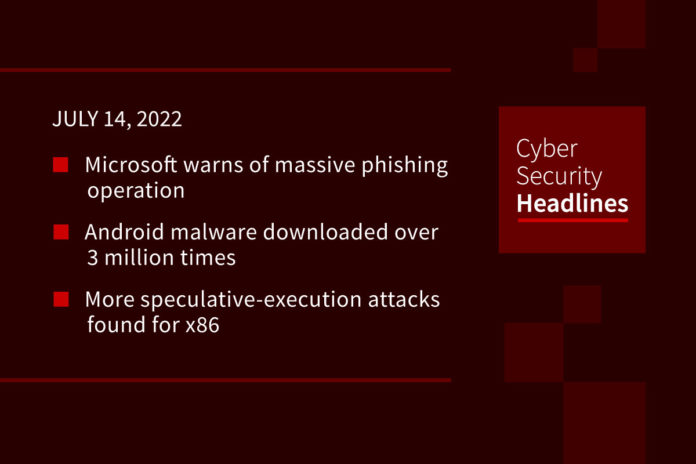
Microsoft warns of massive phishing operation
The company warned of a massive series of phishing attacks targeting over 10,000 organizations since September 2021. These attacks use landing pages designed to spoof the Office online authentication page, stealing credentials and session cookies even for users using multifactor authentication. These are then used to access mailboxes for business email compromise attacks. Microsoft suggests organizations implement MFA with certificate-based authentication and FIDO 2.0 support to mitigate this scheme. It maintained that while some implementations of MFA are vulnerable to these phishing approaches, it should remain “an essential pillar in identity security.”
Android malware downloaded over 3 million times
Evina security researcher Maxime Ingrao documented a malware named Autolycos distributed in eight Android applications, two of which are still available in the Play Store at the time of writing. Two of the removed apps had over one million downloads each. The apps request permission to read SMS content, and generally seek to subscribe users to premium services. Rather than just relying on users finding the apps with lookalike names in the Play Store, the operators also advertised for them on social media. Ingrao discovered the apps in June 2021 and reported findings to Google.
More speculative-execution attacks found for x86
Researchers at ETH Zurich discovered an issue impacting older AMD and Intel CPUs dubbed Retbleed, the latest in a class of Spectre-like attacks that exploit speculative execution methods with side channel attacks to execute arbitrary code. Retbleed specifically is designed to get around so-called “return trampoline” measures to prevent branch target injections to hijack return instruction in the kernel to gain arbitrary speculative code execution. Intel said its enhanced Indirect Branch Restricted Speculation already default in Windows addresses the vulnerability, while AMD introduced a mitigation called Jmp2Ret.
Multiple states investigating Celsius
Vermont’s Department of Financial Regulation announced it joined a multistate investigation into the crypto lender Celsius Network, along with Alabama, Kentucky, New Jersey, Texas, and Washington. The DFR said it believed Celsius to be “deeply insolvent” and does not have assets to meet its obligations. Celsius operated with traders in Vermont without a money transmitter license and largely without regulatory oversight. The DFR said because it did not register interest-earning accounts as securities, customers did not receive disclosures about its risks, ability to repay or financial condition.
(Reuters)
Thanks to today’s episode sponsor, Edgescan

Callback phishing scams impersonate security companies
A new report from the legitimate cybersecurity company CrowdStrike detailed a callback phishing campaign with threat actors impersonating CrowdStrike. Over the past year, the actors would leave messages with companies claiming to be from the security vendors, asking them to call back to resolve a problem or cancel a subscription. Once an organization calls back, the attackers use social engineering to get them to install remote access software. In an update to the campaign, the attackers warn recipients of malicious network intruders compromising workstations, requiring an in-depth security audit that requires access to the device. From there the attackers walk through the employee installing a remote access trojan. CrowdStrike believes the ultimate intention is to launch ransomware on these organizations, and shows ties to the Quantum ransomware gang.
Honda unlock hack update
Earlier this week, we covered a report from Star-V Lab about an exploit in Honda’s rolling code system that could allow for unlocking and starting of vehicles going back to 2012. Initially Honda said the report did not include enough evidence to support the researcher’s claims. A spokesperson subsequently confirmed the reports findings, but said that hackers would need “sophisticated tools and technical know-how” to mimic it. Honda also said that all 2022 and 2023 models use an “improved system” that addresses the issue.
Threat actors don’t have to get fancy
Sometimes you don’t need to be sophisticated to be effective. The operators of the threat group Luna Moth operate a classic phishing campaign. Sending messages from Zoho and Duolinger, the group requests subscriptions payments and attaches a PDF with contact info for issues. Calling will result in a threat actor attempting to install the Atera remote access trojan or just ues off-the-shelf remote administration tools like Splashtop. Some researchers even saw Luna Moth using Rclone. Ultimately the group attempts to exfiltrate data from compromised systems. After that, it approaches the user for a ransom, without really doing the whole ransomware thing.
New Lenovo UEFI flaws discovered
Researchers at ESET discovered two issues in Lenovo UEFI firmware that make the machines vulnerable to buffer overflow attacks. These impact over 70 Lenovo laptop models, including its popular Yoga, IdeaPad, and ThinkBook lines. These could be chained to disable security features on the machines. Lenovo issued fixes for these vulnerabilities. While these cannot generally be exploited by low-skilled remote actors, these vulnerabilities can impact systems before Windows security services boot, making them particularly problematic.