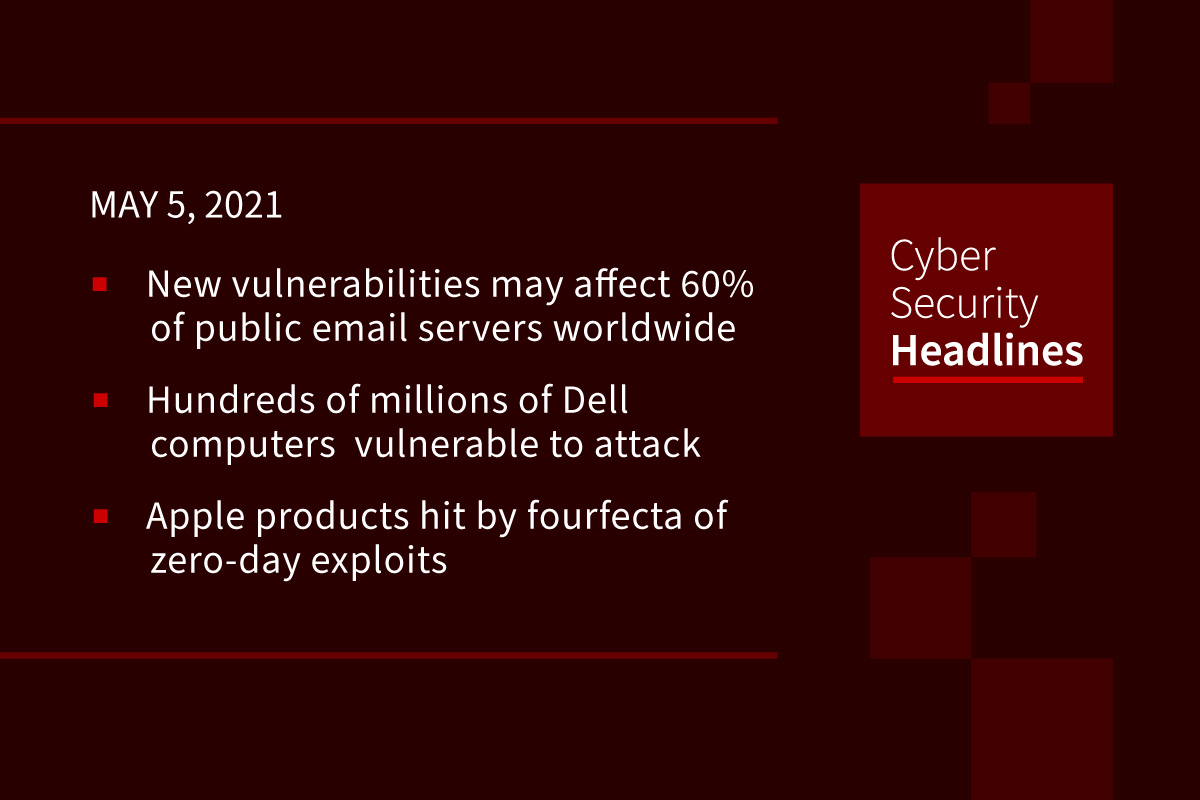
A new set of vulnerabilities may affect 60 percent of the world’s public email servers
The Qualys Research Team has discovered 21 vulnerabilities in the Exim mail server, some of which can be chained together to obtain full remote unauthenticated code execution and gain root privileges. Qualys has named this group of vulnerabilities “21 Nails”. Bharat Jogi, Senior Manager, Vulnerability and Threat Research at Qualys, said in a statement that “the 21 vulnerabilities we found are critical as attackers can remotely exploit them to gain complete root privileges on an Exim system, allowing compromises such as a remote attacker gaining full root privileges on the target server and executing commands to install programs, modify data, create new accounts, and change sensitive settings on the mail servers. It’s imperative that users apply patches immediately.”
Hundreds of millions of Dell computers potentially vulnerable to attack
Laptops, notebooks, and tablets made by DELL are at risk of compromise from a set of five high-severity flaws that had been undetected since at least 2009. The flaws allow an attacker who already has some level of initial access on a system to escalate privileges and gain kernel level access on it. Security researchers from SentinelOne discovered the bugs in Dell’s DBUtil, a driver that is installed and loaded during the BIOS update process on Dell Windows machines. Dell was notified of the issue in December 2020 and has issued an update for it. In an advisory and FAQ today, the hardware maker offers measures that organizations can take to identify whether they have been impacted and steps they can take to address the issue.
Apple products hit by fourfecta of zero-day exploits
Apple on Monday released security updates for iOS, iPadOS, macOS, and watchOS to address three zero-day flaws and expand patches for a fourth vulnerability that the company said might have been exploited in the wild. These latest patches focus on four CVE-numbered critical bugs described as maliciously crafted web content [that] may lead to arbitrary code execution. Shortened into contemporary jargon, that means “drive-by, web-based zero-day RCE exploit.” Drive-by means that just visiting a website and viewing it is enough to trigger the bug, so users only need to be lured onto a booby-trapped site to take a look. Apple recommends seeking updates immediately.
(Naked Security and The Hacker News)
Double Trouble: Worldwide phishing attacks deliver three new malware strains
The attacks hit at least 50 organizations from a wide variety of industries in two waves, first on December 2nd and then between December 11th and 18th, according to a Mandiant report published yesterday. The “uncategorized” threat group named UNC2529, has deployed three new malware strains onto targets’ computers using custom phishing lures. The malware is heavily obfuscated to hinder analysis, and evades detection by deploying payload in-memory whenever possible. The strains are named DOUBLEDRAG, DOUBLEDROP and DOUBLEBACK.
Thanks to our episode sponsor, Boxcryptor
Belgium’s government network goes down after massive DDoS attack
The attack targeted Belnet, a government-funded ISP that provides internet connectivity for Belgian government organizations, such as its Parliament, educational institutes, ministries, and research centers. The incident, which Belnet is still dealing with at the time of writing, is believed to have impacted the activities of more than 200 Belgian government organizations including its tax- and form-filing portal, and vaccine reservation registry. Neither Belnet nor any other Belgium government organization have attributed the DDoS attack to any particular entity.
New Pingback malware uses ICMP tunneling to evade detection
Researchers from Trustwave on Tuesday disclosed a malware that evades detection while executing arbitrary commands on infected systems. Called ‘Pingback,’ the Windows malware leverages Internet Control Message Protocol (ICMP) tunneling for covert bot communications, allowing the adversary to utilize ICMP packets to piggyback attack code. “ICMP tunneling is not new,” the researchers said, “but this particular sample is a real-world example of malware using this technique to evade detection…ICMP is useful for diagnostics and performance of IP connections, [but] it can also be misused by malicious actors to scan and map a target’s network environment. While we are not suggesting that ICMP should be disabled, we do suggest putting in place monitoring to help detect such covert communications over ICMP.”
Health care giant Scripps Health hit by ransomware attack
Nonprofit health care provider Scripps Health in San Diego is currently dealing with a ransomware attack that forced the organization to suspend user access to its online portal and switch to alternative methods for patient care operations. Following the attack, patient services have been offline and some critical-care patients have been redirected to other hospitals, according to local media reports. On Sunday, the health care provider explained in a message that “patient care continues to be delivered safely and effectively at our facilities,” despite IT applications being offline due to established backup processes.
SpaceX launches 60 more Starlink satellites, claims over 500,000 service pre-orders so far
This new addition, just five days after it launched the last batch means the company has now delivered 420 Starlink satellites since the beginning of March, for a total of over 1400 in operation. This constellation, built for broadband service has received “over half a million” pre-order reservations for its service so far, which includes advance deposits on the hardware.