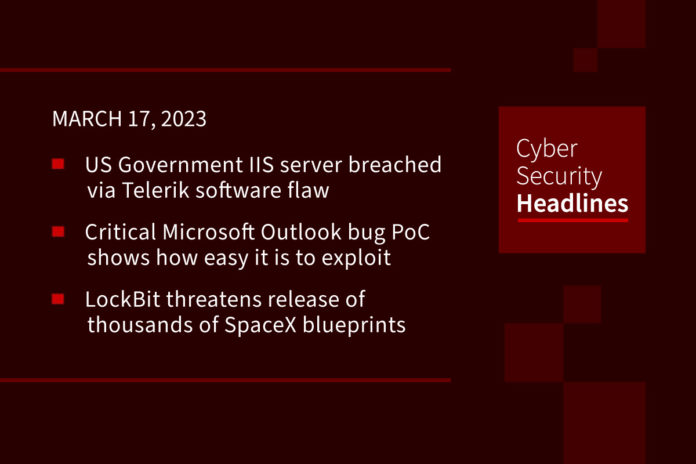
US Government IIS server breached via Telerik software flaw
According to InfoSecurity Magazine, “CISA has disclosed information regarding a .NET deserialization vulnerability (CVE-2019-18935) in the Progress Telerik user interface (UI) for ASP.NET AJAX.” The discovery was communicated via an advisory on Wednesday, and it stated that saying “multiple cyber-threat actors were able to exploit the flaw, which also affects the Microsoft Internet Information Services (IIS) web server of a federal civilian executive branch (FCEB) agency between November 2022 and January 2023.” This flaw has been given a CVSS score of 9.8 owing to the fact that it allows remote code execution (RCE) if exploited successfully.
Critical Microsoft Outlook bug PoC reveals exploit potential
Researchers revealed details on how to exploit a vulnerability in Microsoft Outlook vulnerability for Windows (CVE-2023-23397) that could enable threat actors to steal hashed passwords by simply sending an email. Microsoft has released a patch for the security flaw Bleeping Computer states “it has been exploited as a zero-day vulnerability in NTLM-relay attacks since at least mid-April 2022”. The issue, which has a 9.8 severity rating affects all versions of Microsoft Outlook on Windows. No user interaction is needed following receipt of the email, since “exploitation occurs when Outlook is open and the reminder is triggered on the system.”
LockBit threatens release of thousands of SpaceX blueprints
The LockBit ransomware gang claims it has broken into systems belonging to Maximum Industries, a supplier company to SpaceX, and has stolen 3,000 proprietary schematics. The group threatened to leak or sell the blueprints on March 20. As for the validity of this threat, The Register points out that LockBit is famous for claiming breaches that it hasn’t actually done, such as ION and possibly the UK’s Royal Mail.
Prometei botnet evolves – has infected +10,000 systems since November
According to researchers at Cisco Talos, the Prometei botnet has now infected more than 10,000 systems worldwide since November. This is a crypto-mining botnet with a modular structure that uses numerous techniques to infect systems and evade detection. It was first observed by Cisco Talos experts in July 2020. An investigation of artifacts uploaded to VirusTotal helped date botnet’s activity back to May 2016. Talos has confirmed that the botnet “continues to improve modules and exhibits new capabilities in recent updates.”
Chinese and Russian hackers using stealthy SILKLOADER
Groups associated with Chinese and Russian cybercrime organizations have been observed using malware that can load Cobalt Strike onto infected machines. The Finnish cybersecurity company WithSecure has named the malware SILKLOADER and points out that it uses DLL side-loading techniques to deliver its payload which is commercial adversary simulation software. It is thought that this new technique is a result of improved detection capabilities against Cobalt Strike.
Senators ask CISA to examine Chinese consumer drones
A bipartisan group of senators wants CISA to look deeper into consumer drones made by a company that has “deep ties” to the Chinese Communist Party. The senators warn that these drones could be used to spy on U.S. critical infrastructure. The use of drones is quickly expanding to serve “everything from food delivery to emergency services.” Senators Mark Warner (D-VA) and Marsha Blackburn (R-TN) said CISA needs to step in and “reevaluate the risks associated” with drones built by Shenzhen DJI Innovation Technology – a company they accuse of having links to China’s government. A CISA spokesperson said the agency “will not comment on the letter publicly and plans to respond directly to the senators.”
Healthcare software firm ILS announces data breach affecting more than 4 million people
Hackers broke into the network of Independent Living Systems (ILS), a healthcare software company based in Miami, and stole healthcare data of more than four million people. According to The Record, ILS provides “third-party administrative services to health plans, providers, hospitals, and pharmaceutical and medical device companies” and has done so for nearly two decades. ILS started sending breach notification letters out on Tuesday following the July 5, 2022 cyberattack. The information includes names, addresses, dates of birth, driver’s license numbers, Social Security numbers, financial account information and medical data such as diagnosis codes and health insurance information.
Microsoft 365 Copilot assistant is announced
CoPilot is an assistant powered by artificial intelligence designed to “help boost productivity across Microsoft 365 apps,” and is currently being tested by select commercial customers. Its role is to help create and manage documents, presentations, and spreadsheets, as well as triage and reply to emails. Using the GPT-4 large multimodal model, Copilot will be installed in all Microsoft 365 apps, from Word, Excel, PowerPoint, Outlook, and Teams to Microsoft Viva and Power Platform. Similar to the new Bing Chat, it also works like a chatbot, enabling users to generate content based on prompts exchanged via an interface.