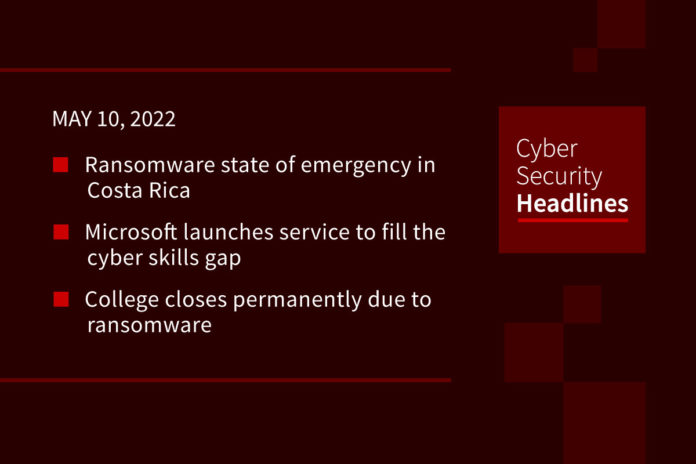
Ransomware state of emergency in Costa Rica
Newly sworn in Costa Rican President Rodrigo Chaves wasted no time in declaring a state of emergency, citing recent cyberattacks from the Conti ransomware group that hit multiple government agencies. Conti actors initially claimed to have attacked Costa Rican agencies last month, impacting digital services from the Treasury, the The Ministry of Science, Innovation, Technology, and Telecommunications, and the Costa Rican Social Security Fund, among others. Bleeping Computer observed Conti published most of 672GB data dump that appears to belong to Costa Rican agencies. Conti operators appeared to initially ask for a $10 million ransom from the Costa Rican ministry.
Microsoft launches service to fill the cyber skills gap
Microsoft announced three new managed security services under its new Microsoft Security Experts suite. The company says these are designed for organizations of any size impacted by the ongoing cybersecurity skills shortage. Microsoft Defender Experts for XDR will enter into preview this fall, effectively offering a managed version of Microsoft 365 Defender. Security Services for Enterprise officially launched in full, offering security consulting services from the company. And a preview of Microsoft Defender Experts for Hunting launched, which looks for threats across a customer’s endpoints and cloud applications.
(Protocol)
College closes permanently due to ransomware
Lincoln College informed the Illinois Department of Higher Education and Higher Learning Commission that it will close its doors as of May 13th. This is believed to be the first US college to shutter operations as a result of a ransomware attack. In December, the college was hit by a ransomware attack, “hindered access to all institutional data” and took down all systems around recruitment, retention, and fundraising. Lincoln College restored access in March 2022, but combined with falling enrollment due to the COVID-19 pandemic, could not find a viable way forward with operations.
(Engadget)
Tech trade groups comes out against India’s reporting mandate
We reported last week on updates to India’s Information Technology (IT) Act that would require reporting cybersecurity incidents within six hours to government regulators. Unsurprisingly the industry trade group ITI, which includes Apple, Google, Microsoft, Adobe, Visa and other tech giants has publicly come out against the revisions. The trade group was critical of the overly broad criteria of reporting incidents, saying “ these provisions may have severe consequences for enterprises and their global customers without solving the genuine security concerns.” ITI made the case that a 72-hour window would be more reasonable to sort out any false positives from an organization.
Thanks to our episode sponsor, Datadog

Watch the on-demand webinar now to learn how to get full-stack security for your production environment at datadoghq.com/ciso/
Researchers warn of cheap trojan for sale
Security researchers at BlackBerry warned of a remote access trojan called DCRat available for sale on Russian forums with a starting price of around $5 USD for a two-month license. This makes it one of the cheapest available commercial RAT products found by researchers. It appears to be the work of a lone malware author, although the researchers found it is actively maintained, with a modular structure written in .NET. The price seems to have made the malware more popular of late, but it first appeared on the threat landscape in 2018, although seems to have been redesigned and relaunched a year later.
US offers Conti bounty
The US Department of State issued a notice offering up to $15 million for information on the leaders of the Conti ransomware group, or for any individuals participating in an attack. In the notice announcing the bounty, the State Department said it was the costliest strain of ransomware on record, impacting over 1000 victims as of the start of 2022. Back in May 2021, the FBI sent out an alert on Conti, saying at that time that it was responsible for over 400 attacks. This isn’t the first bounty by the State Department, offering a similar chunk of change for information on the leads of the Darkside and REvil ransomware groups.
Nvidia crypto limited bypassed
Last year, Nvidia released RTX 3000 series GPUs with a Lite Hash Rate limiter, making them inefficiency for cryptocurrency mining in the hopes this would improve the supply situation for gaming GPUs. The developers of the cryptocurrency mining software NiceHash announced they successfully bypassed Nvidia’s this limiter. Techspot reports several benchmarking sites have confirmed NiceHash’s claims. Earlier this year, a claimed mitigation for Nvidia’s cards turned out to be malware.
(TechSpot)
And now your Should Have Patched Tuesday Update
F5 notified users of its BIG-IP application delivery controllers of 18 high-severity vulnerabilities. One is deemed critical, allowing for an unauthenticated attacker with network access to execute system commands. Security researchers at Armis discovered vulnerabilities in network equipment from Aruba and Avaya, dubbed “TLStorm 2.0” that misuse the NanoSSL TLS library to potentially break network segmentation. Armis said there’s no evidence of these being exploited and worked with the vendors to issue patches. And the package management site RubyGems.com patched a server-side vulnerability that could have allowed attackers to remove a third-party package.