously imposed financial sanctions on Russia and Belarus extend to crypto, as assets are covered by the “transferable securities” category. The EU also announced the expansion of financial restrictions on Belarus to mirror Russia’s, including restrictions on SWIFT to three Belarusian banks. There has been some speculation by US lawmakers that Russia could use cryptocurrency transactions to avoid some of the impact of international sanctions.
(CoinDesk)
Hackers fork open source tools
A new report from Security Joes shows that threat actors targeting the gambling industry used a forked version of the open source reverse tunneling utility Ligolo called Sockbot. This modified version removed the need to use command-line parameters and included checks to help avoid running it in multiple instances. The only other group to use a modified version of Ligolo is the Iranian state-sponsored hacking group MuddyWater. Security Joes said Ligolo generally required significant and advanced modification to make it useful as a hacking tool, indicating advanced capabilities of the attackers forking it. The overall tactics of the attack show them tightly related to a Russian-speaking ransomware gang.
Uninterrupted power supply interrupted by zero-days
The security firm Armis published details on three zero-day vulnerabilities in Schneider Electric’s APC Smart-UPS products that could open up the devices to be used for network infiltration. These vulnerabilities were dubbed TLStorm, and lie in vulnerabilities in how the devices connect to the SmartConnect cloud feature connect over TLS. These vulnerabilities require no human interaction, and could let an attacker hijack a TLS connection to push unauthorized firmware or remote code execution. Schneider said its working on remediations and mitigations, and Armis said there is no indication these vulnerabilities are being actively exploited.