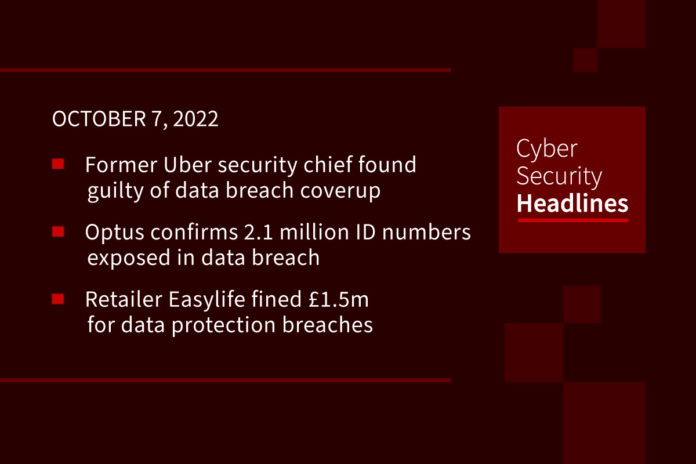
Former Uber security chief found guilty of data breach coverup
A U.S. federal court jury has found former Uber Chief Security Officer Joseph Sullivan guilty of not disclosing a 2016 breach of customer and driver records to regulators and attempting to cover up the incident. Sullivan has been convicted on two counts: One for obstructing justice by not reporting the incident and another for misprision. He faces a maximum of five years in prison for the obstruction charge, and a maximum of three years for the latter. The 2016 hack of Uber occurred as a result of two hackers gaining unauthorized access to the company’s database backups, prompting the ride-hailing firm to secretly pay a $100,000 ransom in December 2016 in exchange for deleting the stolen information.
Optus confirms 2.1 million ID numbers exposed in data breach
Optus confirmed yesterday that 2.1 million customers had government identification numbers compromised during a cyberattack last month. Of these, 1.2 million had at least one number from a current and valid form of identification compromised, and 900,000 had ID numbers exposed but from documents that are now expired. This has not changed the original number of affected customers – all 9.8 million customers had other personal information exposed, including email addresses, date of birth, or phone numbers.
Retailer Easylife fined £1.5m for data protection breaches
A leading UK catalog retailer has been issued with a financial penalty of close to £1.5m by the country’s information regulator for breaching data protection and marketing laws. The Information Commissioner’s Office (ICO) said that Easylife used the personal information of its customers to target them with health-related products without their consent. The firm claims to be one of the largest home and garden retailers of its kind in the UK, although it also sells products and services related to health and automotive. The ICO explained that 80 out of 122 products in Easylife’s Health Club catalog, were considered to be “trigger products” which, if bought, would lead to the firm profiling the customer and targeting them with follow-on calls and emails.
Australian Federal Police arrest man suspected of exploiting Optus cyberattack
Aussie police have arrested a 19-year-old Sydney resident accused of trying to extort money from victims of the recent cyberattack and digital burglary at national telecommunications provider Optus. The Australian Federal Police (AFP) said it was alerted to the blackmail attempt when some Optus customers were told to transfer AU$2,000 ($1,300) to a bank account or have their personal data used for financial crimes. The unnamed individual is alleged to have used 10,200 of the records on customers that were uploaded to the web following the attack in September, including names, dates of birth, phone numbers, email addresses, home addresses, driving licenses, and passports.
And now thanks to this week’s episode sponsor, Hunters

“Egypt Leaks” – hacktivists are leaking financial data
Resecurity, a California-based cybersecurity company protecting Fortune 500 corporations globally, has noticed a new group of hacktivists targeting financial institutions in Egypt. The bad actors go under the campaign “EG Leaks” (also known as “Egypt Leaks”), they started leaking large volumes of compromised payment data belonging to the customers of major Egyptian banks on the Dark Web. First mention of this activity have been detected in a Telegram channel created to leak Excel files containing 12,229 credit cards.
Japanese sushi chain boss resigns amid accusation of improper data access
The president of casual Japanese chain restaurant Kappa Sushi resigned yesterday in the wake of a data-theft scandal. Kobi Tanabe was arrested by the Tokyo Metropolitan Police Department on September 30 on allegations of violating Japan’s competition laws. Before he became boss of Kappa Sushi, Tanabe led rival discount sushi establishment Hama Sushi – which has accused Tanabe of stealing trade secrets by accessing data caches. As the former director of Hama Sushi, Tanabe had contacts, including former subordinates, who allegedly emailed him daily sales data on several occasions.
Ferrari denies data breach and ransomware attack following gang’s online claims
Luxury car maker Ferrari is denying that it was hit with a ransomware attack after a gang added the company to its list of victims this week. The ransomware group RansomEXX posted to its leak site on Sunday claiming to have stolen 7 GB of data from the company. The stolen documents allegedly include contracts, invoices, internal company information, repair manuals and more. But in a statement to The Record on Tuesday, a Ferrari spokesperson said it was aware of reports that documents from the company have been leaked online but said it is not dealing with any kind of ransomware attack or cybersecurity incident. The RansomEXX listing did not include a specific ransom demand or details about how they allegedly attacked the company.
Intel inching closer to mass production of spin qubit chips
Intel claims to have achieved a milestone in efforts to produce silicon spin qubit devices using existing manufacturing processes, a move they think might pave the way for large-scale production of quantum computers. They describe this as “the industry’s highest” yield and uniformity for silicon spin qubit hardware. Intel’s quantum angle has been on scaling up the process to fabricate quantum processor chips using its own transistor manufacturing techniques, which have been tuned for large-scale production over many decades. The latest research was conducted using Intel’s second-generation silicon spin test chip, developed at their transistor research and development facility, Gordon Moore Park at Ronler Acres in Hillsboro, Oregon.