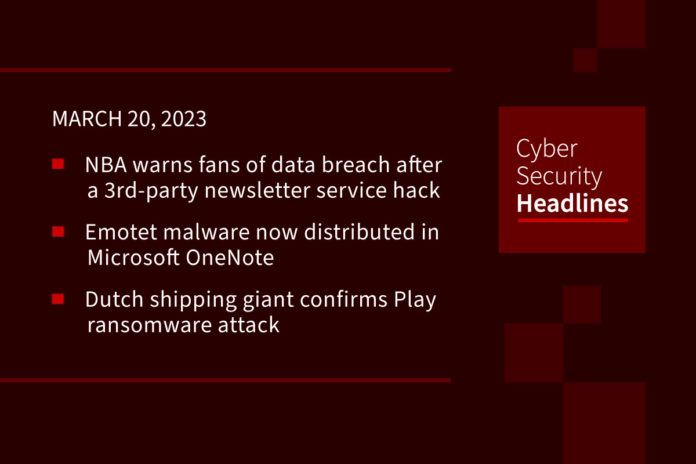
NBA warns of data breach after a third-party newsletter service hack
The NBA has launched an investigation into this security breach to determine the extent of the incident. The association pointed out in a data breach notification sent to the fans that its systems were not impacted, but that the incident affected an unknown number of individuals. The unauthorized third party accessed and created copies of the names and email addresses of some of its fans. The data breach did not compromise usernames, passwords, and other information.
Emotet malware now distributed in Microsoft OneNote
Following up on a story we brought you earlier in the month, it appears that Emotet malware is now being distributed using Microsoft OneNote email attachments, in order to bypass Microsoft security restrictions and infect more targets. “These attachments are being distributed in reply-chain emails that impersonate guides, how-tos, invoices, job references, and more.” Recipients see a message stating that the document is protected, which then prompts them to double-click the ‘View’ button to display the document properly. In this Emotet malware campaign, the threat actors have hidden a malicious VBScript file called ‘click.wsf’ underneath the “View” button.
Dutch shipping giant Royal Dirkzwager confirms ransomware attack
The maritime logistics company has confirmed that the ransomware is from the Play group. This is the latest in number of attacks on the shipping industry. The company’s CEO told The Record the ransomware attack “did not have an effect on operations but did involve the theft of data from servers that held a range of contracts and personal information.” Royal Dirkzwager was founded in 1872 and provides information to more than 800 maritime and shipping organizations. It registers more than 200,000 ship movements a year. “Its systems allow ports to know when ships will arrive and what nautical services will be available when they make it to a port.”
BreachForums mastermind Pompompurin arrested
U.S. law enforcement authorities in New York have arrested Conor Brian Fitzpatrick in connection with running BreachForums hacking forum under the alias Pompompurin. “When arrested in Peekskill, NY, a town about 35 miles north of Manhattan, Fitzpatrick confirmed he was the owner of the alias and was the owner and administrator of ‘BreachForums,'” FBI Special Agent, John Longmire, said. He has been charged with one count of conspiracy to solicit individuals with the purpose of selling unauthorized access devices. He was released a day later on a $300,000 bond signed by his parents and is scheduled to appear before the District Court for the Eastern District of Virginia on March 24.
Thanks to this week’s episode sponsor, Conveyor

Infosec teams have reduced questionnaires by 80% by giving their customers access to our self-serve trust portal to download docs and answers.
For any remaining questionnaires that do come in, use our GPT-Questionnaire Eliminator response tool or white-glove questionnaire completion service to knock them off your to-do list. Use all 3 parts of the platform to solve the questionnaire problem or start with one. Learn more at www.conveyor.com.
Cancer patient sues medical provider after ransomware group posts her photos
The suit, against the Lehigh Valley Health Network, came after hackers posted nude photos of the cancer patient along with her health records. The Lehigh Valley Health Network suffered the attack, identified as being by ALPHV/BlackCat, on Feb. 6, and publicly disclosed that it was the victim of a cyberattack in a Feb. 22 statement posted to the company’s site. The ransomware group demanded payment but the company refused to pay. The suit seeks class action status for all parties whose data was exposed, and monetary damages to be determined later.
MKS Instruments hit with lawsuit following ransomware attack
In a similar story, a former employee of MKS Instruments is filing a class action lawsuit as a result of a ransomware attack against the company that happened in February. The suit alleges that “the company’s negligent cybersecurity led to the unauthorized and unnecessary breach of personal identifying information.” The ransomware attack occurred on February 13. It “impacted business systems and delayed or disrupted the company’s ability to process orders, ship products, and provide other services,” according to comments made by CEO John Lee in a Feb. 28 earnings call. The complaint, filed March 3 in the Orange County Superior Court of California, identifies “John Doe” as a former employee of the company’s Irvine branch office and says that Doe and others “provided personal and medical information to their employer, information that the company said may have been stolen and exfiltrated during the attack.”
Kaspersky releases a new version of Conti decryptor
This new version of a decryption tool for the Conti ransomware is based on previously leaked source code, made available in March 2022, by a Ukrainian security researcher who was protesting the gang’s position on the Ukraine conflict. Kaspersky researchers uncovered a new portion of leaked data in February of this year, published on forums and noticed the presence of 258 private keys. “The leak also included source code and some pre-compiled decryptors, which allowed the researchers to release new version of the public decryptor.” The researchers added all 258 keys to the latest build of Kaspersky’s utility RakhniDecryptor 1.40.0.00. Users can download the decryptor from the Kaspersky’s “No Ransom” site.
Last Week in Ransomware
Damage from the Clop ransomware attacks on GoAnywhere platforms is becoming more apparent. This has led to numerous data breach disclosures from organizations including Community Health Systems (CHS), Hatch Bank, Rubrik, and Hitachi Energy. There were also ransomware attacks on Essendant and the LA housing authority, an attack on Amazon’s Ring doorbell, on a hospital in Barcelona and the re-emergence of IceFire on Linux systems.