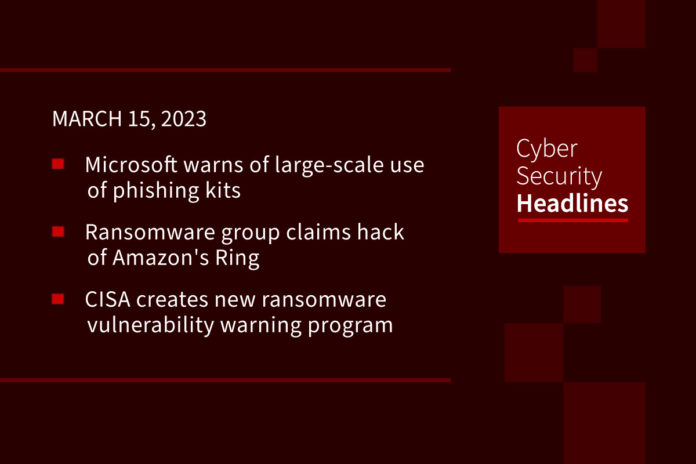
Microsoft warns of large-scale use of phishing kits to send millions of emails daily
Microsoft Threat Intelligence is tracking a threat actor behind the development of an open source adversary-in-the-middle (AiTM) phishing kit capable of orchestrating attacks at scale. The group has been named DEV-1101. AiTM phishing attacks are effective due to their ability to get around multi-factor authentication. DEV-1101 is said to be behind phishing kits that can be purchased or rented which cuts down on the effort and resources required to launch a phishing campaign.
Ransomware group claims hack of Amazon’s Ring
The ransomware group ALPHV whose malware is known as BlackCat, is claiming responsibility for breaching the Ring security camera company, owned by Amazon. The gang is threatening to release Ring’s data. Ring told Motherboard “it does not have evidence of a breach of its own systems, but said a third-party vendor has been hit with ransomware.” Motherboard has verified that a listing naming Ring is currently on ALPHV’s data dump site.
(Vice)
CISA creates new ransomware vulnerability warning program
CISA has announced the creation of a new Ransomware Vulnerability Warning Pilot (RVWP) program. As a follow-up to the Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA), the RVWP will help CISA assess common ransomware exploitation flaws. The Agency will warn critical infrastructure entities so as to assist them with enabling mitigation before an incident. CISA will continue to “rely on various existing services, data sources, technologies and authorities, including its Cyber Hygiene Vulnerability Scanning service.”
Cybercriminals exploit SVB collapse to steal money and data
Threat actors are already registering suspicious domains, conducting phishing pages, and gearing up for business email compromise (BEC) attacks following the collapse of Silicon Valley Bank. Security researcher Johannes Ulrich warned that the scammers might attempt to contact former clients of SVB to offer them a support package, legal services, loans, or other fake services relating to the bank’s collapse. In addition to the domains, many with SVB in them, Ulrich describes an attack already seen in the wild from BEC threat actors impersonating SVB customers and telling customers that they need payments sent to a new bank account after the bank’s collapse. Other scams include informing SVB customers that the bank is distributing USDC a digital stable coin as part of a “payback” program.
Medical device giant says cyberattack leaked sensitive data of 1 million people
Massachusetts based medical device maker ZOLL said a cyberattack in January exposed the sensitive information of more than 1 million people. ZOLL said the incident started on January 28 when they “detected unusual activity” on their internal network, with information being accessed on February 2. “Information that may have been disclosed includes your name, address, date of birth, and Social Security number. It may also be inferred that you used or were considered for use of a ZOLL product,” the company told victims. ZOLL produces a range of devices including defibrillation and monitoring tools as well as devices for circulation and CPR feedback, data management, therapeutic temperature management, and ventilation.
Meta to cut 10,000 jobs in second round of layoffs
This announcement makes Meta the first Big Tech company to announce a second round of mass layoffs as the industry braces for a deep economic downturn. According to Reuters, the cuts are “part of a restructuring that will see the company scrap hiring plans for 5,000 openings, kill off lower-priority projects and flatten layers of middle management.” Meta will also ask managers to become contributors, eliminate non-engineering roles, automate more functions and at potentially reversing its “remote-first” work policy.
(Reuters)
UK’s largest state boarding school announces “sophisticated cyberattack”
Wymondham College is the largest state boarding school in the UK, with 1,200 students aged 11 to 18. On Tuesday it announced it had been hit by a “sophisticated cyberattack”, but did not explain the nature of the attack. This is the latest in a line of attacks on UK-based educational establishment. A spokesperson stated, “We are not aware of any data breach. A number of the College’s systems have been impacted, including access to some files and resources.” No ransom demand has yet been made.
Patch Tuesday update
Yesterday Microsoft announced its March 2023 Patch Tuesday updates, which fix two actively exploited zero-day vulnerabilities and a total of 83 flaws. Nine vulnerabilities have been classified as ‘Critical’ for allowing remote code execution, denial of service, or elevation of privileges attacks, not includin 21 Microsoft Edge vulnerabilities fixed on Monday. The two actively exploited zero-day vulnerabilities fixed in yesterday’s updates are CVE-2023-23397 – Microsoft Outlook Elevation of Privilege Vulnerability, and CVE-2023-24880 – Windows SmartScreen Security Feature Bypass Vulnerability. Other vendors who released updates in March 2023 include: Apple for GarageBand, Cisco for multiple products, Google for Android, ChromeOS, and Google Chrome, Fortinet for the FortiOS vulnerability, SAP and Veeam.