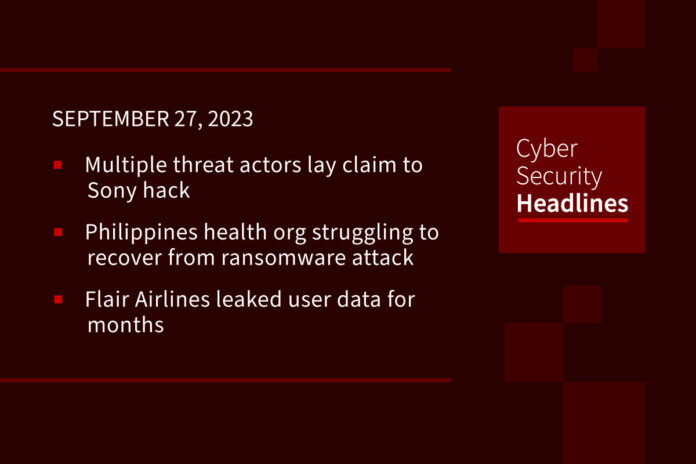
Multiple threat actors lay claim to Sony hack
A threat actor that surfaced last month, RansomedVC (or “Ransomed”), claims they have compromised Sony’s systems and are attempting to sell 260 GB of data for $2.5 million on the Dark Web. However, RansomedVC so far has only published 2 MB including a PowerPoint presentation, some Java source code, and Eclipse IDE screenshots. Meanwhile, another threat actor ‘MajorNelson’ has claimed responsibility for the attack on BreachedForums. MajorNelson has leaked over 3 GB of data, including the data leaked by RansomedVC, but also contains credentials for Sony’s internal systems including SonarQube, Creators Cloud, certificates, license generating emulators and incident response policies. Major Nelson said, “RansomedVCs are scammers who are just trying to scam you and chase influence. Enjoy the leak.” Sony said it is investigating the situation and declined further comment.
(Dark Reading and Bleeping Computer)
Philippines health org struggling to recover from ransomware attack
The Philippines’ universal healthcare system (PhilHealth) is reeling from the effects of a security incident they announced on Friday. PhilHealth’s CEO said Monday that access to member portals and e-claims were taken offline as part of its containment efforts. Members have been forced to pay for benefits over the counter (rather than online) and PhilHealth has added 60 days to the claims filing period. PhilHealth said no personal or medical info was leaked. However, the Medusa ransomware gang, who took credit for the attack, has given PhilHealth 10 days to pay a $300,000 ransom to delete the member data it stole and decrypt the data they encrypted. Law enforcement agencies have been engaged to help investigate the incident.
Canadian Flair Airlines leaked user data for months
Researchers discovered that ultra-low-cost carrier Canadian Flair Airlines exposed customer data for at least seven months. The carrier’s flyflair.com website exposed the site’s environment files containing MySQL database credentials, the carrier’s email account credentials and secret tokens, and app keys. At least one subdomain was collecting private user info including names, emails, phone numbers, and flight details. Researchers issued several notifications about the flaw, including to the Canadian Computer Emergency Response Team (CERT), before the vulnerability was finally resolved.
Microsoft rolls out support for passkeys in Windows 11
On Tuesday, Microsoft officially rolled out support for passkeys in Windows 11 as part of a major update to the desktop operating system. The feature allows users to login to websites and applications using their device PIN or biometric information, without having to provide a username and password. Passkeys are based on FIDO standards and offer a strong and phishing-resistant replacement for passwords. Passkeys have been adopted by Apple, Google, and a number of other services in recent months.
Thanks to our sponsor, AppOmni

What you need is a robust SSPM designed to secure the dynamic and extensible nature of SaaS apps and their data. That’s where AppOmni comes in. We continuously monitor your SaaS estate to detect cyber risks and secure your company’s most critical data and workflows. Get started at AppOmni.com.
EU calls for safeguards to address AI deepfake election risks
On Tuesday, European Union’s Commissioner, Vera Jourova, called for stronger efforts to address the risks AI-generated disinformation may pose to next year’s European Parliament elections. Jourova has called upon mainstream platforms to inform users about the “synthetic origin of content posted online.” The EU’s voluntary anti-disinformation Code currently has 44 signatories including major social media and search platforms as well as advertisers and civil society organizations involved in fact-checking. The EU commissioner planned to meet with ChatGPT maker, OpenAI, later Tuesday to discuss the issue, though the AI giant is not currently a signatory to the Code.
Google assigns new critical CVE to bug exploited in attacks
Google has assigned a new CVE ID to a bug initially disclosed as a Chrome weakness (tracked as CVE-2023-4863) under active exploitation and for which Google issued a patch two weeks ago. Google’s new CVE (CVE-2023-5129) now identifies the bug as a critical heap buffer overflow issue in the WebP library and assigned a maximum severity of 10/10. This update has significant implications for other projects using the open-source library including 1Password, Signal, Safari, Mozilla Firefox, Microsoft Edge, Opera, and native Android web browsers. Organizations must now address the reclassified critical issue across these platforms to ensure the security of user data.
New ZeroFont phishing campaign displays fake AV-scans
A threat actor is using zero-point fonts in emails to make them appear as safely scanned by security tools in Microsoft Outlook. This phishing technique aims to evade security filters by inserting invisible benign terms that mix with suspicious visible content, skewing AI security checks. Although this technique has been used as far back as 2018, the latest phishing campaign observes emails using zero-point fonts to hide invisible bogus security scan messages that display in the email listing pane. Experts warn this technique could make a massive difference in the effectiveness of phishing operations by giving the recipient a false sense of security.
RSA crypto attack is back with the arrival of Marvin
Back in 1998, Daniel Bleichenbacher, a Swiss cryptographer who currently works for Google, showed that a client of an SSL/TLS server could use server error response info to decrypt messages encrypted using RSA’s public-key algorithm. Red Hat engineer, Hubert Kario, has discovered that most implementations of RSA PKCS#1 v1.5 are still vulnerable to his new version of the old attack, which he has named “Marvin” after “the Paranoid Android” from The Hitchhiker’s Guide to the Galaxy. Kario has provided his attack script for those interested in testing their TLS systems.