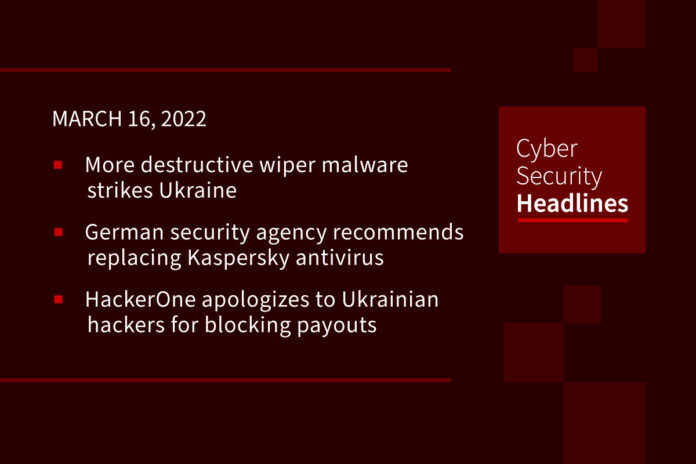
More destructive wiper malware strikes Ukraine
On March 14, researchers at ESET announced on Twitter that they’ve discovered new malware, dubbed CaddyWiper, the third wiper discovered by the firm in as many weeks being used to attack Ukraine. ESET noted that CaddyWiper, which so far has only been observed on a few dozen systems in a limited number of organizations, does not share any “significant” code similarities with HermeticWiper or IsaacWiper. While CaddyWiper erases user data and partition information, ESET notes that it avoids wiping information on Windows domain controllers.
(ZDNet)
German security agency recommends replacing Kaspersky antivirus
The German Federal Office for Information Security agency, aka BSI, recommends consumers uninstall Kaspersky anti-virus software warning of elevated risks in light of the ongoing Russian invasion of Ukraine. Specifically, BSI warns that Kasperky anti-virus software or its IT infrastructure could knowingly or unknowingly be exploited as part of offensive cyber operations. The alert pointed out that antivirus software operates with high privileges on machines and if compromised could allow an attacker to take them over. BSI has recommended, “replacing applications from Kaspersky’s virus protection software portfolio with alternative products.”
HackerOne apologizes to Ukrainian hackers for blocking payouts
On Tuesday, Chris Evans, the CISO of bug bounty platform HackerOne, apologized to Ukrainian hackers after erroneously blocking their bug bounty payouts following sanctions imposed on Russia and Belarus after Ukraine’s invasion. The company confused matters by stating in a now-deleted tweet that the company would re-route all rewards earned by hackers in sanctioned areas to UNICEF. HackerOne has since restored access to Ukrainian accounts and is working to fix payment issues while clarifying that rewards would only be donated upon explicit instruction from the hacker. Evans added that HackerOne will publish a frequently asked questions (FAQ) page within 24 hours to share more information about what happened.
FTC to fine CafePress for cover up of massive data breach
The U.S. Federal Trade Commission (FTC) announced plans to slap CafePress custom t-shirt and merchandise site, with a $500,000 fine for a breach that affected over 23 million of its users. Instead of responsibly informing customers about the breach, CafePress instead closed the users’ accounts and charged them each a $25 account closure fee. The FTC explained that CafePress stored customer Social Security numbers and password reset answers in plain text, and retained user data for longer than necessary. As part of the proposed settlement, CafePress will be required to implement multi-factor authentication, minimize data collection and retention, and encrypt Social Security numbers stored on its servers.
Thanks to our episode sponsor, Varonis
FBI warns of MFA flaw used by state hackers
The FBI says Russian state-backed hackers gained access to a non-governmental organization (NGO) cloud by exploiting a misconfigured setting within the organization’s Duo multi factor authentication (MFA) platform. The hackers used credentials obtained in a brute-force password attack to access an inactive but not yet disabled Active Directory account. From there the attackers used RDP to connect to Windows domain controllers and then moved laterally to gain access to the cloud storage and email accounts to exfiltrate data. On Tuesday, the FBI and CISA jointly advised orgs to enforce MFA, ensuring to protect against “fail open” and re-enrollment scenarios, to disable inactive AD and MFA accounts and prioritize patching of known exploited vulnerabilities.
Israeli Government sites taken off line in large-scale cyberattack
Israeli government websites were taken offline Monday in what is being described as the largest ever Distributed Denial of Service (DDoS) attack to be launched against the country. The cyberattack took down the websites of Israel’s Prime Minister’s Office and its interior, health, justice and welfare ministries, while a local newspaper implicated Iran as the responsible threat actor amidst ongoing tensions between the two countries. All affected websites appear to now be operational, however, the Israeli government has declared a state of emergency to study the extent of the damage caused by the attack.
New Linux botnet exploits Log4j
A newly discovered malware botnet, which researchers have dubbed B1txor20, leverages vulnerable Apache Log4j libraries to exploit Linux ARM, X64 CPU architecture devices. Researchers at Qihoo 360 NetLab used a honeypot to capture multiple malware samples which they found to be capable of creating backdoors and rootkits, serving as a SOCKS5 proxy, downloading other malware, stealing data, and executing arbitrary commands. What makes the B1txor20 malware stand out is the use of DNS tunneling for communicating with its command-and-control (C2) server, an old but reliable technique used by threat actors to tunnel malware and data via DNS queries.
Report uncovers alarming level of alert fatigue in Cloud environments
Orca Security commissioned a global, cross-industry study among IT decision makers to examine the current state of cloud security alert fatigue. The report revealed that security teams are inundated with cloud security alerts with 59% of respondents receiving more than 500 cloud security alerts per day. The survey showed that monitoring alerts is causing burnout with roughly 60% respondents indicating that alert fatigue has contributed to staff turnover and also has created internal friction. The report also shows a false sense of confidence with more than 95% responding that they feel confident or very confident in their tooling, despite 43% of respondents indicating that more than 40% of their alerts are false positives, roughly half saying more than 40% of alerts are low priority, and more than half of respondents indicated that critical alerts are being missed.