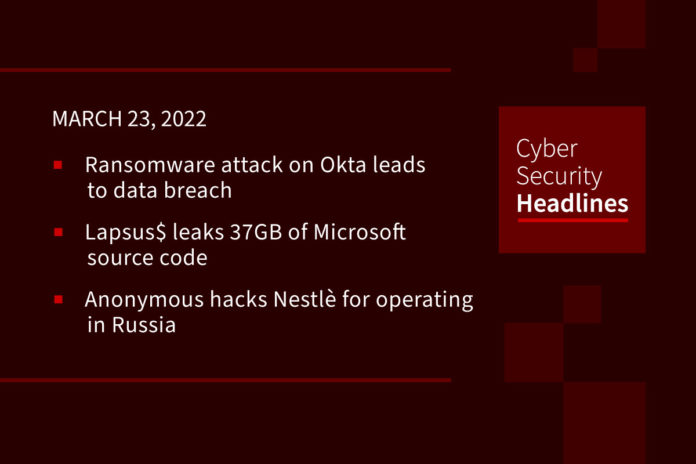
Ransomware attack on Okta leads to data breach
Lapsus$ group claims to have hacked the network of cloud-based security software provider, Okta. Lapsus$ posted screenshots on Telegram confirming that it successfully stole sensitive data and was able to gain super-user access to Okta’s entire corporate network. The media is speculating that the data breach could have put all of Okta’s roughly 15,000 customers at extreme risk, affecting companies such as Peloton, Cloudflare, Grubhub, T-Mobile, FCC, and Sonos. A spokesperson from Okta noted that, so far, there is no firm evidence to substantiate the media’s speculation.
Lapsus$ leaks 37GB of Microsoft source code
Lapsus$ appears to be staying busy, posting a 7zip archive on Monday night, containing 37 GB of source code for over 250 projects, including Bing and Cortana, that appears to have been stolen from Microsoft’s internal Azure server. The stolen source appears to be related to Microsoft web-based infrastructure, websites, and mobile apps with no detected impact to Windows, Windows Server, or Microsoft Office. In recent months, Lapsus$ has disclosed numerous cyberattacks against large companies, including NVIDIA, Samsung, Vodafone, Ubisoft, Mercado Libre and, or course, Okta.
Anonymous hacks Nestlè for operating in Russia
Hacktivist group Anonymous announced Tuesday that they’ve stolen 10 GB of sensitive data from Nestlè, including company emails, passwords, and customer data for continuing to operate in Russia after its invasion of Ukraine. So far Anonymous has only leaked a sample of data of roughly 50,000 Nestlé customers. Ukrainian Prime Minister Denys Shmyhal said of Nestlé’s choice to remain in the Russian market, “Paying taxes to the budget of a terrorist country means killing defenseless children and mothers. I hope Nestle changes its mind soon.” Anonymous has threatened 40 more international companies, warning that they have 48 hours to cease Russian operations.
Top Russian meat producer hit with BitLocker encryption attack
Moscow-based meat producer and distributor Miratorg Agribusiness Holding has suffered a major cyberattack that encrypted its IT systems, according to a report from Rosselkhoznadzor, the Russian federal supervision service. The announcement indicates that the attackers used a ransomware attack, leveraging Windows BitLocker to encrypt files. The motive for the attack appears to be sabotage and not financial in nature. Miratorg has stated that they are working towards restoring business operations and has indicated that it does not anticipate any impact to supply and shipments to Russian citizens.
Thanks to our episode sponsor, Varonis
Russia laying groundwork for cyberattacks on US infrastructure
On Monday, the White House warned that the latest intelligence indicates that the Russian government is exploring “options for potential cyberattacks” on critical US infrastructure, in retaliation for sanctions resulting from Russia’s invasion of Ukraine. The White House has contacted companies that could be impacted and has also released a fact sheet for organizations to use to harden their cyber-defenses, including employee awareness and education, implementing multi-factor authentication (MFA), staying current with patching, backing up and encrypting data, performing red-team exercises, and updating security tools.
Background check company sued over data breach
Back in February, international background check services company, Creative Services, Inc. (CSI) confirmed that personal data belonging to more than 164,000 clients had been compromised in a breach they detected back in November. Breached data included names, dates of birth, financial account numbers, Social Security numbers and driver’s license numbers. CSI began issuing breach notices last month, offering 24 months of free credit monitoring to affected individuals. CSI’s latest breach discovery came two months after it had notified one thousand individuals that their personal information had been compromised in a separate incident. Four parallel lawsuits have been filed by plaintiffs alleging that CSI failed to effectively protect the information of people whose backgrounds it was hired to check.
Hundreds of HP printer models vulnerable to remote code execution
Security advisories have been published for four security vulnerabilities affecting HP’s LaserJet Pro, Pagewide Pro, OfficeJet, Enterprise, Large Format, and DeskJet printer models. The first issue, disclosed in an advisory from Trend Micro, is a critical severity buffer overflow flaw that could lead to remote code execution on affected printers. A second bulletin from HP warns about two critical and one high-severity bug that could be exploited for information disclosure, remote code execution, and denial of service. HP has released firmware security updates for most affected products and has provided mitigation instructions for printers still pending security updates.
Someone hacked the Spelling Bee
Proving that nothing is sacred, back in January, hackers targeted the website for the National Spelling Bee and stole personal information from site users. According to a data breach filing by Scripps, the company who organizes the notorious contest, the hackers were able to steal login credentials and more than 54,000 email addresses from the site which is used as a resource portal for contestants’ parents, sponsors, and teachers. Scripps quickly patched its website after discovering the breach and have notified site users, advising them to change their passwords. Scripps indicated that, so far, they have received only a handful of related user inquiries.
(Gizmodo)