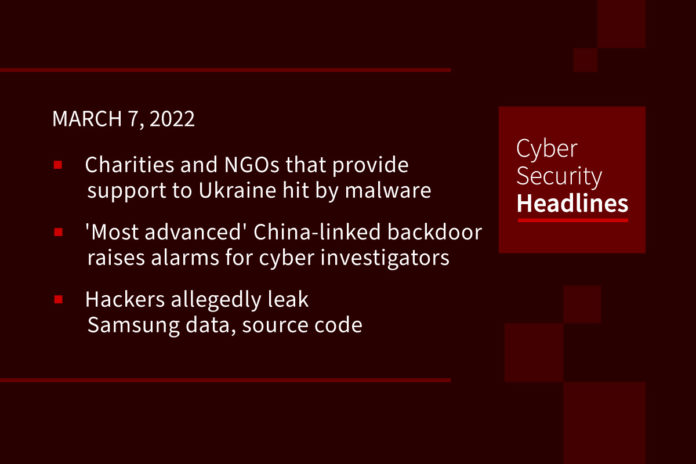
Charities and NGOs that provide support to Ukraine hit by malware
The report comes from Amazon, who is crediting the attacks to state-sponsored hackers while confirming that it, Amazon, is helping customers impacted by the attacks to adopt security best practices. Amazon did not name the impacted organizations, but it is known to be working with groups such as UNICEF, UNHCR, the Red Cross, and Save the Children. A few days ago, researchers from cybersecurity firm Proofpoint uncovered a spear-phishing campaign, likely conducted by a nation-state actor, that compromised a Ukrainian armed service member’s email account to target European government personnel involved in managing the logistics of refugees fleeing Ukraine.
‘Most advanced’ China-linked backdoor ever raises alarms for cyber-espionage investigators
A backdoor in use as recently as November 2021 is the “most advanced piece of malware” ever seen from China-linked spies, according to researchers at Symantec. Dubbed Daxin, the malware forms part of “a long-running espionage campaign against select governments and other critical infrastructure targets,” most of them being of strategic interest to China. The malware “appears to be optimized for use against hardened targets, allowing the attackers to burrow deep into a target’s network and exfiltrate data without raising suspicions,” the researchers said. Dick O’Brien, principal editor for the Symantec Threat Intelligence Team, told CyberScoop that for China-linked malware, this is “on another level.”
Hackers allegedly leak Samsung data, source code
Less than a week after releasing a 20GB document archive from 1TB of data stolen from Nvidia, the Lapsus$ data extortion group on Friday leaked a huge collection of confidential data they claim to be from Samsung Electronics. The leak apparently contains “confidential Samsung source code” for every Trusted Applet (TA) installed in Samsung’s TrustZone environment used for sensitive operations (e.g. hardware cryptography, binary encryption, access control), as well as algorithms for biometric unlock operations, bootloader source code for all recent Samsung devices, confidential source code from Qualcomm, source code for Samsung’s activation servers, and full source code for technology used for authorizing and authenticating Samsung accounts, including APIs and services. This is according to Bleeping Computer, who also state that if these details are accurate, Samsung has suffered a major data breach that could cause huge damage to the company.
Flaw in Linux Kernel groups feature allows container escape
A now-patched high-severity Linux kernel vulnerability, tracked as CVE-2022-0492 (CVSS score: 7.0), can be exploited by an attacker to escape a container to execute arbitrary commands on the container host. The issue is a privilege escalation flaw affecting the Linux kernel feature called control groups (groups), that limits, accounts for, and isolates the resource usage (CPU, memory, disk I/O, network, etc.) of a collection of processes. Major Linux distributors including Ubuntu, and Redhat, have now published advisories regarding this flaw.
There are many misconceptions about security automation, so Torq is debunking a security automation myth each day this week.

Incorrect. Proactive management of security incidents is just as important, like automatically scanning IaC configurations to detect vulnerabilities, automating collaboration between devs, IT ops and SecOps to prevent risks before they’re threats. To learn more about the realities of automation, head to torq.io.
Researchers devise attack for stealing data during homomorphic encryption
Researchers at North Carolina State University have developed what they claim is the first successful side-channel attack on an emerging security technology called homomorphic encryption, which, unlike typical encryption methods, allows for computing operations to be performed directly on encrypted data without the use of a secret key. The researchers’ technique involves a way to steal data even while it is in the process of being homomorphically encrypted. They liken the attack to lock-pickers in movies who listen to a safe to crack it, saying, “We do the same on computer hardware. We listen to the power consumption of a device as it computes some cryptographic operations. … Thereby, we can infer the actual computations going on.” They will present their findings at the virtual DATE22 conference on March 23.
Amid Russian invasion, Ukraine granted formal role with NATO cyber hub
Members of NATO’s cyber center of excellence this week voted unanimously to allow Ukraine to participate in its ongoing work. Ukraine was granted the formal role of “contributing participant” to the hub, known as the Cooperative Cyber Defence Centre of Excellence (CCDCOE), by its 27-member steering committee, the organization announced. Ukraine had requested contributing participant status to the center — based in Tallinn, Estonia — last year but at that time was denied. The center’s website lists the non-alliance countries of Austria, Switzerland, Sweden and Finland as contributing participants.
Meris botnet embeds ransomware notes in URL
Hey webop_geeks, you_are_already_dead, is a note claiming to be left by the REvil ransomware gang, embedded into the attack itself as a string of text in the URL for the extortion demand. Imperva’s Nelli Klepfish states, “We are observing more cases like this where the ransom note has been included as part of the attack itself, perhaps as a reminder to the target to send their bitcoin payment. Once the target receives this note, the attack is already underway, adding a sense of urgency to the threat.” Evidence points to the DDoS attacks coming from the massive Meris botnet. Meris sucks its power out of the thousands of internet-of-things (IoT) devices that have been hijacked thanks to a years-old vulnerability, tracked as CVE-2018-14847, in MicroTik routers.
Teen who tracked Elon Musk’s jet turns his attention to Russian oligarchs
In a new Twitter account created over the weekend, 19-year-old Jack Sweeney from Florida has already amassed nearly 162,000 followers as the teen tracks the private jets of at least 21 Russian billionaires and tycoons. According to the new account @RuOligarchJets, the private jets and helicopters of Roman Abramovich, owner of Chelsea Football Club, have been taking off and touching down in various destinations including Moscow, Baku, Saint Kitts and Nevis and Dubai as of Monday. In addition to tracking flight movements, Sweeney also tracks other measures including fuel usage and cost.