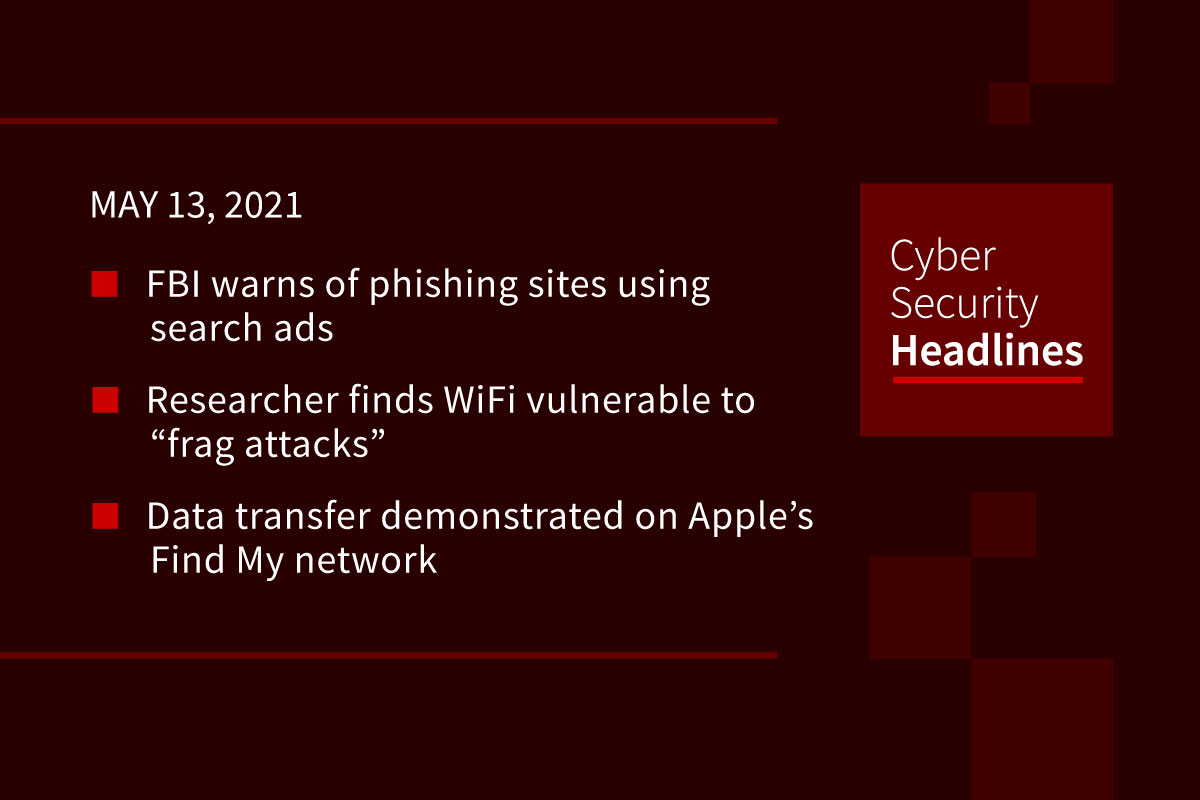
FBI warns of phishing sites using search ads
The agency sent out a private industry notification to the US private sector describes a phishing campaign impersonating an unnamed financial institution. One version of the scheme relied on getting traffic using search engine ads, with another version relied on surfacing a phishing site in organic search results. Regardless of the approach, the goal was to lead victims to a seemingly legitimate banking portal to input account credentials and answer security questions. If this information did not grant the threat actors access, they would also call the victim under the guise of “restoring account access” to get further information. The FBI said this specific scheme has been ongoing since March 2021, but Catalin Cimpanu at The Record reports that this tactic has exploded in popularity since mid-2020.
Researcher finds WiFi vulnerable to “frag attacks”
Belgian security researcher Mathy Vanhoef published details of so-called WiFi “frag attacks,” which uses several vulnerabilities in the WiFi standard to inject plaintext frames or malicious code into a protected Wi-Fi network, although these attacks require user interaction or uncommon network settings. These exploits could ultimately be used to intercept traffic by tricking the victim into using a malicious DNS server. Some of these bugs in the standard date back to 1997. Vanhoef disclosed the bugs to the WiFi Alliance prior to publishing his result, with patches from Microsoft, the Linux kernel, and numerous network vendors either now available or announced.
(Engadget)
Data transfer demonstrated on Apple’s Find My network
In a blog post published Wednesday, security researcher Fabian Bräunlein demonstrated how Apple’s Find My network can be exploited to transfer data. By faking the way an AirTag broadcasts its location as an encrypted message, the hack lets packets of arbitrary data be transmitted over the Find My network, which is capable of using the data connection of any nearby Apple device with Find My enabled. By simulating a Find My broadcast, what would be encrypted as a GPS location encodes arbitrary data instead. In Braunlein’s demo, short text strings are sent back over the Find My network to a home Mac. It’s not clear if this could be used maliciously.
(9to5Mac)
Missed patches a major cause of government security incidents
A new report from BAE Systems Applied Intelligence found that 63% of managers in UK central governmental organizations experienced a security incident in the past six-months, with 52% of those coming from missed patches. Interestingly, security considerations were virtually tied with integration issues as the most common barrier to upgrades with 68% and 69%, respectively. Overall 60% of departments had digital transformation plans in place, with 75% of those motivated by a desire to mitigate the risk of security vulnerabilities.
Thanks to our episode sponsor, Altitude Networks

Xiaomi removed from US investment ban
Xiaomi and the U.S. Defense Department reached an agreement to remove Xiaomi from a list of firms barred from US investment. The Defense Department put Xiaomi on the list earlier this year, claiming it was a supplier for the Chinese military. Xiaomi filed a lawsuit against this, saying being placed on the list would cause irreparable harm, and U.S. District Judge Rudolph Contreras issued an initial injunction on the order in March, ruling that Xioami was likely to win the lawsuit in litigation. The Defense Department and Xiaomi are now negotiating over specific terms and will file a separate joint proposal before May 20.
Microsoft warns of campaign against aviation organizations
The company warned about an ongoing spear-phishing campaign targeting aerospace and travel organizations using multiple remote access trojans. The attackers send spoofed emails appearing from legitimate organizations with malicious attachments claiming to have aviation, travel, and cargo data. The malware uses a new Snip3 loader, which is able to identify sandboxing and virtual environments to better avoid detection. Once installed, Microsoft observed the trojans attempting to “steal credentials, screenshots and webcam data, browser and clipboard data, system and network into, and exfiltrates data often via SMTP Port 587.”
Babuk leaks ransomware negotiations with Washington DC PD
The ransomware operators claimed to have stolen 250GB of data from the Washington D.C. Metropolitan Police Department last month, asking for a $4 million ransom to not expose the data. The group has now leaked alleged conversations with the police department, showing that negotiators offered $100,000 to prevent the release of the data, which was turned down by the Babuk operators. Following the breakdown of negotiations, the operators began leaking alleged “background investigations” on police officers that includes psychological evaluations, polygraph responses, supervisor interviews, their credit history, information about their home, their social security numbers, date of birth, personal emails, home address, phone numbers, their driver’s licenses, financial details, and their handwritten signatures.
AWS System Manager misconfigurations lead to data leaks
A new report by Check Point research found that these Services System Manager configuration errors potentially exposed 5 million documents with personally identifiable information and credit card transactions on more than 3,000 SSM documents. By default SSM documents are set to private, but can be shared with other AWS accounts or just set to public. Essentially the researchers found that developers didn’t follow published AWS best practices when managing SSM documents. Check Point warned that these documents could give attackers insight into internal resources and operations of an organization needed to pull off social engineering attacks.