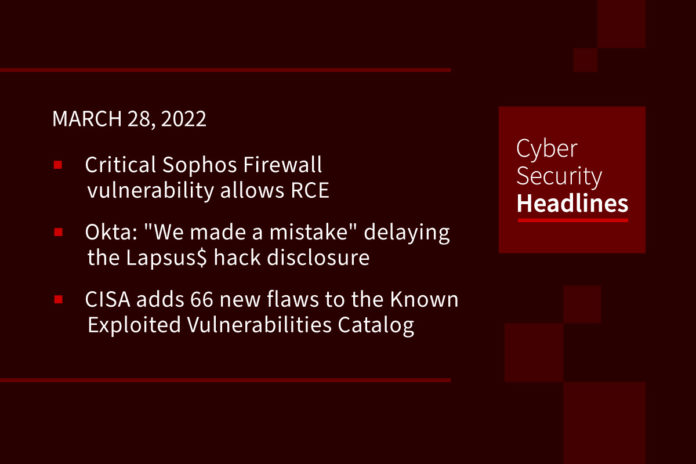
Critical Sophos Firewall vulnerability allows remote code execution
Sophos has fixed a critical vulnerability in its Sophos Firewall product that allows remote code execution (RCE). Assigned CVE-2022-1040 with a 9.8 CVSS score, the vulnerability allows a remote attacker who can access the Firewall’s User Portal or Webadmin interface to bypass authentication and execute arbitrary code. The vulnerability was responsibly reported to Sophos by an unnamed external security researcher via the company’s bug bounty program. Sophos has released hotfixes that should, by default, reach most instances automatically.
Okta: “We made a mistake” delaying the Lapsus$ hack disclosure
Okta has admitted that it made a mistake delaying the disclosure of hack from the Lapsus$ data extortion group that took place in January. Additionally, the company has provided a detailed timeline of the incident and its investigation activities. The hack from the Lapsus$ data extortion group originated at Sitel, Okta’s third-party provider of customer support services. “We want to acknowledge that we made a mistake,” states Okta, further admitting that it is ultimately responsible for its contracted service providers like Sitel. Okta claims that in January it wasn’t aware of the extent of the incident which, the company believed, was limited to an unsuccessful account takeover attempt targeting a Sitel support engineer. The incident has resulted in a 20 percent drop in Okta’s share prices as of Friday.
CISA adds 66 new flaws to the Known Exploited Vulnerabilities Catalog
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, Federal Civilian Executive Branch agencies have to address the identified vulnerabilities by April 15, 2022 to protect their networks against attacks exploiting the flaws in the catalog. Experts recommend also private organizations review the Catalog and address the vulnerabilities in their infrastructure. The oldest flaws in the set of 66 recently added issues are dated back to 2005, while the newest ones have a 2022 CVE date.
Google issues emergency fix for Chrome zero-day
Tracked as CVE-2022-1096 and considered high-severity, the security hole is described as a Type Confusion bug in the V8 JavaScript and WebAssembly engine. The bug was reported by an anonymous researcher, and Google has yet to determine the bug bounty amount for this issue. We are aware that an exploit for this bug exists in the wild, the company notes in its advisory, without providing further details on the vulnerability itself or on the observed exploitation. A patch for this flaw has been included in Chrome 99.0.4844.84, which is now rolling out for Windows, Mac and Linux users. This is not the same Zero-Day bug that we reported here on Friday as being exploited by North Korean threat actors.
Thanks to our episode sponsor, Varonis
Kaspersky added to FCC list that bans Huawei, ZTE from US networks
The security company is now being listed a company that poses “an unacceptable risk to the national security of the United States.” The decision essentially puts Kaspersky in the same class as Chinese telecommunications hardware makers Huawei and ZTE, which were among the first added to the list in 2021. In a public notice issued Friday, the agency said that the Kaspersky decision is based on a 2017 ruling by the Department of Homeland Security (DHS), which banned the company’s products and services from U.S. government use. Kaspersky states that such charges are unsubstantiated and suggests the ban has more to do with the current “geopolitical climate.”
(source)
Hackers remotely start, unlock Honda Civics with $300 tech
Keyless car entry exploits are nothing new. But this particular key fob hijack issue with some Honda vehicles manufactured between 2016 and 2020 is, according to The Register, a demonstration that auto manufacturers haven’t adapted their technology to keep up with known threats. This security weakness, tagged CVE-2022-27254, was discovered by Ayyappan Rajesh, a student at University of Massachusetts Dartmouth, along with someone with the handle HackingIntoYourHeart. According to the duo, various Honda vehicles send the same, unencrypted RF signal for each door-open, door-close, trunk-open and remote start. This allows for an attacker to eavesdrop on the request and conduct a replay attack.
‘Precursor malware’ infection may be a sign you’re about to get ransomware
Lumu Technologies founder and CEO Ricardo Villadiego suggests that “precursor malware,” which is essentially reconnaissance malicious code, lays the groundwork for a full ransomware campaign to come. Companies that can find and remediate that precursor malware can ward off the ransomware attack, he says. He bases his statements on a study of more than 2,000 companies that Lumu monitors, in which every ransomware attack came with other malware preceding it and paving the way. Lumu collected information from such aspects as DNS queries, network flows, access logs, firewalls and proxies and correlates the data to identify whether any asset is trying to contact an adversarial infrastructure. “A better way to operate, he says, “is by assuming you’re compromised and let your network prove otherwise.”
Frosties NFT operators arrested over $1.1 million ‘rug pull’ scam
Two alleged operators of the Frosties NFT rug pull have been arrested and charged by US law enforcement. The pair, both 20 years old, allegedly operated “Frosties,” a Non-Fungible Token (NFT) project that, at the outset, looked professional and offered quirky cartoon art. However , investors who handed over cryptocurrency to purchase the NFTs in January this year were alerted to a potential scam when the Frosties Discord server vanished alongside the original project’s Twitter profile, having briefly displayed the message, “I’m sorry.” Rug pulls are similar to exit scams performed by cryptocurrency exchanges and pump-and-dump meme stock frauds. The pair are facing 20 years for wire fraud if convicted and were working on a second NFT scam called “Embers” at the time of their arrest.
(ZDNet)