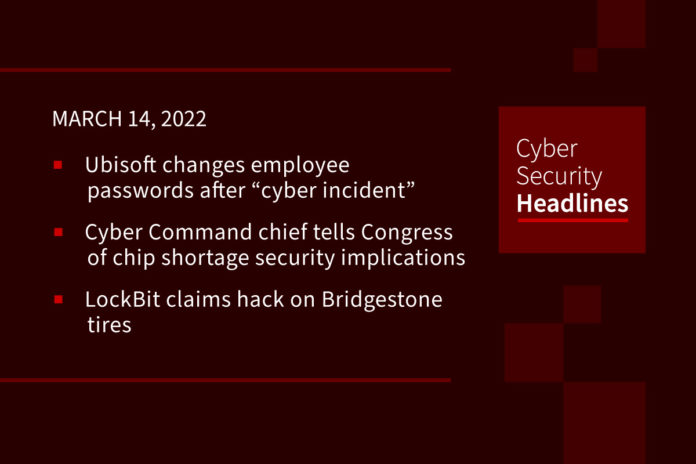
Ubisoft changes employee passwords after “cyber security incident”
In a brief statement published on its website, maker of hit titles like Assassin’s Creed and Just Dance, said that out of caution it had “initiated a company-wide password reset” but that games and services were acting normally and there was “no evidence” any players’ personal information had been exposed. Details are still scant, but a report from The Verge states that LAPSUS$ hacking group – which has recently claimed responsibility for attacks on NVIDIA and Samsung might be taking credit for this incident as well.
Cyber Command chief tells Congress chip shortage has national security implications
China’s increasing progress toward producing enough semiconductor chips domestically to avoid relying on foreign trade is an issue of great concern for us in terms of broader impacts, U.S. Cyber Command and National Security Agency head Gen. Paul Nakasone told House Intelligence Committee members this week. He added, China’s progress toward chip independence would give the Chinese more leverage to act as they please without fear of sanctions. He added the United States is lagging in domestic semiconductor chip production, and noted that Ukraine and Russia produce 90% of America’s neon gas, which is critical for the lasers used to make chips.
LockBit claims hack on Bridgestone tires
On February 27, Bridgestone Americas, one of the America’s largest manufacturers of tires, sent home some company employees of the La Vergne plant, just outside of Nashville, TN, due to a possible cyber-attack. Bridgestone launched an investigation into the incident and hired a prominent consultant firm to understand the full scope and nature of the incident. A statement read, in part, “out of an abundance of caution, we disconnected many of our manufacturing and retreading facilities in Latin America and North America from our network to contain and prevent any potential impact.” LockBit operators apparently plan to release stolen materials March 15, if the company does not pay the ransom.
Android malware Escobar steals Google Authenticator MFA codes
The Aberebot Android banking trojan has returned under the name ‘Escobar’ with new features, including stealing Google Authenticator multi-factor authentication codes. New features include taking control of the infected Android devices, recording audio, and taking photos, while also expanding the set of targeted apps for credential theft. Its main goal is to steal information for takeover of bank accounts, including siphoning of available balances, and performing unauthorized transactions. Users can minimize the chances of being infected with Android trojans by avoiding the installation of APKs outside of Google Play, using a mobile security tool, and ensuring that Google Play Protect is enabled.
Thanks to our episode sponsor, Varonis
Dell opts out of Microsoft’s Pluton security for Windows
Dell will not include Microsoft’s Pluton technology in most of its commercial PCs, telling The Register: “Pluton does not align with Dell’s approach to hardware security and our most secure commercial PC requirements.” Microsoft launched its Pluton security layer for PCs with much fanfare in 2020 after developing it with Intel, AMD, and Qualcomm. Pluton effectively bakes a co-processor in silicon that securely stores encryption keys, credentials, and other sensitive information. The idea being that this data is kept close to the CPU cores, within the same processor package, thwarting attempts to extract secret information. Intel, for one, has not implemented Pluton in any 12th-Gen Intel Core processors, code-named Alder Lake, opting for its own TPM support. Dell laptops shipped with 12th-Gen Intel Core processors will therefore not use Pluton for their TPMs.
Zero-click flaws in widely used UPS devices threaten critical infrastructure
Three critical security vulnerabilities in widely used smart uninterruptible power supply (UPS) devices could allow for remote takeover, meaning that malicious actors could cause business disruptions, data loss and even physical harm to critical infrastructure, researchers at Armis have found. The flaws, which Armis has dubbed TLStorm, are in APC Smart-UPS devices, which number about 20 million in deployment worldwide. APC is a subsidiary of Schneider Electric. Being controlled through a cloud connection means a bad actor could remotely take over devices without the user ever knowing about it,” the researchers warned. Furthermore, an attacker could gain code execution on a device, forcing it to physically damage itself or other assets connected to it, they said.
New Chinese exascale supercomputer runs ‘brain-scale AI’
Back in October, reports surfaced that China had achieved exascale-level supercomputing capabilities on two separate machines, built with entirely Chinese components, from CPU to network. A paper published Friday, now outlines its capabilities that involves a pre-trained AI language model with 14.5 trillion parameters with mixed precision performance of over one exaflop. The paper’s authors say, “This is an unprecedented demonstration of algorithm and system co-design on the convergence of AI and High Performance Computing.” An exaFLOP, by the way is one quintillion (1018) floating-point operations per second. To match what a one exaFLOP computer system can do in just one second, you’d have to perform one calculation every second for over 31 billion years.
(The Register and Network World)
Mary Coombs, first female commercial programmer, dies at 93
Passing away on February 28, Mary will be remembered for her pioneering work in programming a computer for commercial applications. She was central to the development of the Lyons Electronic Office – LEO – for British food chain Lyons in the 1950s, winning out over a number of other applicants – all male – to become one of a two-person team charged with its development. In a time at which computers involved valves and mercury delay tubes, she wrote subroutines for repetitive subtraction and division of numbers. The LEO I computer occupied an entire room, ran at 500 kHz and had just 2,000 35-bit words of memory. One of her notable triumphs that she recounted was in debugging the LEO 1, and finding the source of its problem to be electrical interference caused by operations of the company elevator located next to the LEO room.