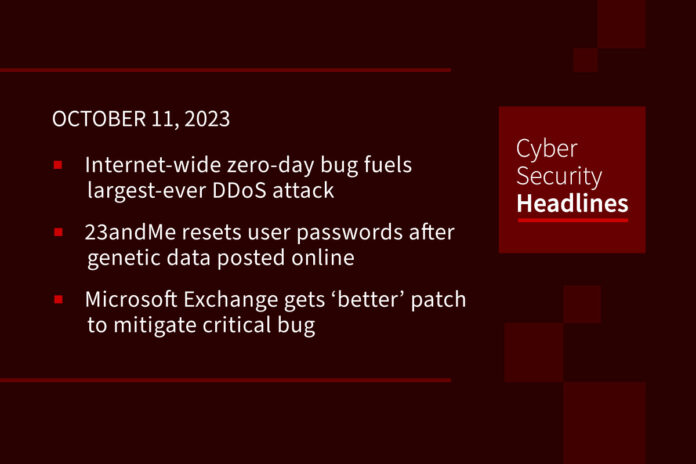
Internet-wide zero-day bug fuels largest-ever DDoS attack
An Internet-wide zero-day vulnerability is to blame for a record-breaking distributed denial-of-service (DDoS) attack dubbed “HTTP/2 Rapid Reset” (CVE-2023-44487). Amazon Web Services, Cloudflare, and Google Cloud each observed the just-minutes-long attack on August 28 and 29, with Google recording a peak of 398 million requests per second (rps), seven and a half times larger than any previous attack against its resources. The providers partnered with DDoS security, and infrastructure vendors to minimize the effects of the attacks, mainly through load balancing and other edge strategies. The exploited protocol, HTTP/2, enables browsers to quickly view website images and text and the protocol is used by roughly 60% of all Web applications. Many organizations will remain exposed to the attack until they patch their HTTP/2 instances.
(Dark Reading and CyberScoop)
23andMe resets user passwords after genetic data posted online
Following up on a story Cyber Security Headlines brought to you on Monday, genetic testing company 23andMe said it’s requiring users to reset their passwords “out of caution.” The company said that hackers accessed accounts using passwords that were made public in previous data breaches. Beginning last Wednesday, hackers began advertising alleged 23andMe user data on BreachForums, offering individual profiles for between $1 to $10 each. According to 23andMe, the data was “compiled” from users that had opted into a feature to automatically share their data with others. Theoretically, this would allow a hacker to access more than one victim’s account for every account they broke into.
Microsoft Exchange gets ‘better’ patch to mitigate critical bug
The Exchange Team asked admins to deploy a “better” patch for a security flaw (CVE-2023-21709) that enables unauthenticated attackers to escalate privileges on unpatched Exchange servers in low-complexity attacks without the need for user interaction. Although Microsoft issued an initial patch during its August 2023 Patch Tuesday, admins also needed to manually remove the vulnerable Windows IIS Token Cache modules or run an additional PowerShell script to protect their servers. As part of the October patch Tuesday, Microsoft has released a new security update (CVE-2023-36434) that fully addresses the original flaw without requiring any additional procedures.
Microsoft to kill off VBScript in Windows to block malware delivery
After 27 years of use, Microsoft is planning to phase out Visual Basic Script (or ‘VBScript’) in future Windows releases. The VBScript programming language was introduced back in August 1996 and was bundled with Internet Explorer until the browser was deprecated by Microsoft earlier this year. Malicious actors have used VBScript to distribute malware, including notorious strains like Lokibot, Emotet, Qbot, and DarkGate. Over the past several years, Microsoft has taken measures to curb attacks on VBA macros and disabled VBScript by default in Internet Explorer 11 on Windows 10. Microsoft will continue making VBScript an on-demand feature until it is sunset.
Huge thanks to our sponsor, Hyperproof

One-click exploit could pose serious threat to Linux systems
GitHub’s Security Lab has warned Linux users about a serious remote code execution vulnerability (tracked as CVE-2023-43641) affecting a component of the popular GNOME desktop environment. The flaw was found in a library called Libcue which is used by a search engine called Tracker Miners, which GNOME uses to increase file search efficiency. Researchers released a video demonstrating a one-click exploit for Ubuntu and Fedora Linux distros and noted that all distributions running GNOME could be vulnerable. The researchers publicly released a simple version of the PoC, which only causes benign system crashes, so users can check their systems. Researchers say they won’t release a fully weaponized exploit until users have had a chance to install the patch.
DDoS malware variant expands targets with 13 router exploits
A Mirai-based DDoS (distributed denial of service) malware botnet tracked as IZ1H9 has added thirteen new payloads to target Linux-based routers and routers from manufacturers including D-Link, Zyxel, TP-Link, and TOTOLINK. Researchers report observing peak exploitation rates in early September, attacking nearly 30 CVEs across vulnerable devices. After exploiting one of theCVEs, an IZ1H9 payload fetches and executes a script that deletes activity logs before connecting to bot clients tailored for different system architectures. The script then modifies the device’s iptables rules to obstruct connections and make it harder to remove the malware. Finally the malware establishes communication with the C2 (command and control) server and waits for commands to execute.
You should probably patch that (Patch Tuesday edition)
Yesterday, Microsoft pushed its October 2023 Patch Tuesday security fixes to address more than 100 vulnerabilities across the Windows ecosystem including three flaws already being exploited in the wild. As part of the fixes, Microsoft joined tech giants AWS, Google and Cloudflare to address the ‘HTTP/2 Rapid Reset’ zero-day DDoS flaw. Additionally Microsoft addressed a pair of zero-days in Microsoft WordPad (CVE-2023-36563) and Skype for Business (CVE-2023-4176) which respectively allow for disclosure of NTLM hashes and privilege escalation.
Additionally, Adobe joined in by documenting 10 serious flaws across Photoshop, Adobe Commerce and Magento Open Source. Exploitation of the flaws could lead to arbitrary code execution, privilege escalation, arbitrary file system read, security feature bypass and application denial-of-service.
SAP also got in on the patching frenzy, with its most severe security fixes addressing 37 bugs in the Chromium browser in SAP Business Client, including two critical and 20 high-severity vulnerabilities.
(SecurityWeek[1][2][3] and Bleeping Computer)
Damage to undersea cable and gas pipeline caused by ‘external activity’
On Tuesday, Finnish officials say that damage to an undersea gas pipeline and telecommunications cable connecting Finland and Estonia appears to have been caused by “external activity.” On Sunday, Finnish and Estonian system operators shut off the flow of gas to the Balticconnector pipeline after detecting an unusual drop in pressure. Finnish Prime Minister Petteri Orpo stopped short of calling the pipeline leak sabotage but said it could not have been caused by regular operations. Officials say they are taking the incident seriously as they continue to investigate the cause.
(AP News)