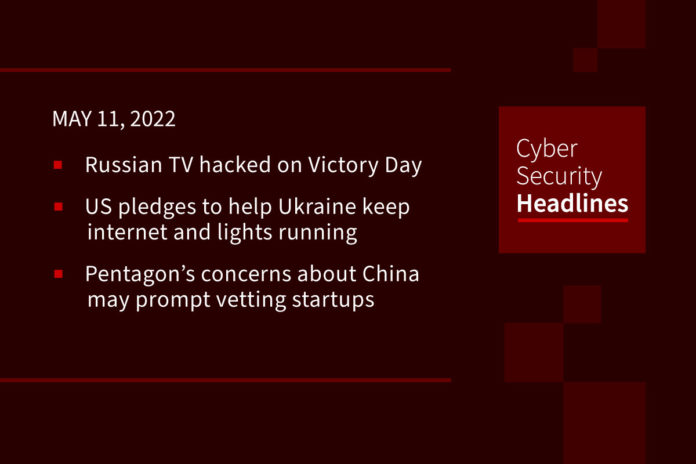
Russian TV hacked on Victory Day
Early Monday morning, as Russian TV stations prepared to air Vladimir Putin’s annual Victory Day Parade held at Red Square, pro-Ukrainian hackers took aim at the TV outlets, posting anti-war messages including, “the blood of thousands of Ukrainians and hundreds of their children in on your hands.” The hack, which is likely the work of Anonymous, affected online streaming and satellite broadcasts of several providers and also disrupted TV Zvezda, a channel run by the Russian Defense Ministry.
US pledges to help Ukraine keep internet and lights running
On Tuesday, the US State Department announced a coordinated governmental effort to help Ukraine protect their electrical grid and internet access. Aid will include FBI intelligence on cyberattacks planned against Ukraine, technical support and thousands of communications devices (such as data terminals and satellite phones) provided by the US Agency for International Development (USAID) and CISA, and the Department of Energy helping integrate Ukraine’s electrical grid with the European Network of Transmission system Operators for Electricity (ENTSO-E), which will help bolster both security and resiliency.
Pentagon’s concerns about Chinese interests may prompt vetting startups
Congress may soon require government agencies to vet tech startups seeking federal funding, after a Defense Department study found that China is benefiting from the Pentagon’s Small Business Innovation Research program (SBIR). The report highlighted several case studies which have “national and economic security implications” including American companies dissolving so its members could join Chinese government talent programs as well as venture-capital recipients redirecting funds to Chinese organizations supporting the country’s defense industry. The report concludes that the SBIR program, which expects to award $3.9 billion this year, requires enhanced due-diligence and oversight.
(WSJ)
Security assessments significantly impacting vendors
A new study by Whistic highlights the business impacts of performing vendor security assessments. The report found that, with the rise in data breaches caused by third-party vendor vulnerabilities, the number of vendors assessed annually increased by 20% from the prior year. And while vendors invest significant time and resources into undergoing SOC2 and ISO27001 assessments, 77% of companies indicate it is Very Likely or Likely that they will still ask for additional security documentation. Unfortunately, these assessments are not standardized with 82% of companies using fully or partially customized security questionnaires to evaluate their vendors. On average vendors are spending over 80 hours per month responding to security assessments with 79% percent of them saying these assessments add a week to the sales cycle, or more if their customers need clarification on any of their responses.
(Whistic)
Thanks to our episode sponsor, Datadog

Built on top of the observability platform, Datadog brings unprecedented integration between security and devops aligned to shared organizational goals.
Watch the on-demand webinar now to learn how to get full-stack security for your production environment at datadoghq.com/ciso/
UK government takes down 2.7 million scams
UK’s National Cyber Security Centre (NCSC) said on Tuesday that it stalwarted 2.7 million internet scams last year as part of its Active Cyber Defence (ACD) initiative. Malicious campaigns included fake celebrity endorsements,vaccine-related scams, bogus extortion emails, and even emails impersonating the NCSC’s own CEO Lindy Cameron. The agency’s takedown tally was nearly four times greater than in 2020 due, in large part, to its newly introduced Takedown Service. The initiative also blocked more than 1.2 million domains linked to Android Flubot malware, while roughly 33 million organizations signed up for the agency’s early vulnerability warning service. More than 10,000 organizations leveraged the NCSC’s Exercise in a Box toolkit designed to enhance incident response.
Malware goes regional as attackers change tactics
The new Cloud and Threat Report from Netskope reveals that most malware attacks now originate from the same region as the victim, representing a marked tactical shift by threat actors. Netskope attributes this to attackers attempting to avoid geofencing filters and other prevention measures. Additional report findings saw Trojans accounting for 77 percent of all malware downloads, with attackers using social-engineering techniques to get malicious payloads past their victims. Nearly half (47%) of malware downloads originate from cloud apps. On a positive note, attacks involving malicious Microsoft Office documents are on the decline.
You should probably patch that (continued)
Following up on the F5 BIG-IP remote code execution vuln we reported on last week, cybersecurity researchers are warning that threat actors are now exploiting the critical bug to deliver malicious code. Meanwhile, Microsoft’s May 2022 Patch Tuesday addresses three zero-day vulnerabilities, including one related to Windows LSA Spoofing which is being actively exploited. The other two zero-days allow for DoS attacks in Hyper-V and remote code execution (RCE) attacks in Azure Synapse and Data Factory, with public exploits now available for both of these bugs. In total, Microsoft fixed 75 flaws, eight which are rated critical.
(Security Affairs and Bleeping Computer)
China scrapping millions of computers over security concerns
Due to software security concerns emerging from the US Tech war, China has directed its government agencies to discard over 50 million computers within the next two years. As per the plan, all Microsoft-owned Windows operating systems will be replaced with new home-grown OS software and any incompatible hardware will also need to be replaced. China has yet to take a strict stance on use of Microsoft-owned products at private companies.