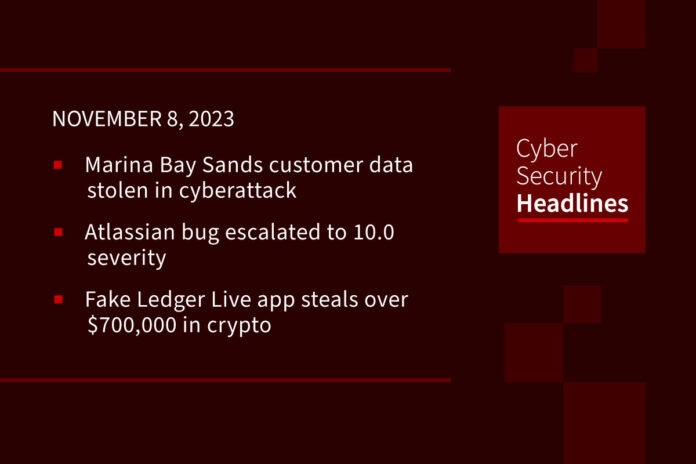
Singapore’s Marina Bay Sands customer data stolen in cyberattack
The Marina Bay Sands (MBS) luxury resort and casino in Singapore has disclosed a data breach that impacts personal data of 665,000 customers. The incident affected MBS loyalty program member data and was discovered by the company on October 20, just a day after the attack began. Exposed data includes names, email addresses, phone numbers, country of residence and membership information. This data could allow attackers to target victims with phishing and social engineering attacks, though the company said so far there is no evidence that their members have been impacted by the incident. The incident is still under investigation and the nature of the attack has not yet been disclosed.
(The Record & Bleeping Computer)
Atlassian bug escalated to 10.0 severity
The severity rating for a bug in all on-premises versions of Atlassian Confluence Data Center and Server technology (CVE-2023-2251) has been increased from 9.1 to the most critical rating of 10.0. An Atlassian advisory explains that the severity rating was raised due to ongoing active exploits against the bug, including ransomware. Researchers at Rapid7 also issued an advisory warning of snowballing attacks starting over the weekend. The vulnerability allows unauthenticated attackers to reset Confluence and create an administrator account. Atlassian said it can’t confirm which customer instances have been impacted by the active attack, but has published indicators of compromise for security teams and admins to research.
Fake Ledger Live app steals over $700,000 in crypto
A fraudulent cryptocurrency management app called Ledger Live Web3 was published in the Microsoft Store on October 19. On November 5, a member of the crypto community warned that the app had stolen $600,000 in crypto from its users. Microsoft took immediate action, removing the app the same day, but not before the crooks had already transferred more than $768,000 from victims. The fraudsters listed the developer name as “Official Dev” and the app had just one five-star rating at the time of its takedown. Given the numerous warning signs that the app was a potential scam, some are questioning the thoroughness of Microsoft’s application vetting process.
23andMe data theft prompts DNA testing companies to bolster security measures
Following the theft of millions of user records from 23andMe as a result of a suspected credential stuffing attack, other DNA testing and genealogy companies are stepping up user account security. Ancestry is notifying customers that they will need to use multi-factor authentication to log into their account in order to view their DNA matches. This requirement will go into effect by the end of the year. Additionally, MyHeritage said in a blog post last week that two-factor authentication will soon be made a requirement for its customers and cited the data theft at 23andMe. For its part, 23andMe also said this week that it was also requiring all customers to use a second step of verification for their account sign-ins.
Huge thanks to our sponsor, Offsec

During the event, you’ll learn how to attract and assess top talent, how to craft positioning for budget conversations, why CISOs make great board members, and more.
Hear from forward-thinking infosec leaders from companies like CISCO, Amazon, and Salesforce.
Save your seat and equip yourself with actionable takeaways to help shape the future of your organization’s security.
Register now at offsec.com/evolve
Free tool helps industrial organizations find vulnerabilities
OPC UA is a machine-to-machine communication protocol used by many industrial solutions providers for interoperability between various types of industrial control systems (ICS). While the protocol is highly useful, it can also pose a serious risk to organizations. Finland-based cybersecurity company Molemmat Oy, has developed a new vulnerability scanning tool, called OpalOPC, to help identify weaknesses in the protocol. OpalOPC is available for both Windows and Linux and is free for non-profit projects and organizations whose revenue does not exceed $1 million.
Microsoft Authenticator has blocked millions of hacker-initiated MFA notifications
Microsoft’s Authenticator app provides multi-factor authentication, password auto-fill, and passwordless sign-in to Microsoft accounts. Back in May, Microsoft implemented number-matching MFA, a more secure alternative to push notifications which attackers take advantage of by inundating users with MFA approval requests (referred to as “MFA bombing”). Even with the more secure number-matching, users still received annoying prompts when an unauthorized user attempts to access their account. To combat this, Microsoft added new features that scrutinize login attempt details and block them if they are suspicious. Since completing the roll-out of the blocking feature in late September, Microsoft has blocked over six million MFA notifications suspected to have been initiated by hackers.
GootBot implant heightens risk of post-infection ransomware
In an advisory published Monday, the IBM X-Force team said it has spotted a new implant called “GootBot.” The implant is a variant of the notorious Gootloader malware which has typically been used to gain initial access. However, GootBot is being utilized for lateral movement after initial Gootloader infection, receiving PowerShell commands from command-and-control (C2) server which allow it to move laterally. Of particular concern is the fact that GootBot implants currently maintain zero antivirus detections.The Gootloader group has a history of using Search Engine Optimization (SEO) poisoning to manipulate search engine results, to lure victims to compromised websites where they may unwittingly download the initial payload.
Data brokers expose sensitive US military member info to threat actors
On Monday, researchers from Duke university published a study showing how easy it is to purchase information on military service members and veterans from US data brokers. While some brokers refused to sell the data to an unverified organization, others were more concerned with ensuring confidentiality of the purchase transactions rather than the confidentiality of the actual data. The researchers managed to acquire sensitive information for as little as $0.01 per individual for bulk purchases. The researchers also successfully purchased data from several brokers using a .asia domain name that had been linked to a Singaporean IP address. The researchers recommended that lawmakers pass a comprehensive privacy law with strong controls on the data brokerage ecosystem and urged Congress to provide more funding to regulatory agencies that can enforce new policies.