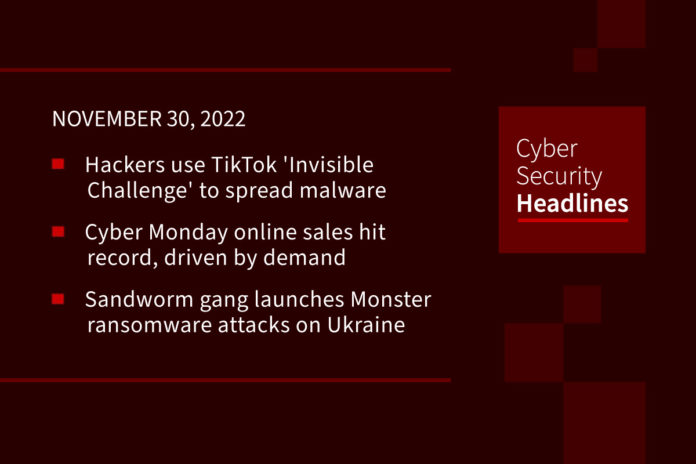
Hackers use trending TikTok ‘Invisible Challenge’ to spread malware
Threat actors are capitalizing on a popular TikTok challenge to trick users into downloading information-stealing malware, according to new research from Checkmarx. The scheme is based on a trend called Invisible Challenge, which involves applying a filter known as Invisible Body that just leaves behind a silhouette of the person’s body. This has led to a demand for an unfilter that would allow viewer to see the person within the silhouette. Attackers are now posting TikTok videos with links to rogue software dubbed “unfilter” that purports to remove the applied silhouette. This software deploys WASP stealer malware hiding inside malicious Python packages, and is designed to steal users’ passwords, Discord accounts, cryptocurrency wallets, and other sensitive information.
Cyber Monday online sales hit record
Although Expectations for this year’s holiday online spend were lukewarm, Cyber Monday pulled in $11.3 billion in sales online according to figures from Adobe Analytics, which tracks seasonal e-commerce activity. This is 5.8% more than consumers spent on the same day last year, and sets a record both for the day and the year so far. This is despite the fears of inflation potentially dampening consumers’ spirits. Adobe said that these figures were based on more transactions overall, and points to retailers’ deep discounts paired with greater availability of goods after shortages of the years before.
Sandworm gang launches Monster ransomware attacks on Ukraine
The Russian criminal crew Sandworm is launching another attack against organizations in Ukraine, using a ransomware that analysts at Slovakian software company ESET are calling RansomBoggs. In a Twitter thread, the ESET researchers wrote that they had detected RansomBoggs deployed within the networks of “multiple organizations in Ukraine.” While some aspects of RansomBoggs are different from the malware that has been linked to Sandworm – such as the malware’s code being written in .NET – the deployment methods are similar to the one seen last April during the Industroyer2 attacks against the energy sector.”
North Carolina college confirms ransomware group stole sensitive data
Guilford College in North Carolina has confirmed that ransomware actors who attacked their school also stole sensitive data of students, faculty and staff. A spokesperson for the 185-year-old college said the attack occurred in October. “While our investigation remains ongoing, we do have evidence to suggest the unauthorized actor responsible for this incident may have illegally accessed sensitive data,” the spokesperson said. On Friday, the Hive ransomware group took credit for the attack and threatened to leak the data stolen, posting samples of what was taken on October 21.
Thanks to this week’s episode sponsor, Automox

Microsoft Defender boosts default tamper protection for all enterprise users
Microsoft has announced that built-in protection is generally available for all devices onboarded to Defender for Endpoint, the company’s endpoint security platform. Once applied, this default set of settings provides better protection for enterprise endpoints against advanced and emerging threats, including ransomware attacks. Microsoft stated, “initially, built-in protection will include turning tamper protection on for your tenant, with other default settings coming soon,” This announcement comes after the company began to toggle on tamper protection for all new customers with Defender for Endpoint Plan 2 or Microsoft 365 E5 licenses starting last year.
Twitter users’ stolen data leaked online — more shared privately
Over 5.4 million Twitter user records containing non-public information stolen using an API vulnerability that was fixed in January, have been shared for free on a hacker forum. Another massive, potentially more significant, data dump of millions of Twitter records has also been disclosed by a security researcher, demonstrating how widely abused this bug was by threat actors. The data consists of scraped public information as well as private phone numbers and email addresses that are not meant to be public. This data was collected in December 2021 using a Twitter API vulnerability disclosed in the HackerOne bug bounty program that allowed people to submit phone numbers and email addresses into the API to retrieve the associated Twitter ID. This is an expansion part of an ongoing exploit by the hacker known as Pompompurin who initially offered Twitter user records for sale in July, and is now stating that this second data dump was not sold and was only shared privately among a few people.
Wave of cyber-enabled scams target FIFA World Cup fans
As the global soccer tournament enters its second full week in Qatar, FIFA World Cup scams are proliferating as cybercriminals aim to score big from unsuspecting fans, according to data collected by cybersecurity firm Group-IB. Researchers said Tuesday they’ve identified as many as 90 potentially compromised Hayya accounts, which is the mandatory system established so World Cup attendees can enter Qatar and access tickets and other services such as transportation. They have also observed the attackers using info-stealing malware such as Redline and Erbium, fake merchandise and ticket websites used to steal money directly or swipe banking credentials, 40 fake apps in the Google Play Store promising access to tickets, and at least five websites purporting to be job application forms used to harvest personal information.
Irish regulator fines Facebook for leak of users’ data
Ireland’s Data Protection Commission (DPC) has levied fines of €265 million ($277 million) against Meta Platforms for failing to safeguard the personal data of more than half a billion users of its Facebook service, ramping up privacy enforcement against U.S. tech firms. The fines follow an inquiry initiated by the European regulator on April 14, 2021, close on the heels of a leak of a “collated dataset of Facebook personal data that had been made available on the internet.” Meta acknowledged that the information was “old data” that was obtained by malicious actors by taking advantage of a technique called “phone number enumeration” to scrape users’ public profiles. This entailed misusing a tool called “Contact Importer” to upload a huge list of phone numbers to uncover matches.