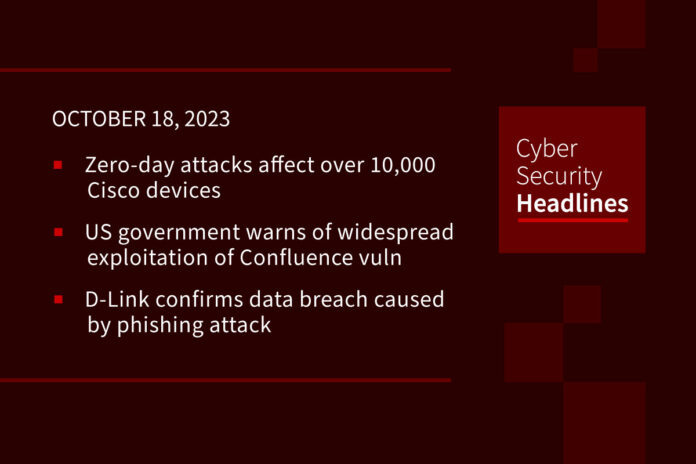
Zero-day attacks affect over 10,000 Cisco devices
Researchers have discovered attackers are exploiting a recently disclosed critical zero-day bug (CVE-2023-20198) affecting at least 10,000 Cisco IOS XE devices including enterprise switches, routers, access points, and wireless controllers. The maximum severity vulnerability targets devices with the Web User Interface (Web UI) enabled and that also have HTTP or HTTPS Server toggled on. Researchers at VulnCheck say that privileged access on the IOS XE could allow attackers to monitor network traffic, pivot to protected networks, and perform man-in-the-middle attacks. While a patch is not available, administrators should immediately disable the web interface, remove management interfaces from the internet, and check for suspicious user accounts.
US government warns of widespread exploitation of Confluence vulnerability
Following up on a story we’ve been covering on Cyber Security Headlines over the past two weeks, CISA, the FBI, and the Multi-State Information Sharing and Analysis Center (MS-ISAC) are warning of potential widespread exploitation of a zero-day vulnerability in on-premises instances of Atlassian Confluence Data Center and Server (tracked as CVE-2023-22515 with a CVSS score of 9.8). The bug has been exploited by Chinese nation-state threat actors since September 14, roughly two weeks before Atlassian released fixes. The bug is remotely exploitable without authentication and could lead to privilege escalation. The advisory further warns that successful exploitation could lead to threat actors creating additional unauthorized administrative accounts.
D-Link confirms data breach caused by phishing attack
The Taiwanese networking equipment manufacturer, D-Link, confirmed it suffered a data breach resulting from an employee falling victim to a phishing attack. In response, D-Link immediately shut down potentially impacted servers and disabled all but two user accounts used during the investigation. The attacker claims to have stolen source code for D-Link’s D-View network management software, along with millions of personal info entries belonging tof customers, employees, government officials, and the company’s CEO. The stolen data allegedly includes names, emails, addresses, phone numbers, account registration dates, and the users’ last sign-in dates. The threat actor is seeking $500 for the stolen data despite the fact that timestamps reveal the info may date back to between 2012 and 2013.
Meta now lets Instagram users stop online data collection
Meta says it has expanded the ability of Instagram users to block data collection across the apps and websites they visit. This blocking was already a feature in Facebook, and will allow users to review which businesses share info with Meta, disconnect specific activity, or clear collected information. Instagram users can find this feature, called Activity Off-Meta Technologies, within the platform’s Accounts Center.
Huge thanks to our sponsor, Vanta

Vanta’s market-leading trust management platform brings GRC and security efforts together. Integrate information from multiple systems and reduce risks to your business and your brand — all without the need for additional staffing.
And by automating up to 90% of the work for SOC 2, ISO 27001, and more, you’ll be able to focus on strategy and security, not maintaining compliance.
Join 5,000 fast-growing companies that leverage Vanta to manage risk and prove security in real-time. Our listeners get $1,000 off Vanta. Go to vanta.com/ciso to claim this discount.
Malicious Notepad++ Google ads evade detection for months
Threat actors have been abusing Google Ads in a months-long malvertizing campaign targeting users looking to download the popular Notepad++ text editor. The campaign’s URLs filter out crawlers, VPNs, and bots, eventually landing victims in a site that contains decoy download links for the text editor. Upon clicking on those links, a second check is performed to ensure the visitor is not protected by a sandbox. Victims who are deemed suitable targets are served a script which researchers found not to be weaponized. However, they identified a prior version of the same file that attempted to connect to a remote domain on a custom port they believe is part of a Cobalt Strike deployment. To protect themselves, users should skip promoted results on Google Search and double-check they’ve landed on an official domain.
UAE, US partner to bolster financial services cybersecurity
During the Gitex Global Conference in Dubai, Dr. Mohamad Al Kuwaiti, head of cybersecurity for the UAE government, met with Todd Conklin, deputy assistant secretary of the Treasury, and agreed to cooperate in multiple areas. These areas included sharing cybersecurity incident and threat info, staff training and study visits, and conducting cross-border cybersecurity exercises. This effort is part of the US Treasury’s collaborative approach to improving cybersecurity for the international financial system through public-private partnerships and developing relationships with international partners.
Fake browser updates used for malware distribution
Cybersecurity researchers from Proofpoint are tracking at least four distinct threat clusters mimicking fake updates for popular browsers like Chrome, Firefox and Edge. Proofpoint said the threat actor, TA569, has been using the tactic for over five years to deliver malware called SocGholish while more threat actors have since adopted the strategy. The attack is stealthy and uses three stages starting by deploying JavaScript or HTML-injected code on a compromised website, then directing traffic to actor-controlled domains before finally executing the payload on the user’s device. The campaign’s success lies in exploiting users’ trust in known and safe sites. Proofpoint says the attack underscores the need for robust security controls including network detection, security awareness training and incident reporting procedures.
Tech CEO sentenced to 5 years in IP address scheme
Amir Golestan, the 40-year-old CEO of the Charleston, SC-based technology company Micfo LLC, has been sentenced after pleading guilty to an elaborate IP address scheme. Golestan used a network of phony companies to secure more than 735,000 Internet Protocol (IP) addresses from the American Registry for Internet Numbers (ARIN). ARIN sued Golestan and Micfo back in 2018 for obtaining the IP addresses under false pretenses. While that dispute was settled in arbitration, federal prosecutors in South Carolina took notice, filing criminal wire fraud charges against Golestan in May 2019. The US Department of Justice (DoJ) says Golestan will serve 60 months in prison and pay ARIN nearly $77,000 in restitution, followed by a 2-year term of court-ordered supervision.