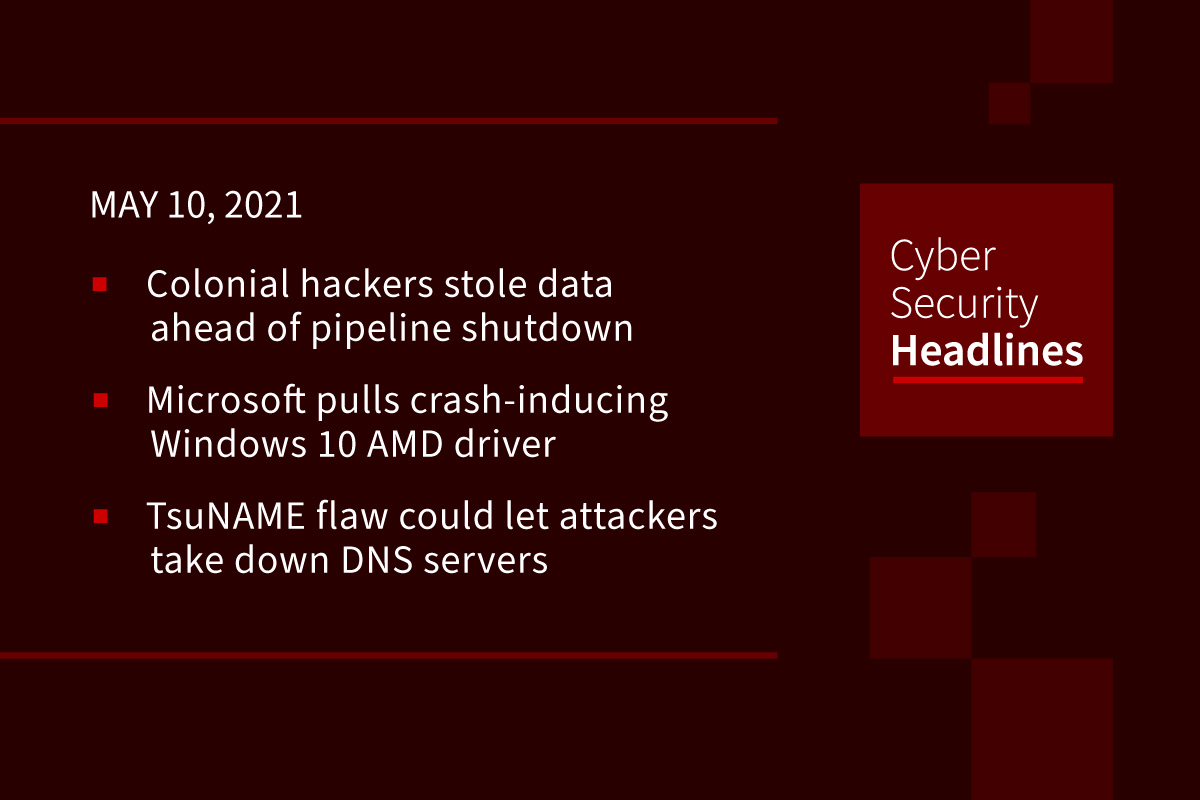
Colonial hackers stole data ahead of pipeline shutdown
The hackers who caused Colonial Pipeline to shut down the biggest U.S. gasoline pipeline on Friday began their blitz against the company a day earlier, stealing a large amount of data before locking computers with ransomware and demanding payment, according to Bloomberg. A cybercrime gang called DarkSide, took nearly 100 gigabytes of data out of the Alpharetta, Georgia-based company’s network in just two hours on Thursday, as part of a double extortion scheme. Colonial made the decision late Friday to shut down the pipeline that is the main source of gasoline, diesel and jet fuel for the East Coast, without saying when it would reopen.
Microsoft pulls Windows 10 AMD driver causing PCs not to boot
For the past week, Windows Update had been pushing a new driver titled Advanced Micro Devices SCSI Adapter 9.3.0.221 to users of AMD-compatible motherboards. Numerous users reported that installing this driver resulted in a prompt to restart Windows 10 but were then greeted with a Blue Screen of Death crash (BSOD) displaying an INACCESSIBLE BOOT DEVICE error message. Due to the large number of people affected by the driver rollout, Microsoft pulled the driver last Wednesday.
New TsuNAME flaw could let attackers take down authoritative DNS servers
Security researchers Thursday disclosed a new critical vulnerability affecting Domain Name System (DNS) resolvers that could be exploited to carry out reflection-based denial-of-service attacks against authoritative nameservers. Called TsuNAME, the vulnerability occurs when domain names are misconfigured with cyclic dependent DNS records, leading vulnerable resolvers to “simply bounce back from zone to zone, sending non-stop queries to the authoritative servers of both parent zones.” To mitigate the impact of TsuNAME in the wild, the researchers have published an open-source tool called CycleHunter that allows for authoritative DNS server operators to detect cyclic dependencies.
Chinese smart TVs caught collecting data on customers’ networks
The owner of a Skyworth smart TV who had noticed its operation slowing down examined its Android-based code and discovered it was scanning for devices connected to their family’s Wi-Fi every 10 minutes. It was scooping up the hostname, mac address, IP, network delay time, surrounding wifi SSID names, and then sending them to Gozen Data, a data analytics company that specializes in delivering targeted advertising to smart TVs. Skyworth, the third-largest TV brand by sales in China, says is has now ended its “cooperation” with Gozen Data and demanded that the company delete all of its “illegally” collected data.
Thanks to our episode sponsor, Altitude Networks

Biggest US ISPs paid for 8.5 million fake FCC comments opposing net neutrality
Some of the largest Internet providers in the US funded a campaign that generated “8.5 million fake comments” to the Federal Communications Commission as part of the ISPs’ fight against net neutrality rules during the Trump administration, according to a report issued last week by New York State Attorney General Letitia James. The industry campaign was run through Broadband for America (BFA), an umbrella group that includes Comcast, Charter, AT&T, Cox, and CenturyLink and allegedly used third party vendors to fabricate comments and attach them to real names and email addresses.
China’s PLA Unit 61419 purchasing foreign antivirus products
Recorded Future’s Insikt Group has discovered six procurement documents from the websites of the official People’s Liberation Army (PLA) military unit 61419 that show its intent to purchase English language versions of antivirus software from companies like Kaspersky, Norton, Symantec and others. Insikt points out that Chinese-language versions of the software would be the more logical choice if it was intended for legitimate use. Insikt suggests that given unit 61419’s extensive history in software supply chain exploitation, the antivirus brands listed in its report should be closely monitored. The report can be found at Recorded Future, dated May 5.
Cisco HyperFlex web interface has critical flaw
Cisco has revealed a pair of critical bugs in its HyperFlex hyperconverged infrastructure product that lets attackers get root access and allows them to execute arbitrary commands. Their advisory states that “this vulnerability is due to insufficient validation of user-supplied input. An attacker could exploit this vulnerability by sending a crafted request to the web-based management interface.” The HX VM is used to install and manage VMs, so the flaws have enormous potential for a miscreant to go on a rampage, however, Cisco says it has not yet seen the flaws exploited in the wild.
IRS to serve Kraken with customer data request re: cryptocurrency traders
In the latest crackdown centered on cryptocurrency trading, the IRS has been granted permission by a federal court in the Northern District of California to issue a “John Doe” summons on the owners of Kraken, in order to obtain information on US taxpayers who have conducted at least $20,000 worth of cryptocurrency trades on the platform between 2016 and 2020. A John Doe order is issued in circumstances when individuals have not been identified. The summons does not imply wrongdoing on the part of Kraken itself.
(ZDNet)