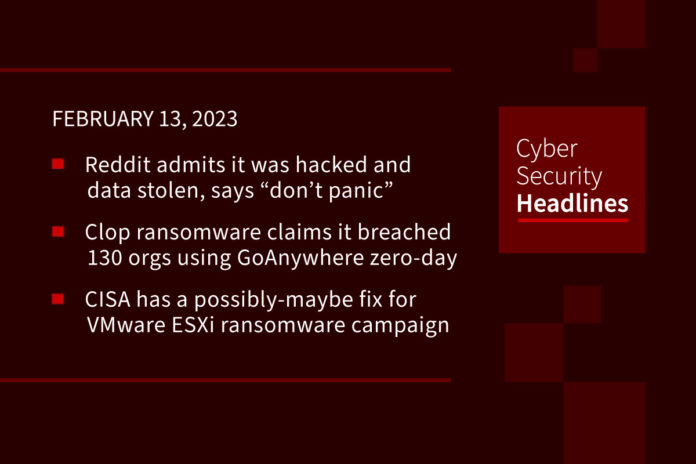
Reddit admits it was hacked and data stolen, says “don’t panic”
Reddit announced Friday that “Reddit systems were hacked as a result of a sophisticated and highly-targeted phishing attack. They gained access to some internal documents, code, and some internal business systems,” although the sophistication involved seemed to be more of an act of stealing employee credentials through a spoofed log-on site. In addition to vague descriptions of docs and some code, Reddit has admitted that information about past and present employees, advertisers and “contacts” was stolen, although they maintain the breach was “limited”.
Clop ransomware claims it breached 130 orgs using GoAnywhere zero-day
Following up on a story we brought you last Monday regarding the Zero-Day in Fortra’s GoAnywhere MFT, the Clop ransomware gang now claims to have stolen the data from over 130 organizations. The gang reached out to BleepingComputer to state that the thefts occurred over ten days. They also claimed that they could now move laterally through their victims’ networks and deploy ransomware payloads to encrypt their systems but decided against it and only stole the documents stored on the compromised GoAnywhere MFT servers. The gang refused to provide proof of the infiltration, the thefts, or any extortion activities, nor has Fortra made any comment.
CISA has a possibly-maybe fix for VMware ESXi ransomware campaign
Following up on another story we brought you last week, CISA released a script last week to help organizations attempting to recover virtual machines affected by a spree of global cyberattacks targeting VMware ESXi servers. However, recent reports indicate that the unknown ransomware hackers have updated the malware to encrypt additional files, making CISA’s script ineffective. According to Censys, a firm that indexes internet-connected devices, there are at least 3,800 hosts compromised with 900 servers with the latest version of hhe malware.
Critical Infrastructure at risk from new vulnerabilities found in wireless IIoT device
Thirty-eight security vulnerabilities have been uncovered in wireless industrial internet of things (IIoT) devices from four different vendors. These could pose a significant attack surface for threat actors looking to exploit operational technology (OT) environments, this according to Israeli industrial cybersecurity company Otorio said. Of the 38 defects, three affect ETIC Telecom’s Remote Access Server (RAS), five other vulnerabilities concern InHand Networks InRouter 302 and InRouter 615. Also identified are two weaknesses in Sierra Wireless AirLink Router.
Thanks to this week’s episode sponsor, CISO Series

Oakland and Modesto hit with ransomware attacks
The City of Oakland has confirmed reports of a ransomware attack that impacted its networks. Officials stated that core functions remained intact, “911, financial data, and fire and emergency resources are not impacted,” although libraries were taken offline. The city of Modesto – about an hour and a half away from Oakland – was also dealing with a citywide ransomware attack that forced the police department to revert back to radios.
6 Hacker develops new ‘Screenshotter’ malware to find high-value targets
A threat actor being tracked as TA886 is targeting organizations in the United States and Germany and is using new custom malware to “perform surveillance and data theft on infected systems.” First discovered by Proofpoint in October 2022, the threat actor appears to have financial motivations, performing a preliminary evaluation of breached systems to determine if the target is valuable enough for further intrusion. They then use phishing emails that include Microsoft Publisher (.pub) attachments with malicious macros, URLs linking to .pub files with macros, or PDFs containing URLs that download malicious JavaScript files.
Embarrassment as US cyber ambassador’s Twitter account is hacked
Top US cyber diplomat Nate Fick, the inaugural US ambassador at large for Cyberspace and Digital Policy, announced last week the hack of his personal Twitter account, not the government agency one. The State Department did not immediately respond to questions about who was responsible for the attack, or how they accessed Fick’s account. Twitter also did not respond to inquiries about whether this account breach was related to the recent online dumps of Twitter users’ data.
Last week in ransomware
As mentioned earlier in this episode, the worldwide ESXiArgs ransomware attacks continued to plague VMware ESXi servers which additionally led to the Linux encryptor for the Royal Ransomware group developing its own Linux encrypt for virtual machines. The U.S. government sanctioned seven TrickBot/Conti cybercrime organization members and released a report detailing how North Korean ransomware attacks are used to fund the its operations. Canada’s Indigo book store chain, and A10 Networks confirmed they suffered a data breach after a Play ransomware attack, and British steelmaker Vesuvius PLC also announced an attack.
(Bleeping Computer and CISO Series)